Heya! Remember when we first talked about CISA’s new BOD 26-02 on End-of-Service (EOS) edge devices back in early February, then provided a handy query to find such internet-exposed EOS devices on your own network?
Well, we’ve gone and made it even easier with a new Findings tab, right in the console. Down with typey-typing, and up with clicky-clicking!
Check it out:
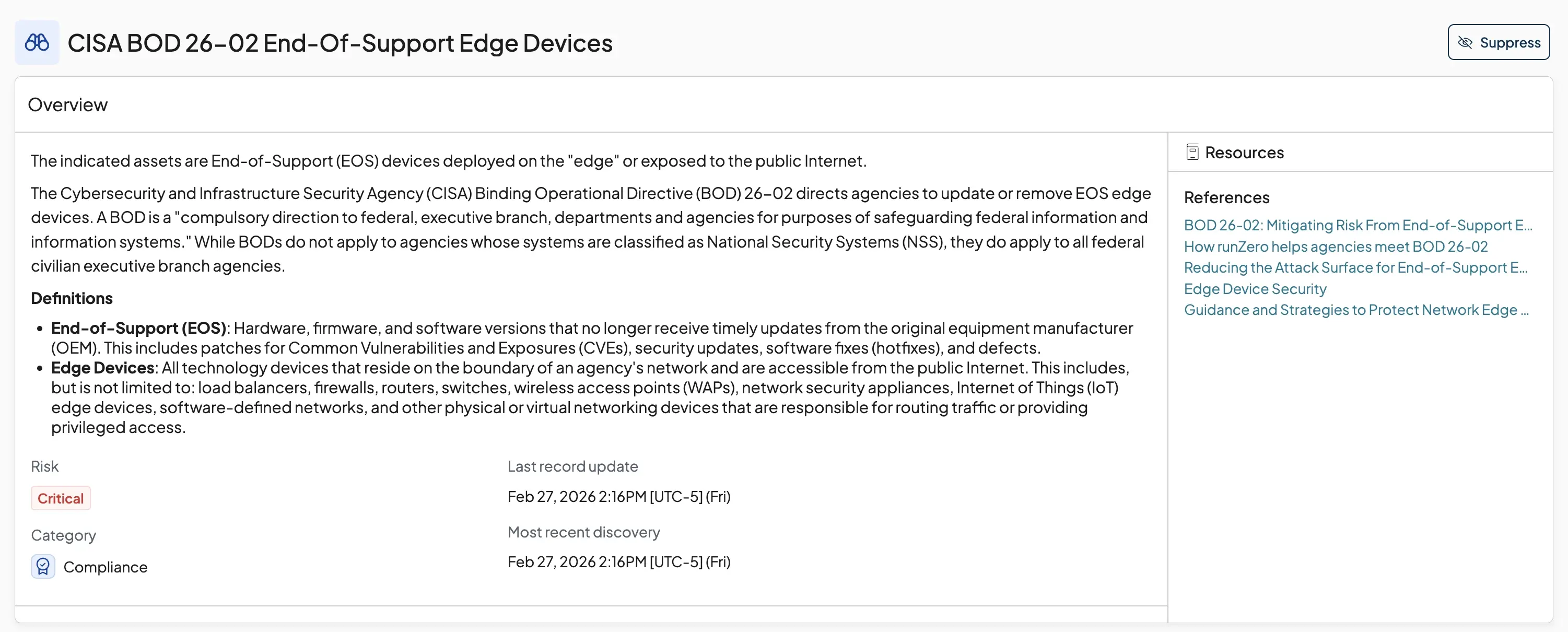
For those who missed the earlier posts, BOD 26-02 is CISA’s two-year program requiring federal civilian agencies to identify and address unsupported edge devices like firewalls, VPNs, routers, proxies, etc. The clock started ticking on February 5th which means the first milestone of having a mechanism in place to identify all edge devices (supported and unsupported) in production begins on May 5, 2026.
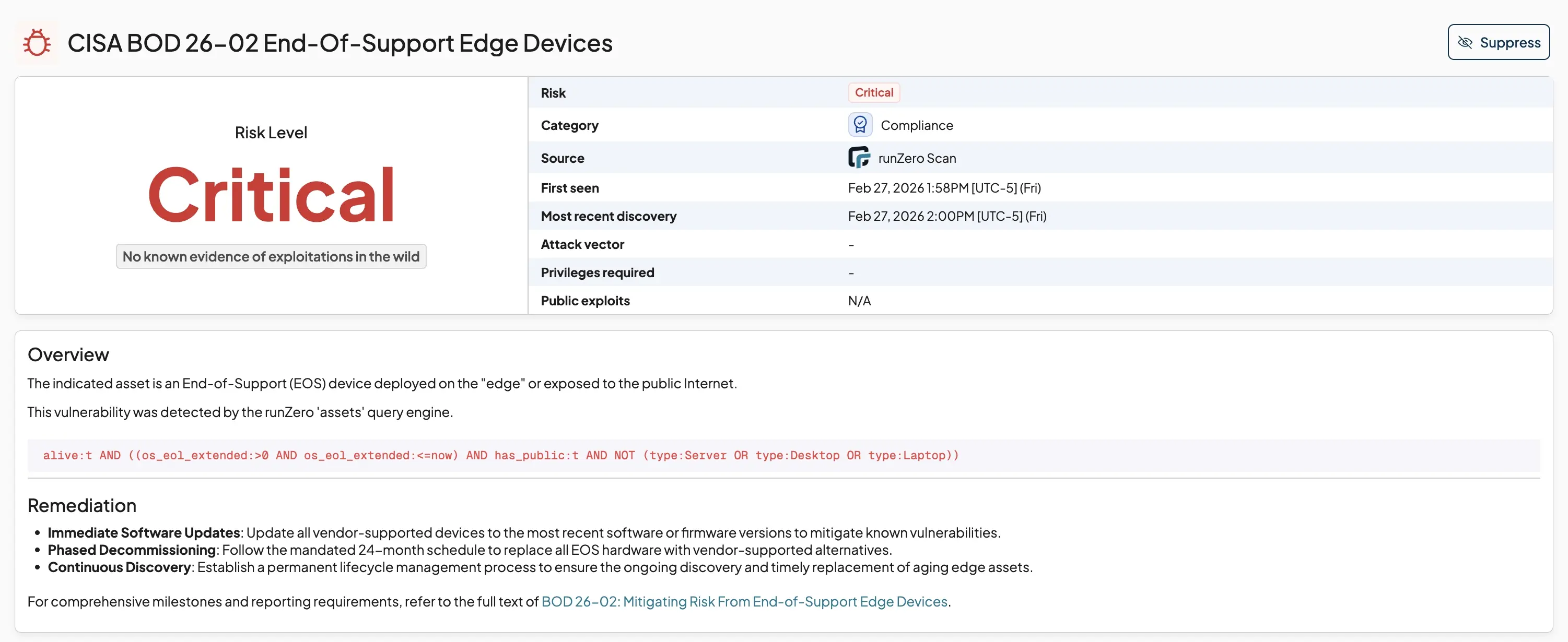
One wrinkle worth noting is that unlike BOD 22-01 and the KEV, CISA decided to keep their official EOL edge device list private. This Finding maps directly to the query we shared last time, surfacing devices in “EOL Extended” state that are exposed to the public internet and aren’t normal servers, desktops, or laptops.
With this update — free to all customers, even the free-trial folks — runZero users can enjoy a consistent, obvious way to track against what CISA (and we) believe are some of the most critically exposed assets on your network. Going forward, we’ll continue to make things easy and clear for you with this Findings tab as we integrate more fingerprints and profiles of commonly-attacked endpoints, so you can get down to the business of upgrading, retiring, or segmenting off these attractive-to-attackers assets.

















