Latest NetWeaver vulnerability #
On September 9th, 2025, SAP issued patch note 3634501 to disclose an insecure deserialization vulnerability that affects certain versions of SAP NetWeaver. The vulnerability is related to the RMI-P4 module, which handles Remote Method Invocation (RMI) and Common Object Request Broker Architecture (CORBA) features. This module uses the P4 protocol, a proprietary SAP protocol that allows remote objects to communicate over the following default port ranges:
- P4: 50004–59904
- P4 over HTTP: 50005–59905
- P4 over SSL: 50006–59906
An adversary can exploit this vulnerability by sending a malicious payload to an open port used by this module, causing the application to deserialize untrusted Java objects. Successful exploitation could allow a remote, unauthenticated adversary to execute arbitrary OS commands on the target system. This vulnerability has been designated CVE-2025-42944 and has been rated critical with a CVSS score of 10.0.
The following versions are affected
- SAP NetWeaver SERVERCORE versions prior to and including 7.50
What is the impact? #
Successful exploitation of the vulnerability would allow an adversary to execute arbitrary code on the vulnerable host, potentially leading to complete system compromise.
Are updates or workarounds available? #
Users are encouraged to update SAP NetWeaver SERVERCORE to the latest version as quickly as possible.
How to find NetWeaver installations with runZero #
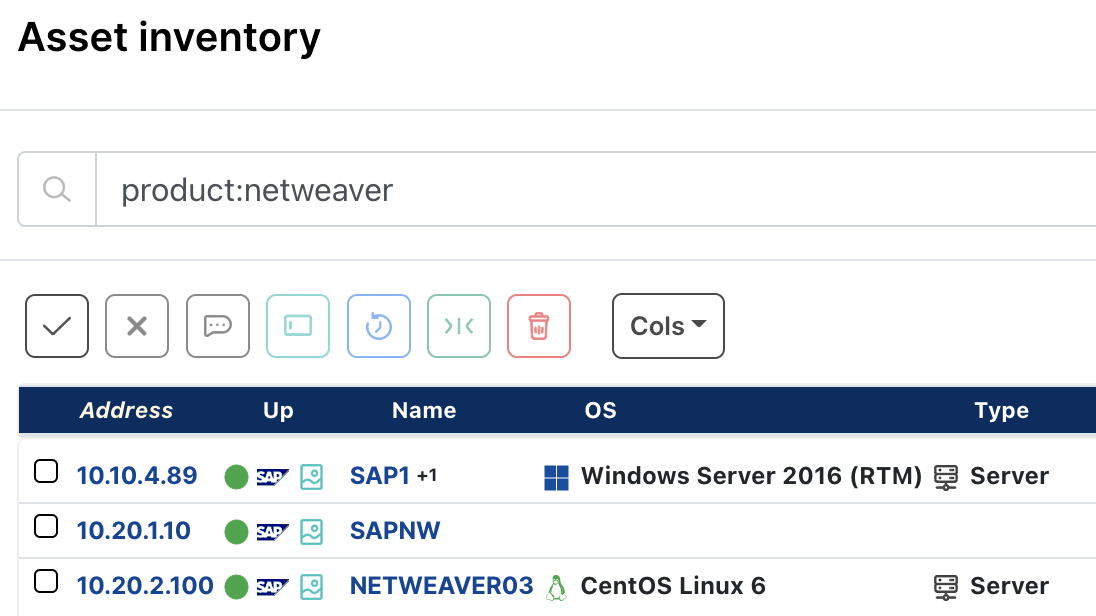
From the Asset inventory, use the following query to locate assets running any version of NetWeaver:
product:NetWeaverFrom the Software Inventory, use the following query to locate potentially impacted assets:
vendor:=SAP AND product:"NetWeaver" AND version:<=7.50April 2025: (CVE-2025-31324) #
On April 24, 2025, SAP issued an emergency patch note for several of the Visual Composer development server component of the NetWeaver server.
- CVE-2025-31324 is rated critical with a CVSSv3 base score of 10.0. Successful exploitation of this vulnerability could lead to remote code execution by remote unauthenticated attackers.
What is the impact? #
A missing authentication check within the Visual Composer Metadata Uploader could allow remote unauthenticated attacker to upload malicious files, such as webshells, to a vulnerable target. They could then directly execute the shells via GET request potentially resulting in system compromise.
The Visual Component development server is not installed by default but is reportedly very commonly installed and used.
Are updates or workarounds available? #
SAP has issued patches and provided some mitigation guidance for all affected software. Refer to the advisory above for more information. The official documentation indicates that NetWeaver 7.50 and higher are impacted but there have been reports that this impacts 7.1x as well.
How to find NetWeaver installations with runZero #
From the Asset inventory, use the following query to locate assets running any version of NetWeaver:
product:NetWeaverFrom the Software inventory, use the following query to locate assets running any version of NetWeaver:
vendor:="SAP" AND product:"NetWeaver" AND (version:>7.0 AND version:<7.55)March 2025 : SAP Commerce, Commerce Cloud and NetWeaver vulnerabilities #
On March 11th, 2025, SAP issued an advisory for several of their products including Commerce, Commerce Cloud and NetWeaver.
- CVE-2025-26661 is rated high with a CVSSv3 base score of 8.8. Successful exploitation of this vulnerability could lead to privilege escalation and the potential disclosure of sensitive information.
What is the impact? #
A missing authorization check within the ABAP Class Builder could allow an authenticated attacker, or malicious user to escalate their privileges, which could lead to the disclosure of sensitive information.
Are updates or workarounds available? #
SAP has issued patches for all affected software. Refer to the advisory above for more information.
How to find NetWeaver installations with runZero #
From the Asset inventory, use the following query to locate assets running any version of NetWeaver:
product:NetWeaverFebruary 2022: SAP NetWeaver vulnerabilities #
A set of recently patched SAP vulnerabilities has been surfaced by the U.S. Cybersecurity and Infrastructure Security Agency (CISA), with their recommendation to patch as soon as possible. Discovered and disclosed by security researchers at Onapsis, these three vulnerabilities are referred to as ICMAD and affect SAP applications which utilize the SAP Internet Communication Manager (ICM).
Which SAP NetWeaver versions are affected? #
Some versions of SAP NetWeaver contain all three of these ICMAD vulnerabilities:
- CVE-2022-22536 (CVSS "critical" score of 10.0) - vulnerable to request smuggling and request concatenation, successful exploitation by an unauthenticated attacker resulting in code execution, victim impersonation, data exfiltration, denial of service, and more. In addition to NetWeaver, some versions of SAP Web Dispatcher and SAP Content Server also contain this vulnerability.
- CVE-2022-22532 (CVSS "high" score of 8.1) - vulnerability in shared memory handling, successful exploitation by an unauthenticated attacker resulting in code execution, victim impersonation, or taking over the victim's logon session.
- CVE-2022-22533 (CVSS "low" score of 3.7) - vulnerability in error handling which could result in a denial of service attack by exhausting available memory, leading to system shutdown.
Is a security patch available? #
Yes. SAP made patched software available earlier this week. While there currently are no known customer breaches related to exploitation of the ICMAD vulnerabilities, SAP does strongly recommend that admins update to the latest available versions as soon as possible.
How do I find potentially vulnerable SAP NetWeaver instances with runZero? #
From the Asset Inventory, use the following pre-built query to locate SAP NetWeaver assets within your network that are potentially vulnerable:
product:netweaver
As always, any prebuilt queries we create are available from our Queries Library. Check out the library for other useful inventory queries.
Try runZero #
Don't have runZero and need help finding potentially vulnerable SAP instances? Start your runZero trial today.


















