At RSAC 2026, we wanted to do something new. Rather than just hanging around a booth and talking to people who could physically make it to San Francisco, we launched runZero Day, a live, multi-hour broadcast that brought the best of the conference experience to the global security community. No travel needed! We brought together founders, journalists, and security leaders to unpack the trends shaping and defining cybersecurity in real time.
If you missed the livestream, here’s a quick look at the themes and sessions from the day hosted by runZero’s Tod Beardsley and Rob King.

The vulnerability crisis: Quality, prediction, and noise #
Right now, the industry is overwhelmed by a flood of CVEs, and we’re pretty sure this is just the beginning of a pretty steep slope. With vulnerability disclosures at an all-time high, the debate over quality versus quantity is more important than ever. In the ‘CVE quagmire’ segment, Jerry Gamblin (RogoLabs) told Tod that we’re facing an average of more than 160 new CVEs per day. He highlighted that while we’re hearing a lot about the potential for an artificial intelligence (AI) tsunami of bugs, we still haven’t addressed people-generated bugs and the inconsistent metadata that have hindered security teams for decades. On a positive note, they discussed how projects like RogoLabs’ CVE.ICU is making the CVE program more transparent, and how the upcoming Schema 6.0 could also help by requiring better, machine-readable data for automated discovery and fixes.
Next, we had the perfect follow-up session, ‘Predicting exploitation’with Jay Jacobs (Empirical Security), exploring the practice of predicting vulnerability exploitation. Jacobs detailed the evolution of the Exploit Prediction Scoring System (EPSS) from a research initiative into a vital, daily-published API that provides probability scores and percentile rankings for hundreds of thousands of CVEs.
They discussed how EPSS differs from other scoring systems and frameworks, specifically explaining the relationship between a probability score and the percentile rank. Jacobs also addressed common misconceptions about low-probability scores, noting that even a small percentage can be highly significant when measured across a massive population of vulnerabilities.
Rounding out our discussions on CVEs was the 'Mute the sirens' session with Mark Lambert (ArmorCode). Given the increasing volume and velocity of vulnerabilities, Lambert explains how an important step in reducing the noise includes determining what actually needs to be fixed, and it’s not just about picking the critical ones. He noted that they leverage threat intelligence from CISA’s KEV and EPSS to determine what’s being actively exploited, which is particularly important given that nearly all CVEs are never actually exploited in the real world.
Then, they further analyze this vulnerability intelligence by using integrations with other solutions to get an inventory of assets, determine what’s externally facing, and understand if a fix is urgently needed from a business-priority perspective. Using this unified exposure management approach goes beyond focusing only on traditional CVEs to include issues found through penetration testing and static analysis, providing a comprehensive picture of an organization’s security posture.
Research-driven reporting in cybersecurity journalism #
With more AI-generated content and smaller newsrooms, cybersecurity journalism faces new challenges. In the 'Signal vs. slop' session, current and former reporters discussed how research-driven reporting is changing. Our panel of experts included Bill Brenner (CYBR.SEC.Media), Dennis Fisher (Decipher), and Steve Ragan (1Password).
The group discussed how reduced funding for traditional media has pushed many journalists to work for and with vendors directly, where brand journalism now fills the gap left by shrinking newsrooms, creating challenges for editorial independence amid the pressures of advertising and sponsored content. They also reflected on how large language models (LLMs) are affecting the quality of security reporting and how the rise of automated content lacks the human insight needed for good communication.
Expanding on the cybersecurity journalist’s perspective, the 'On the frontlines of investigative journalism' session with investigative journalist and author Joseph Menn examined the intersection of technology, crime, geopolitics, and hacktivism.
Menn shared with Tod that today’s most interesting stories aren’t just about business deals or stock prices; they focus on the complex areas where organized crime groups and state-sponsored intelligence operations overlap, especially in places like Russia and China.
They also discussed Menn’s book, Cult of the Dead Cow. They talked about the group's role in pressuring tech giants like Microsoft to take security seriously, effectively shifting the industry from a culture of hobbyist tinkering to one of professionalized defense and public policy influence.
Bridging the physical and digital divide #

In the 'From risk to resilience' session, Mary Gannon (GuidePoint Security) and Patrick Gillespie (GuidePoint Security) talked with Rob about how IT and Operational Technology (OT) are converging. They discussed the unique challenges of securing industrial systems in sectors such as manufacturing and mining, where older software like Windows 98 and even Windows 3.1 is still in use. They pointed out that while bringing IT and OT together offers benefits such as real-time data and remote work, it also poses serious safety risks.
One key takeaway is the importance of knowing what assets are on your network. Many OT organizations don’t have a clear picture of what’s connected, often because the security teams don’t actually own the physical equipment. They explained that in OT, the priorities are different: IT cares most about keeping data private, while OT focuses on safety and keeping systems running. That’s why things like immediate patching aren’t always possible — shutting down a system could put people’s lives at risk.
This shift from physical assets to decentralized systems is also redefining the very concept of a network perimeter. In the ‘Perimeters and pathways’ session with Jared Atkinson (SpecterOps), Zakir Durumeric (Censys), and HD Moore (runZero), our experts stressed that the idea of a single, clear network perimeter is outdated, replaced by a satellite model of thousands of cloud accounts, remote control systems, and data-sovereignty-compliant providers. They also pointed out that network infrastructure, like firewalls, VPNs, and LTE modems, is now a top target for initial access, blurring the line between internal and external assets.
They discussed the pathways attackers take once they gain initial access, and how defenders can use solutions to map identity-based attack paths through systems. The conversation also noted that fingerprinting internal TLS services and searching for matching hashes on the public internet reveals hidden connections and misconfigurations, such as management ports exposed to guest wireless networks that completely bypass intended segmentation.
And this is especially risky at ‘The network edge,’ where old hardware like routers that no longer get updates are easy targets for attackers. During this session, Kimber Duke (VulnCheck) and Patrick Garrity (VulnCheck) discussed the critical intersection of end-of-life (EOL) hardware and this notion of a porous network edge with Tod.
Our experts revealed that edge devices, such as consumer routers and firewalls, are some of the most targeted assets for exploitation. They also talked about the zombie cycle of the internet, where unpatched, unsupported devices remain online indefinitely, creating a massive, static attack surface. Unfortunately, this problem is exacerbated by Internet Service Providers (ISPs) that continue to issue EOL hardware to new customers as well as the lack of consumer awareness regarding router updates.
As the conversation shifted to AI, our experts noted that they’re seeing a mix of valid bugs and ‘AI slop,’ and they anticipate the volume of valid vulnerabilities to increase geometrically over time.
The AI frontier: Bounties and asymmetric defense #
And speaking of AI (which is nearly impossible to avoid in San Francisco, it turns out), it was also a focus in several sessions, including the discussion Tod had with Casey Ellis (Bugcrowd) about ‘Bug bounties in the age of AI.’ They talked about how AI is making it easier for both attackers and defenders, but that the primary drivers of security research still depend on human intent and quick decision-making. They also discussed the challenge of the 'defender's dilemma,' where attackers can try new things quickly and with little risk, while defenders must secure entire environments and face severe operational consequences if their automated 'agents' cause a production outage.
As the session continued, Ellis stressed the importance of vulnerability research and the need to standardize disclosure practices, which is why he’s focusing on disclose.io to make vulnerability disclosure and vulnerability report acceptance easier through standardized legal templates and a vendor-neutral database of disclosure policies.

As noted earlier, we weren’t done with AI yet. 'The infinite eye' segment with Jonathan Cran (Mallory) and HD Moore (runZero) talked with Tod about how AI-powered threat intelligence is giving defenders a real edge in a noisy security landscape. The conversation highlights a major shift in vulnerability management; defenders are transitioning away from waiting for official CVE numbers to tracking emerging threats through GitHub issues, mailing lists, and security advisories. By being more intentional about embracing the strengths of LLMs to filter out slop and fake exploits, defenders can answer critical questions much faster about their exposure in minutes, often beating CVE assignment and official vulnerability databases to the punch.
Strengthening the shield: Community and visibility #

In the 'Force multiplied' session, Rishiraj Sharma (ProjectDiscovery) and Tod discussed how the open-source framework Nuclei has revolutionized how security teams validate vulnerabilities. Sharma explained that Nuclei was created to cut through the noise from traditional scanners, which often flag thousands of potentially vulnerable instances based solely on version detection. Instead, Nuclei lets security pros outline the exact steps a person would take to verify an exploit, making it clear which assets are really at risk and need immediate attention.
Thanks to input from pentesters, bug bounty hunters, and researchers worldwide, Nuclei can now create verified exploit templates in just hours instead of days. Sharma also noted that ProjectDiscovery’s bug bounty program incentivizes researchers to write new templates and validate existing ones to ensure high quality and reduce false positives.
A new kind of RSAC experience #
At the end of the day, the best part of runZero Day wasn’t just one session — it was the insights shared and the format. By moving the conversation beyond the Moscone Center, we were able to broaden the audience for the major themes of the cybersecurity industry and RSAC to the world beyond Silicon Valley.
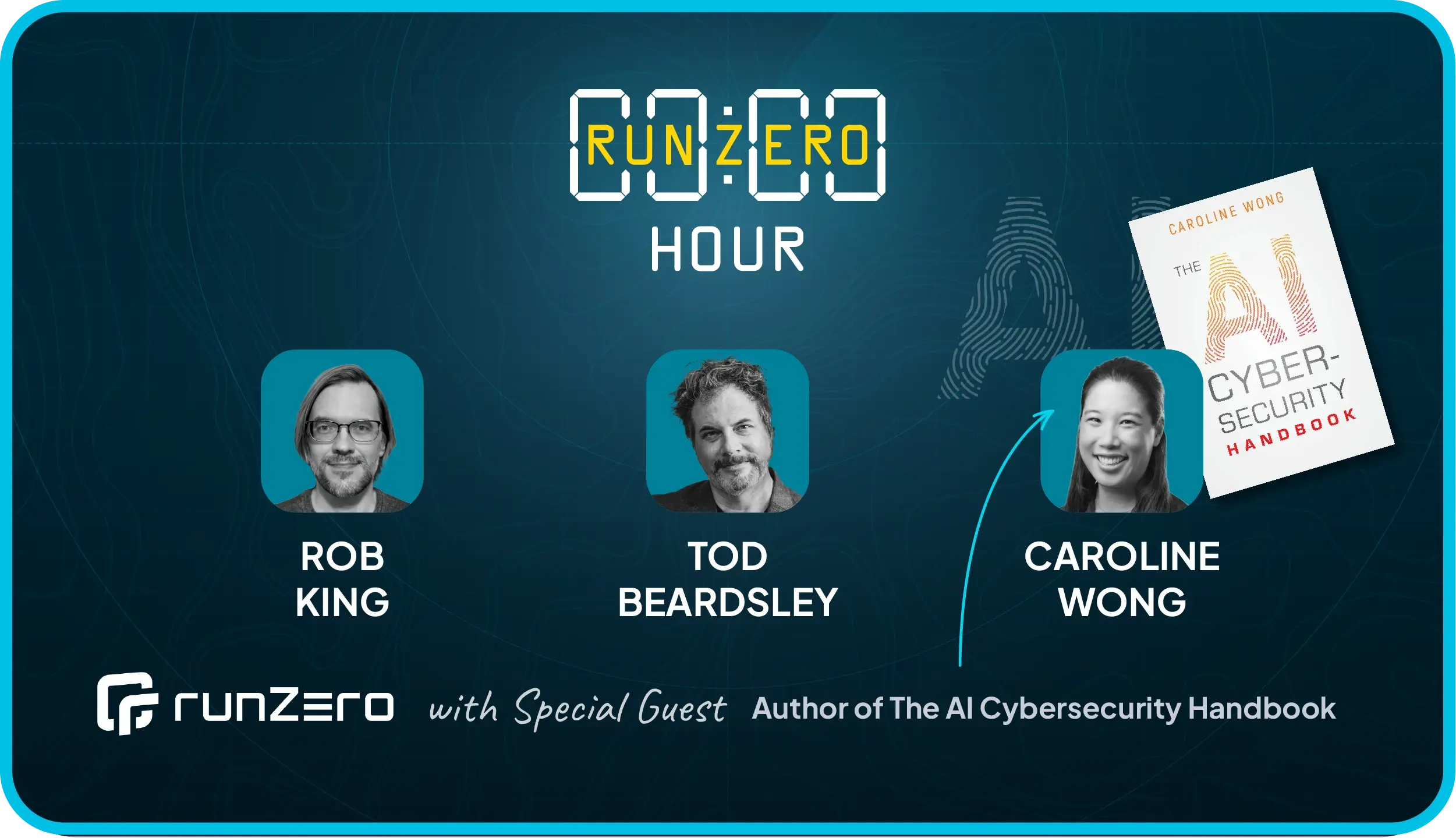
In the end, we hope you dip into the recorded stream, and if you just can’t get enough, you should definitely join the next runZero Hour, where Tod and Rob will chat it up with Caroline Wong, author of The AI Cybersecurity Handbook. They’ll talk more about the ups and downs of our machine-brained tooling in our day-to-day practice of cybersecurity.