Most organizations have gone through a network segmentation project. If you polled security architects, the CISO, and network infrastructure people — particularly in OT — the vast majority would tell you that a combination of firewalls and network segmentation protects against the spread of an attack. In my experience, it is usually more assumption than fact that sensitive areas of the network like OT environments have adequate segmentation, and protection.
Threat actors thrive on these assumptions.
But runZero makes zero assumptions. We discover, validate, and map the potential attack paths for you.
With the release of runZero 4.9, two powerhouse capabilities combine to eliminate this critical visibility gap and reveal exactly how attackers will exploit your network, so you can prevent it.
Understand the entire iceberg, not just the tip #
Using safe, protocol-native queries, runZero recursively walks the backplane to identify the many hidden sub-devices sitting behind Modbus and BACnet gateways. Where traditional tools see only a single gateway IP address, runZero unveils the entire field-level topology of vulnerable PLCs and nested devices downstream of the gateway. Not only do we discover these critical, hidden devices, we fingerprint their attributes and any exposures. Like a ship's sonar that shows the entire iceberg lurking under the waterline, runZero dives deep behind the gateway to see the entire attack surface.
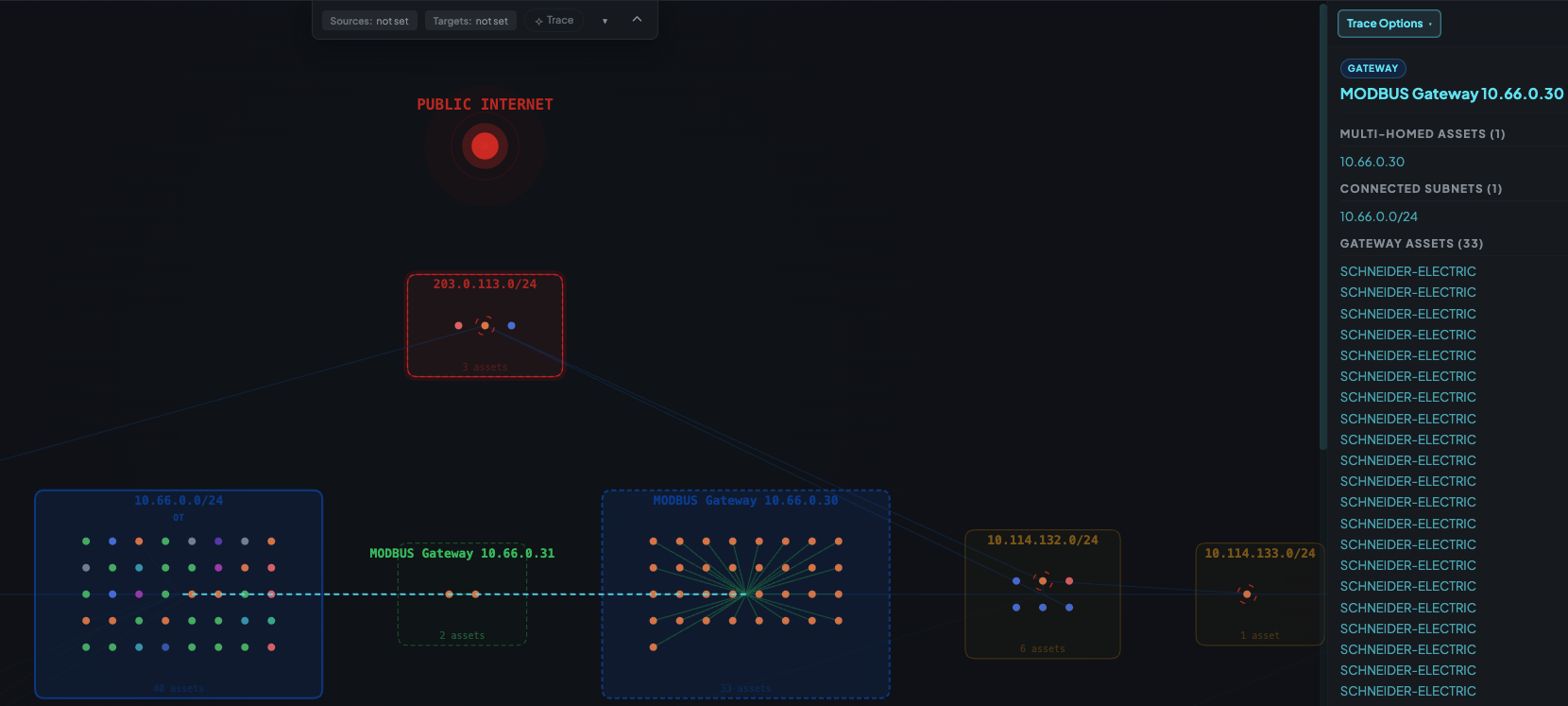
Since OT environments behind the gateway are usually flat, an attack on one of these hidden assets represents a massive lateral movement risk. Compromising a single downstream PLC can grant an adversary control over the physical outputs — the switches that manage everything from safety valves to high-voltage equipment.
So, seeing these devices and reducing their vulnerability is only the first step. The next critical step is validating how accessible (or not) they really are to a threat actor.
See the path of least resistance for attackers #
After deep discovery, runZero leaves assumptions behind by showing you how an attacker could reach those devices, externally or internally. Interactive attack path mapping illuminates avenues of attack that most security professionals may never discover. It models the complex trajectories an adversary would use, exposing the "accidental routes" and multi-homed devices (like jump boxes) that bypass your carefully planned segmentation.
Other vulnerability scanners miss these risks since they are focused only on known vulnerabilities. runZero shows you these paths of least resistance, allowing defenders to focus on the critical exposures and assets that pose the most devastating risk.
The Payoff #
Together, these capabilities completely transform your defensive strategy. Without runZero, you have incomplete visibility plus untested assumptions of your network segmentation. But with runZero, you’ve got complete and automatic discovery, plus attack path mapping that trades assumptions for validation. With runZero, you can map the unmappable, secure every path, and safeguard your OT environments.
Start your free 21 day trial and begin your own discovery now.
















