Rumble v1.16 #
Rumble Network Discovery 1.16 is out, helping you find duplicate SSH keys, monitor for rogue remote access solutions, and collect device serial numbers and asset tags.
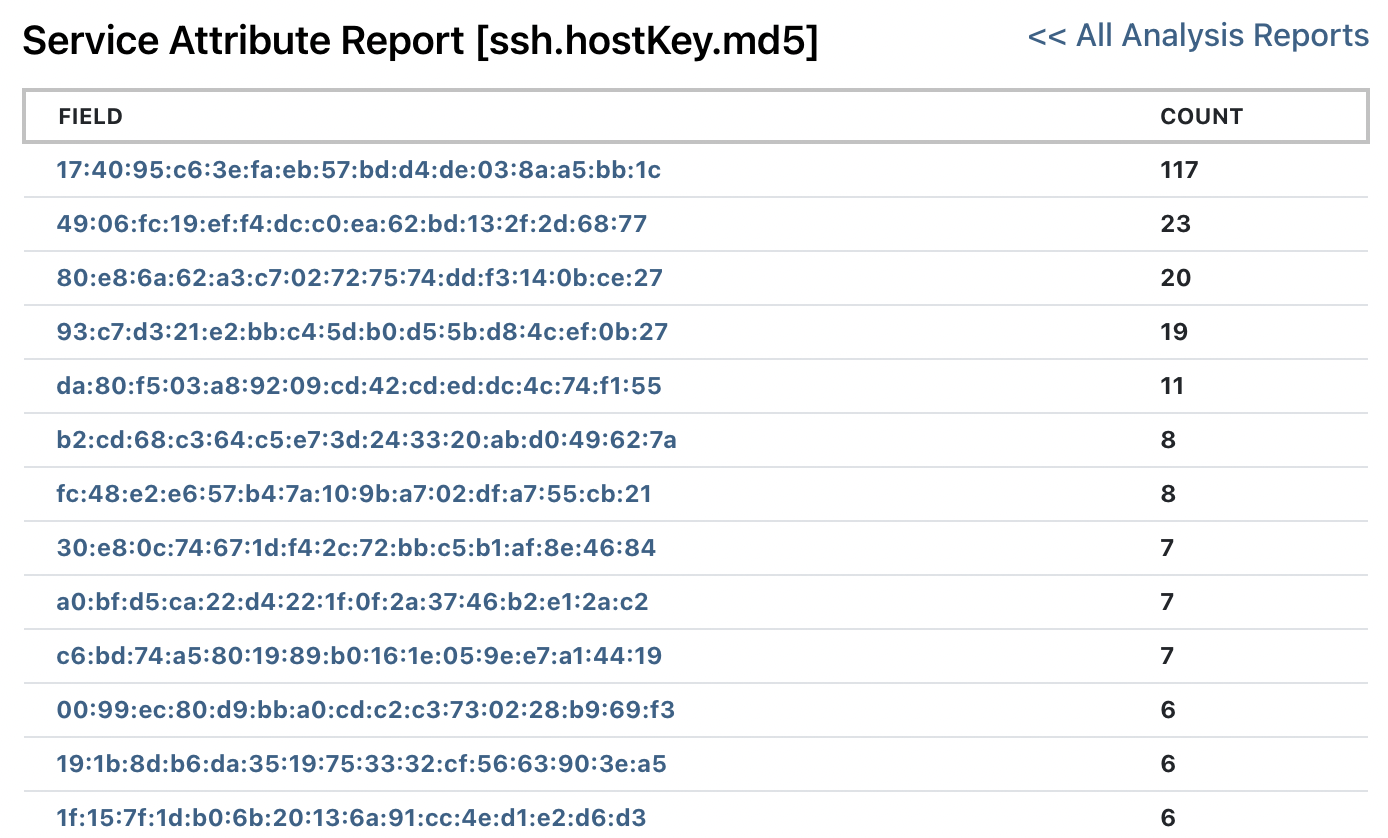
Finding Duplicate SSH Host Keys #
Rumble excels at finding outliers on the network, and finding duplicate SSH keys is one application of this. Vulnerability scanners can find a known bad SSH keys but they don't look for duplicate keys. Rumble collects all SSH key MD5 hashes and then pivots over the SSH host key MD5 to find keys that exist more than once.
Read more about finding duplicate SSH host keys
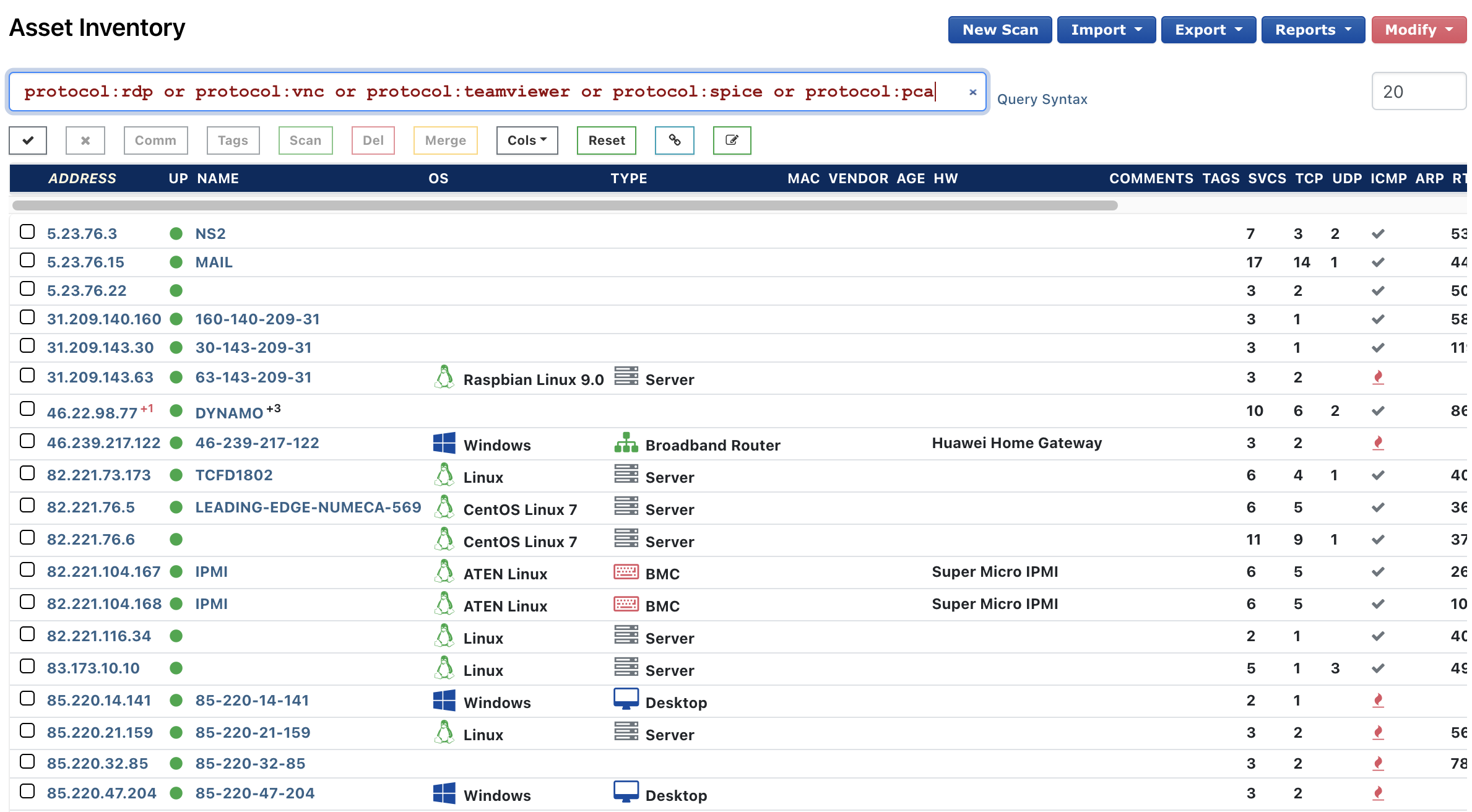
Monitoring for Remote Access Solutions #
Remote Desktop Protocol (RDP) is a useful tool when enabled on a machine that's properly managed on the domain (that is if you're properly managing local accounts). However, RDP can also put you at risk if active on a machine that's not in your domain. It's typically tough to find those, but with Rumble you can. Rumble now detects the TeamViewer protocol on your network in addition to the existing coverage for RDP, VNC, SPICE, and PC Anywhere. This rounds off Rumble's broad support for monitoring remote access solutions.
Read more about monitoring for remote access solutions
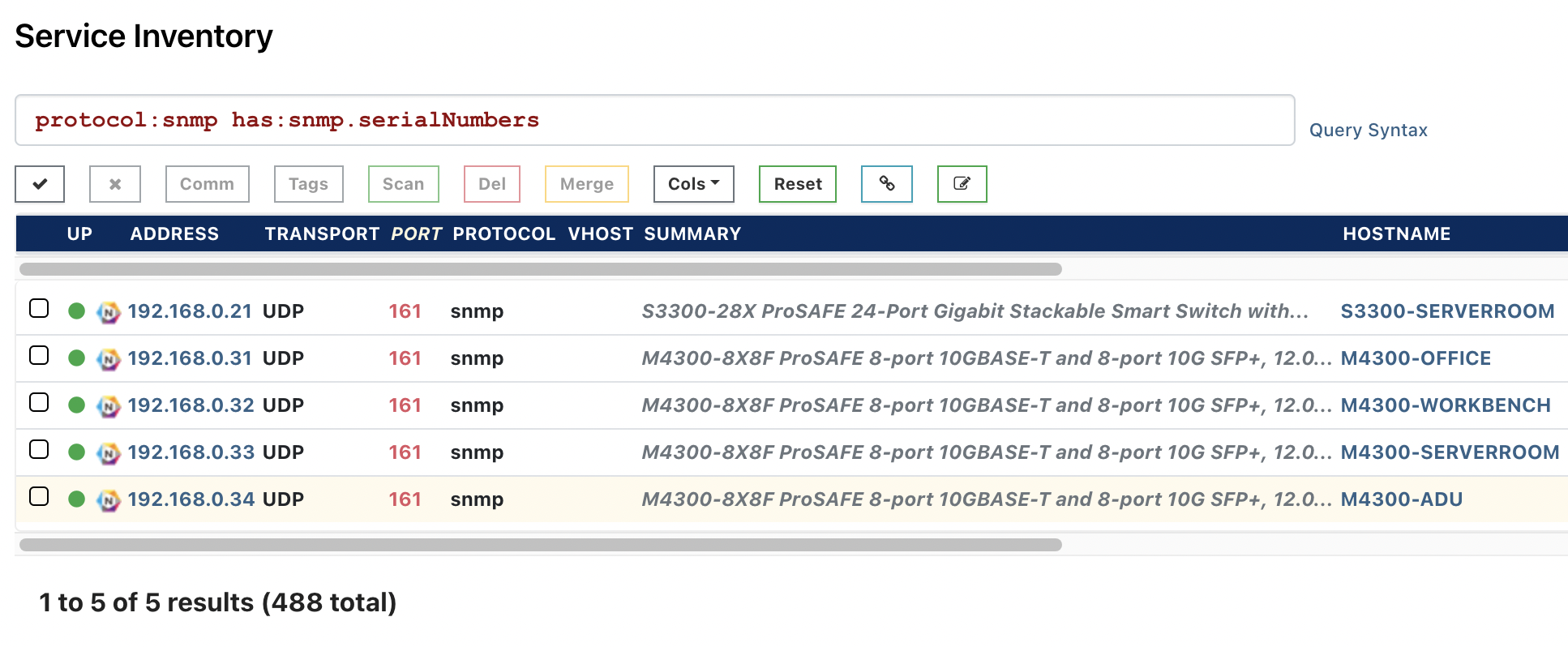
Collecting Device Serial Numbers and Asset Tags #
A few weeks ago, one of our customers asked us if we could pull serial numbers out of Cisco devices because this would be very useful for their MSSP business, and it's now included in Rumble. Pulling serial numbers remotely can be very useful to for support questions and to see if a device's warranty has expired and it should be replaced. You must have SNMP credentials (or the v2 community "public") configured for your scans for this query to work.
Read more about collecting serial numbers and asset tags
Bug Fixes & Improvements #
- The Inventory Search, Exports, and Reports are now significantly faster for large organizations.
- The Agents page will now flag any Windows Agents with an obsolete version of Npcap installed.
- The Dashboard now links to the top 5,000 results for asset types and service details.
- An issue with Crestron probe has been resolved that could hang concurrent scans.
- Rumble-provided queries can now be saved as per-account copies and modified.
- The 169.254.0.0/16 subnet is no longer ignored when processing scan results.
- The runZero Scanner now supports importing gzip-compressed scan data.
- The runZero Scanner and Rumble Agent now detect the CheckMK service.
- Partial site scans now consider ARP cache data from the entire site.
- VMware ESXi versions are now reported correctly.
Release Notes #
The complete release notes for v1.16.0 can be found in our documentation
If you haven't had a chance to try runZero before, or would like to play with the new features, sign up for a free trial and let us know what you think!
















