What's new with runZero 3.9? #
Goals! #
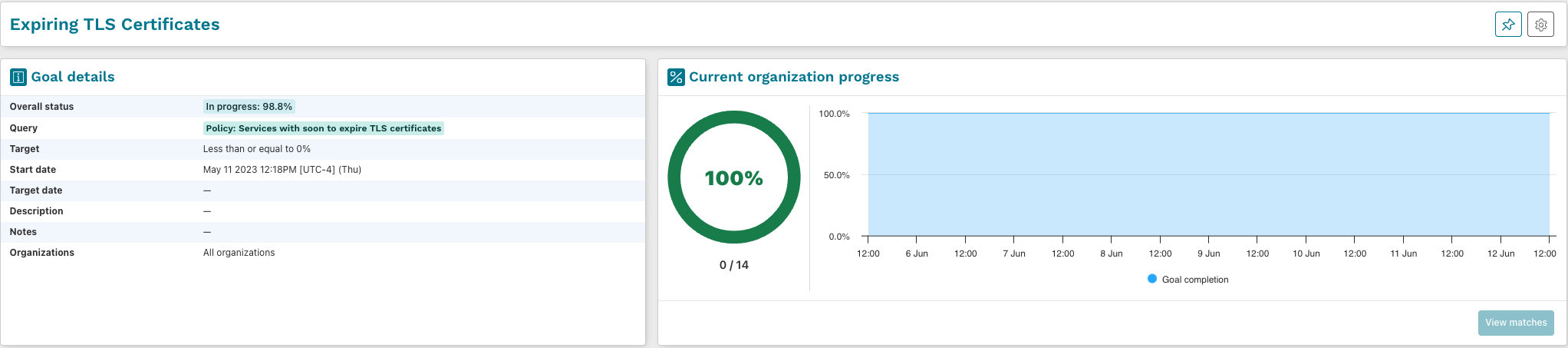
runZero Professional and Enterprise customers can now use Goals to set time-bound and query driven targets that are customizable to what matters most to your team. Huge thanks to all of the folks who provided feedback on this feature during the public preview phase.
Goals can be created based on any queryable attribute within runZero. This includes standard fields like operating system versions, end-of-life status, exposed services and protocols, as well as new fields like asset risk, criticality, and ownership. If you can query for it in runZero, it can now be a Goal!
Common goals include:
- Managing expiring TLS certificates
- Tracking end-of-life devices and operating systems
- Remediating Critical Risk on assets within a set timeframe
- Keeping open management services off of your public facing assets
Attack Surface Management preview #
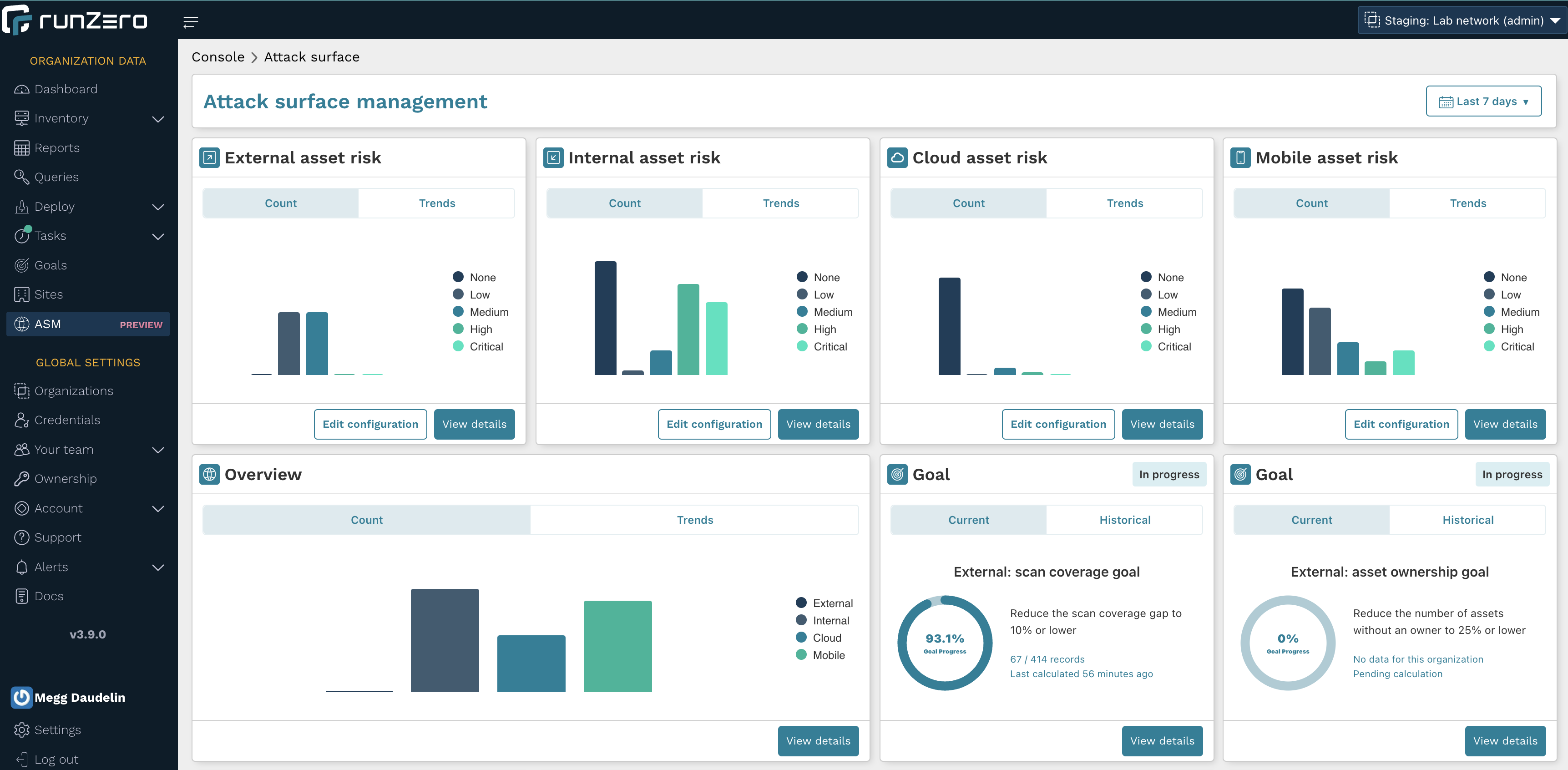
Attack Surface Management (ASM) is the process of discovering, classifying, and assessing the risks across different surfaces of your IT infrastructure. Although runZero supports ASM efforts through external scanning, internal RFC 1918 discovery, and integrations, the platform did not offer a unified workflow or dashboard until now.
The preview version of ASM provides a simple path to define different attack surfaces throughout your organization, providing an overview of risk and coverage along with several custom goals to monitor and communicate your progress. This feature will be in preview until August and will launch publicly as part of runZero 4.0.
If you are a runZero Enterprise customer and are interested in reviewing this feature and providing feedback, please reach out to your CSE or or runZero Support. Participants will be asked to complete a short feedback form after reviewing the feature.
Rapid Responses #
The runZero research team has shared three new Rapid Response posts since 3.8. These posts cover critical, actively exploited vulnerabilities:
Protocol improvements #
runZero now supports the InterMapper and Room Alert protocols, as well as legacy protocols such as time, daytime, chargen, and quote of the day.
runZero's printer support has been improved, enabling protocol detection on ports normally associated with direct print services. This change allows for more accurate detection of Elastic Search, Neo4J, and LogStash services.
In addition to the changes above, runZero now consistently normalizes the AirPlay protocol fields and gathers even more details using the DNS protocol.
Fingerprint improvements #
New fingerprints were added for products by Allen-Bradley, Alma, Amazon, Apple, Avaya, Avigilon, Avocent, Axess TMC, Bodot, Bond, Canon, Canonical, Cisco, ComNet, Dell, Digital Loggers, Eaton, Epson, F5, Fedora, FreeBSD, Fortinet, Google, Hanwha Techwin, Honeywell, HP, HPE, IBM, Johnson Controls, Konica Minolta, LG, Lidarr.Audio, LinkTap, Microsoft, MikroTik, Moxa, NetBSD, Oracle, Panasonic, Philips, Pioneer, Poly, Progress Software, Proxim Wireless, Proxmox, Radwin, Red Hat, RetailNext, Riverbed, Rocky, Samsung, Schneider Electric, Scientific, ScreenBeam, Siemens, Sierra Wireless, SMC Networks, Sony, Standard Networks, SUSE, Tait Communications, Traficon, Tulip, VivoTek, Western Digital, Vasion, Xiaomi, ZeeVee, and ZKTeco.
See runZero 3.9 in action #
Release notes #
The runZero 3.9 release includes a rollup of all the 3.8.x updates, which includes all of the following features, improvements, and updates.
New features #
- runZero goals are now generally available. With runZero goals, users are able to create and monitor progress toward achieving security initiatives.
- Improved the goal progress chart display to work in various browser sizes.
- Goals now shows a pending calculation banner when goal metrics have not been calculated yet.
- Added
source_countandcustom_integration_countas searchable fields. - Saved queries can now be created for tasks.
- The search keyword
recur_last_task_statusis now supported on the task pages. - Improved the display of dashboard charts so that no partial rows, other than the last row, are visible to the user regardless of the number of charts displayed.
- Improved fingerprinting of Fortinet device firmware.
- Optimized database utilization and improved performance.
Product improvements #
- Non-runZero asset sources can now be removed from assets via the asset details or asset inventory pages.
- Equivalent emails are now accepted for email updates.
- Dashboard cards for Asset Source and Custom Integrations should now correctly show only the top 10 counts for each, with a
View morelink added. - A warning is now displayed if a Query is not attached to a Goal.
- Users with
Viewerpermission can now see and use the Sites page. - Improved reliability of scans so they should stall less frequently.
- The activation email should display properly in a broader range of email clients.
- Improved operating system fingerprinting via SNMP Installed Software listing.
- The status indicator in the explorer datagrid now has text describing the status.
- External Asset Report
Include screenshotstoggle now requires thatInclude asset detailsis checked. - External Asset Report now hides the
Top certificate authoritiessection ifInclude TLS certificate detailsis not checked. - Outlier calculations have been adjusted for performance and now include the TLS stack.
- Event rules that result in asset modifications now complete faster.
- The Npcap driver has been updated to version 1.75.
- Improved device type identification of Windows Server assets.
Integration improvements #
- Improved SentinelOne matching to improve asset merging.
- AWS credential validation now always shows the results for each service.
New vulnerability queries #
- Hardware: End-of-Life Cisco Small Business Switches
- Policy: Sun Solaris sadmind RPC service
- Policy: HashiCorp Consul (unauthenticated)
- Policy: Cisco Smart Install service
- Policy: CNCF etcd v2 (unauthenticated)
- Unpatched: Click Modular Router shell (unauthenticated)
- Unpatched: HID VertX/Edge controllers vulnerable to command_blink_on command execution
Bug fixes #
- A bug causing Cisco 8xx Industrial Routers as well as Catalyst 94xx/95xx switches to be incorrectly merged has been fixed.
- A bug where the autocomplete drop down would not always appear on top of other elements has been resolved.
- A bug where integration sources in dashboard views are displayed as IDs instead of names has been resolved.
- A bug where data grid search text would propagate to other data grids has been resolved.
- A bug causing some text inputs to display an autocomplete user experience when it was not intended was resolved.
- A bug that could allow merging AWS, Azure, and GCP assets has been resolved.
- A bug which omitted some SNMPv3 scan attributes has been resolved.
- A bug which caused some project creations to return a
404error page has been resolved. - A bug causing incorrect HTTP response codes for the
/org/metrics/{site_id}API endpoint has been resolved. - A bug which cleared the organizations table screen when sorted has been resolved.
- A bug preventing vulnerabilities from sorting correctly on CVSS columns has been resolved.
- A bug where scan tasks on hosted zones couldn't be stopped has been resolved.
- A bug preventing vulnerabilities from sorting correctly on CVSS columns has been resolved.
- A bug that could result in excessive memory usage has been resolved.
- A bug that resulted in certain models of Cisco routers being incorrectly merged has been resolved.
- A bug in which AWS probes fail when run outside of an AWS EC2 environment has been resolved.
- A bug which prevented IPv6 UDP SYN scans from working on FreeBSD and OpenBSD systems has been addressed.
- A bug where autocomplete suggestions would not update consistently has been resolved.
- A bug causing the "download task button" to show for tasks without a log has been resolved.
- A bug that could cause the SNMP probe to panic in rare scenarios has been resolved.
- A bug that could cause the SNMP probe to stall scans in rare scenarios has been resolved.
- A bug that caused scans to take longer than expected or stall in rare scenarios has been resolved.
- A bug that could prevent the organization dropdown from being clickable has been resolved.
- A bug that could prevent the
rpcbindprobe from completing successfully was resolved. - A bug with copying some connector tasks has been resolved.
- A bug causing some connectors to be labeled as scans has been resolved.
- A bug causing the API
/org/hosted-zonesendpoint to return an empty list of hosted zones has been resolved. - A bug that could result in an invalid asset ownership assignment has been resolved.
- A bug that could prevent a
RUMBLE_CONSOLEoverride from working in the Explorer configuration has been resolved. - A bug that prevented sites with more than 1000 subnets from being saved has been resolved.
- A bug that could result in odd dashboard chart behavior has been resolved.
- A bug that required self-hosted users to configure SMTP before setting up their initial account has been resolved.
- A bug that caused some scan task errors to be displayed twice has been resolved.
- A bug that could prevent bogus services from certain firewalls from being completely filtered has been resolved.
- A bug where Asset queries for exact strings was performing a fuzzy search has been fixed.
- A bug that could cause malformed auto-populated LDAP thumbprints for LDAP credentials has been resolved.
- A bug that prevented credential validation errors from displaying after verification in the console has been resolved.
- A bug where searching via clicking on a tag would not return the correct results has been resolved.
- A bug where multiple subtasks were incorrectly created for the same parent task has been resolved.
- A bug where filters were not retained when importing a Nessus scan configuration has been resolved.
- A bug that prevented copying of some connector tasks has been resolved.
- A bug with linking to the update page on some connector tasks has been resolved.
















