In the world of security marketing, "visibility" has become an overused buzzword. But for those of us actually tasked with defending converged IT/OT environments, visibility isn't about seeing a list of IPs; it's about understanding the functional DNA of our infrastructure.
For years, the industry has relied on the "segmentation illusion"— the comfortable but incorrect assumption that critical industrial assets are air-gapped or safely tucked away behind layers of firewalls. Today, the threat landscape is rapidly evolving due to geopolitical dynamics and AI-powered attacks that are designed to quickly identify segmentation weaknesses, along with other common footholds like internet-exposed OT assets, unpatchable legacy systems, and untrustworthy IT/OT boundaries that turn a minor business breach into a total operational shutdown.
Our latest release is designed to give defenders the high-fidelity asset, network, and security intelligence they need to win in this environment. With the new features in runZero 4.9, you can see exactly how an attacker could move through your network via a series of pivot points, allowing you to harden critical choke points and remediate exposures before they are exploited. We’ve also expanded our OT telemetry to provide deep insights into the role and risk profile of every device in increasingly converged environments.
Here's a quick demo of the new features, or keep reading to learn more:
Map the unmappable. Secure every path. #
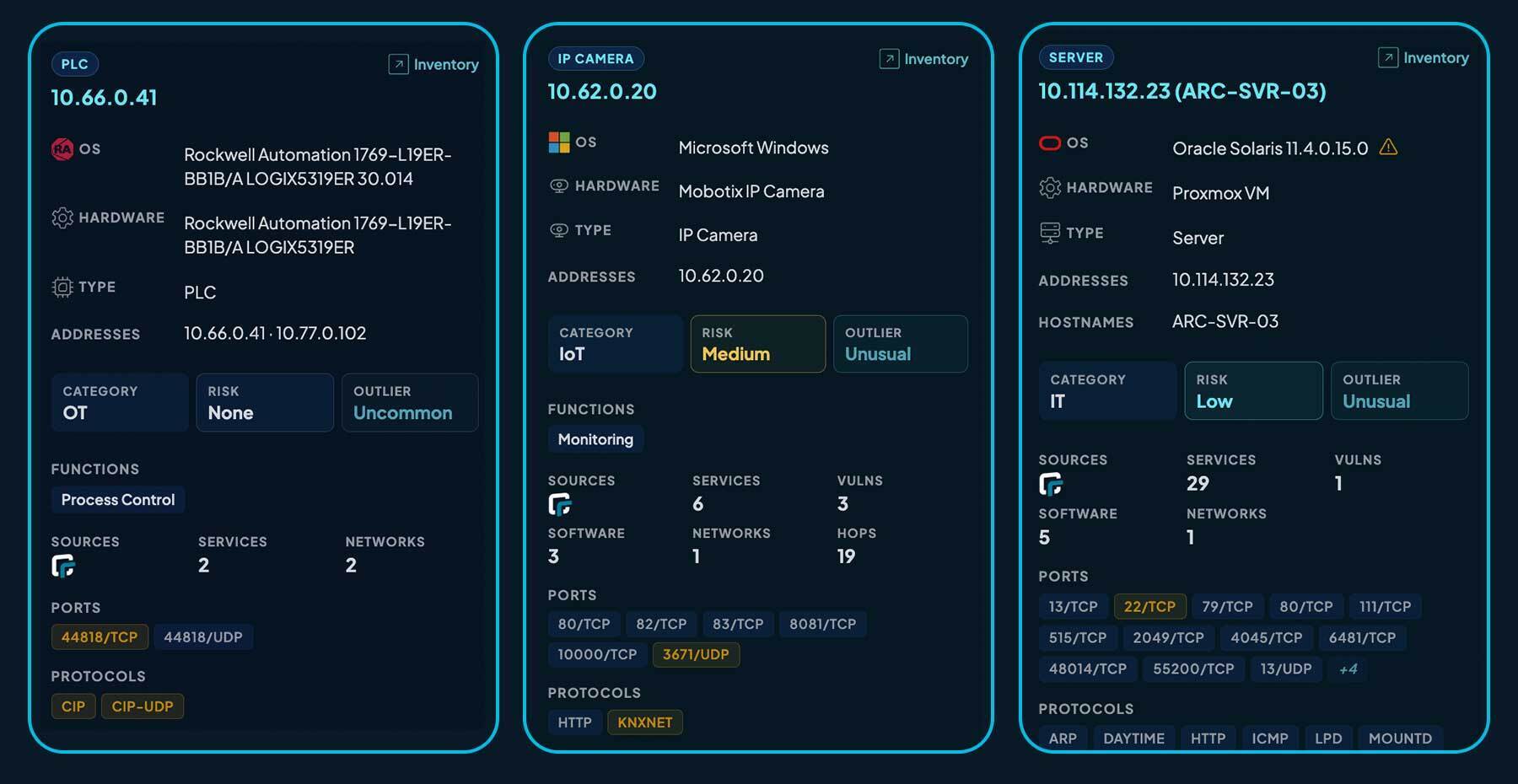
Most OT practitioners have been taught that active scanning is dangerous. We’ve already proven that’s a myth in numerous deployments and in robust testing conducted by the U.S. Department of Energy’s National Renewable Energy Laboratory. runZero’s scan engine is purpose-built for safety. By using safe, protocol-specific probes and granular throttling, we extract high-fidelity metadata — firmware versions, screenshots, and even secondary interfaces — without requiring a single credential or endpoint agent.
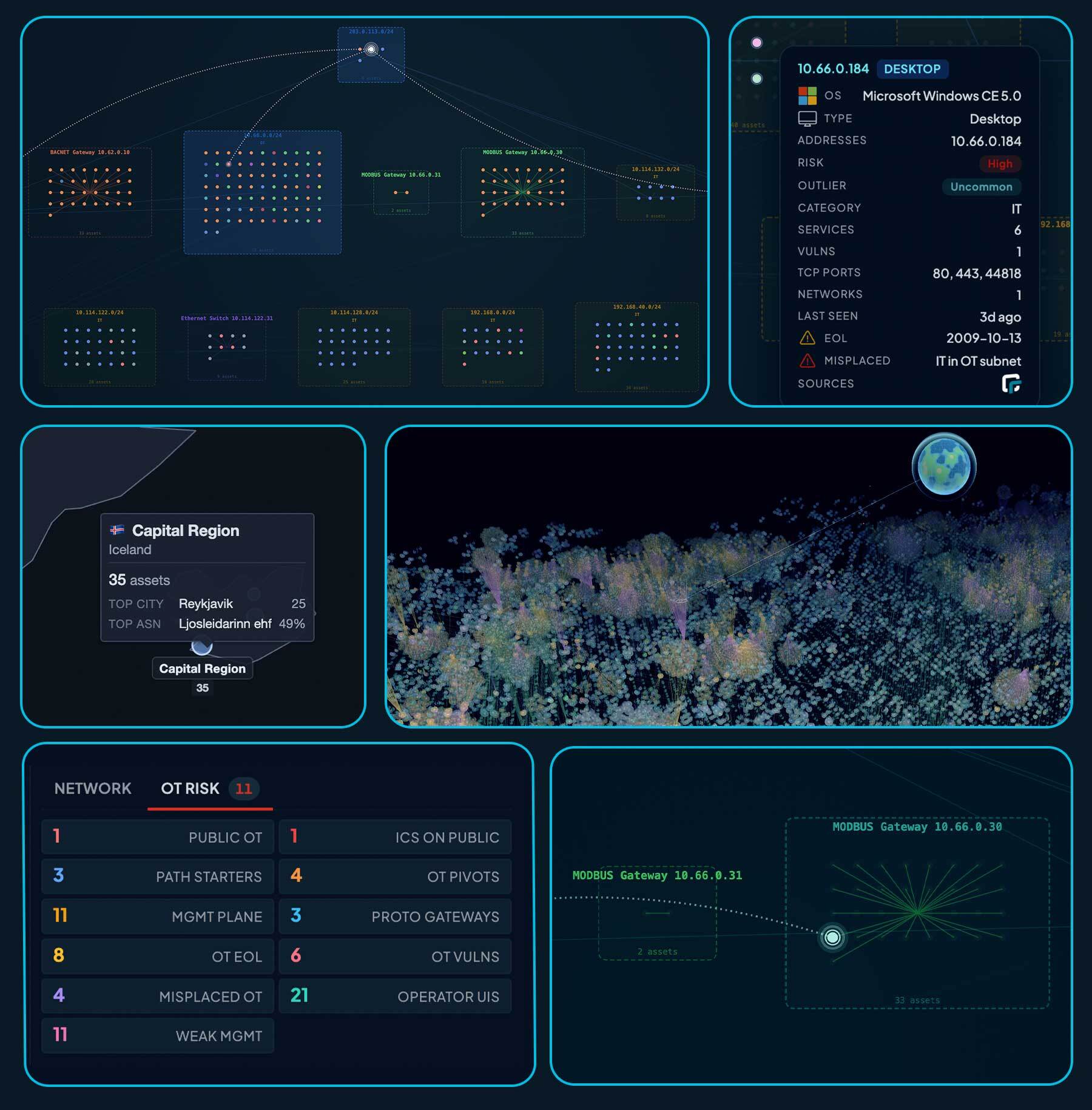
One of the breakthroughs in this release is our ability to map the unmappable. We are one of the only solutions that can now enumerate "sub-assets" sitting behind protocol gateways like Modbus, BACnet, KNXnet, and EtherNet/IP. If you have a gateway with 20 PLCs behind it, we don't just see the gateway; we see the entire field-level topology.
Other capabilities that runZero’s latest release brings to the fight, include:
Topology maps that actually scale (and are fun to explore!) #
Our new 2D and 3D maps let you zoom from a global overview all the way down to individual sites and subnets, enabling you to quickly spot exposures even in environments with hundreds of thousands of assets. No more untangling the network spaghetti; these maps provide clear visuals that make sense of even the most complex environments. With hybrid Layer 2 and Layer 3 views, you can finally see how your physical and logical networks actually overlap. Other new features include the ability to:
Geolocate assets instantly: We use public and egress IP data to pinpoint where your gear is physically sitting across the globe and have added tools so you can search for nearby devices to gain critical environmental context.
Hunt and search in the map views: Get eyes on high-risk assets, pivot points, end-of-life systems, specific device types, and exposures by searching and filtering directly in the map view.
Spot the "weird": Quickly flag anomalies, like a misplaced Windows laptop sitting in a segmented production zone where it definitely doesn't belong, as well as outliers that don’t look like the others (pro tip: this usually means they’re risky devices).
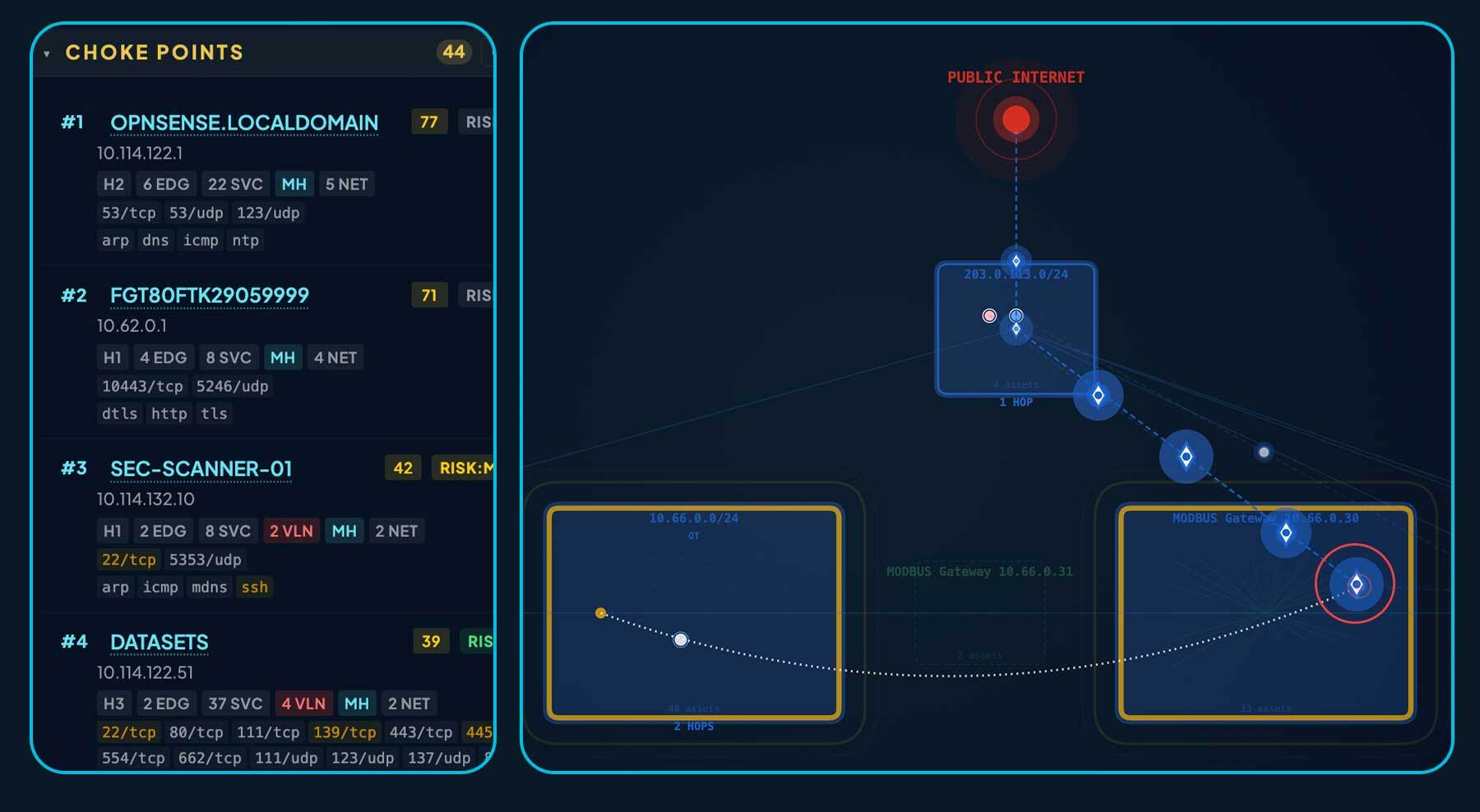
Interactive attack path mapping #
Want to know how an attacker would move around your network? You can now visualize trajectories from initial compromise to operational impact.
Trace the attack path: Set a source and a target to see the exact pivot points and bridges an attacker would use to traverse your environment.
Find the choke points: See which critical assets could grant attackers access to your crown jewels.
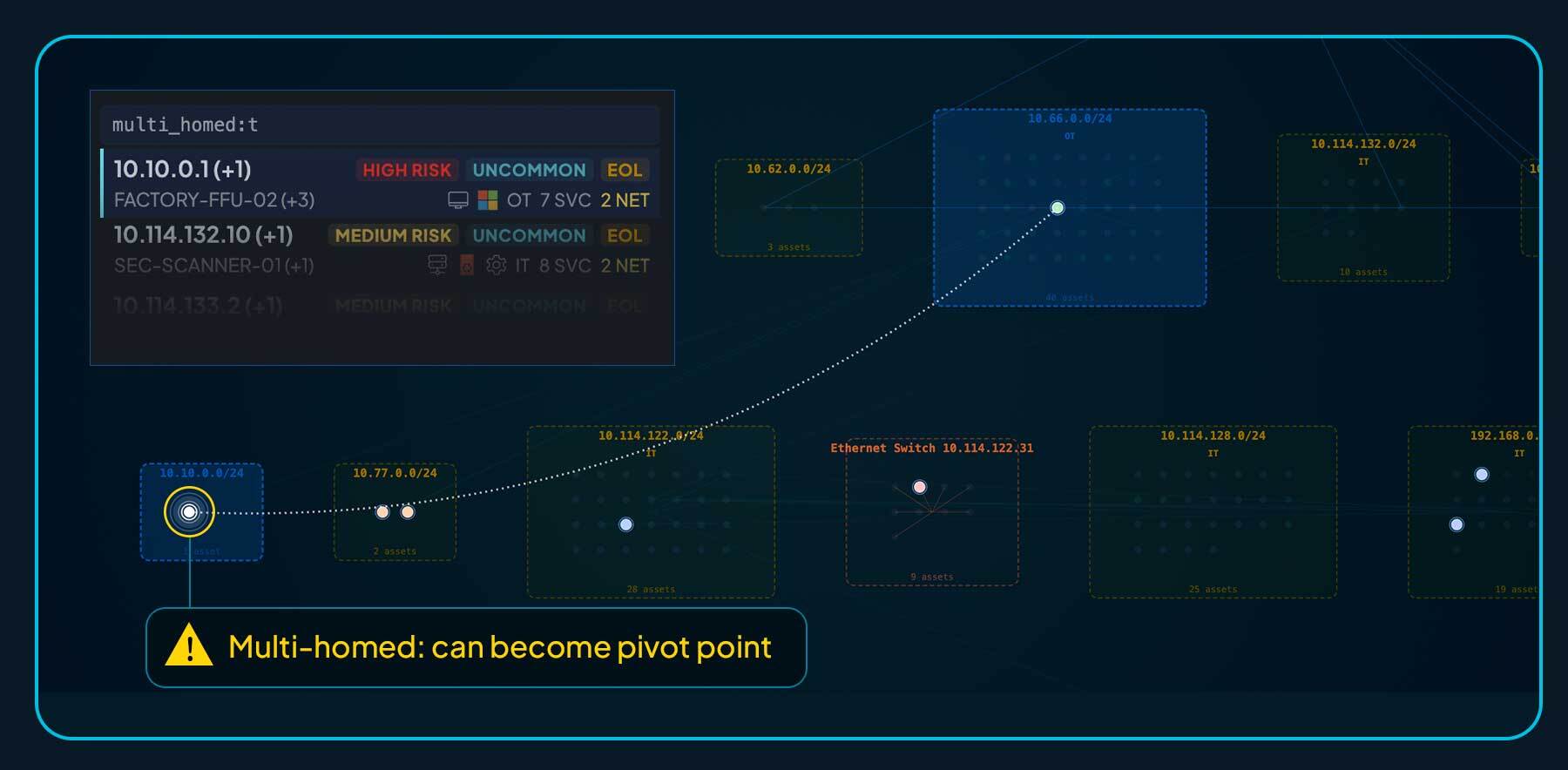
Multi-homed and bridge detection #
Automatically surface devices connected to multiple networks and bypass your carefully planned segmentation and firewall strategies.
Go beyond the gateway #
Other tools stop at the protocol gateway. We don’t. runZero uses safe, protocol-native queries to peer behind gateways and unmask the downstream PLCs and field-level devices sitting on serial and fieldbus networks.
Unmask protocol exposures #
Gain asset intelligence across your entire attack surface with an expanded library of 220+ protocols. This release delivers deep visibility into dozens of "insecure by design" industrial protocols — like Modbus, BACnet, EtherNet/IP, and Siemens S7comm — which are commonly targeted by attackers attempting to pivot from the network to physical operations.
Real-world risk prioritization #
Not every exposure is a hair-on-fire emergency. We help you focus on the segmentation gaps and vulnerabilities that actually put your operations at risk.
Device classification and even-deeper fingerprinting #
We analyze thousands of distinct asset attributes to ensure you have definitive insights into exactly what a device is and what it’s doing on your network. The latest release adds asset categorization and function tags that you can use to search, filter, and explore.
Sleek UI/UX enhancements — now with new dark and light modes #
We’ve overhauled the interface to make data exploration faster and easier across any sized environment, even the massive ones. And yes, we finally added dark mode, because we know what it’s like to stare at a screen in a dimly lit SOC at 2am — plus, it just looks cool. If you prefer the high-contrast life, there’s a new light mode, too. Or, stick with the "classic" view — whatever helps you hunt best!

Real-world scenario: IT-origin with OT blast radius #
To illustrate the power of this release, let's look at a scenario to see how our new capabilities turn raw telemetry into a defensive strategy.
The biggest threat to industrial operations usually isn't a "Stuxnet-style" custom exploit; it’s an IT-originated event that cascades into OT because the boundary between the two is weak. In this case, the culprit isn't a complex hack — it’s a single, forgotten workstation that shatters the "segmentation illusion" and turns a network breach into a total factory floor shutdown.
The dangerous, but intentional "administrative" bridge #
Imagine an attacker gaining a foothold in the corporate IT network through a security camera using default credentials (yes, we can help you find that). These cameras are oftentimes inside the network, but out-of-the-box settings tell firewalls to port forward internet traffic to them, exposing them to the world.
While searching for high-value targets, the attacker discovers a technician’s laptop on the same wireless network as the camera. This laptop is plugged into the factory network — but for internet access, the technician is still using the corporate wireless network, and unfortunately has also enabled RDP.
The attacker is able to log in to this laptop with the default technician account, and the laptop becomes the first hop from the internet-exposed camera to the factory LAN, bypassing the main firewall.
From the compromised laptop, the attacker is able to reach the factory LAN, and although the network is mostly segmented correctly, a sole Rockwell Automation controller is attached.
The attacker is able to enumerate the Ethernet/IP (CIP) of the controller and identify additional targets accessible through the protocol gateway, providing full access to RTUs without credentials
By sending an unauthorized "Stop" command through the gateway to the RTU, the attacker shuts down every downstream PLC — halting a $100M production line and disrupting a series of robotic arms and equipment.
The defender’s edge #
But never fear, defenders. runZero’s new capabilities would help you thwart this attack:
Visualize the trajectory: Our new attack path mapping highlights the exact route from the corporate network, through the laptop, and into the production subnet.
Identify the choke point: runZero flags the laptop running RDP as high risk, showing you precisely where your security policy has been bypassed.
See the downstream impact: While the attacker only sees a gateway, runZero’s sub-asset discovery peers behind it to reveal the PLCs controlling the robotic arms and production line equipment. By querying the gateway via specialized industrial protocols like CIP or Modbus, runZero unmasks the field-level devices that were previously invisible to the security team.
Why it matters #
This isn't just a hypothetical "worst-case" scenario — it is a statistical reality. In a recent representative sample of large manufacturing environments, runZero found that 30% of all OT assets are only one hop away from an internet-exposed device, and 90% are within just two hops.
These findings highlight how easily a single forgotten workstation can turn a minor IT breach into a catastrophic operational shutdown. Even in "secure" networks, segmentation is frequently bypassed — often intentionally — to make remote maintenance easier for vendors or technicians.
By surfacing these risky assets and identifying the hidden attack paths they create, runZero enables you to move beyond the "segmentation illusion," harden your boundaries, and ensure your air gap is a reality, not just an assumption.
In-depth intelligence built for converged environments #
Whether you are managing a national telecom, a global manufacturer, or a critical utility, runZero provides the unified source of truth needed to bridge the gap between IT and OT security operations. We don't just find your assets; we visualize reachability and highlight true risk. Because in a world of millions of nodes, the only one that matters is the one an attacker can exploit.
How to get started with runZero
Try the Platform: Interested in seeing runZero in action? You can explore the platform for free for 21 days, and following your trial, you can transition to our free Community Edition (for environments with fewer than 100 assets).
Learn More: Explore our platform and resources for more information about runZero.
















