A few weeks ago, one of our customers asked us if we could pull serial numbers out of Cisco devices because this would be very useful for their MSSP business. We were able to update the scan engine quick and this feature is now included as of release 1.15.3. Pulling serial numbers remotely can be very useful to for support questions and to see if a device's warranty has expired and it should be replaced. You must have SNMP credentials (or the v2 community "public") configured for your scans for this query to work.
If taking old equipment off the network is your use case, Rumble can also show the device age based on the MAC address manufacturing date.
Finding Device Serial Numbers in Rumble #
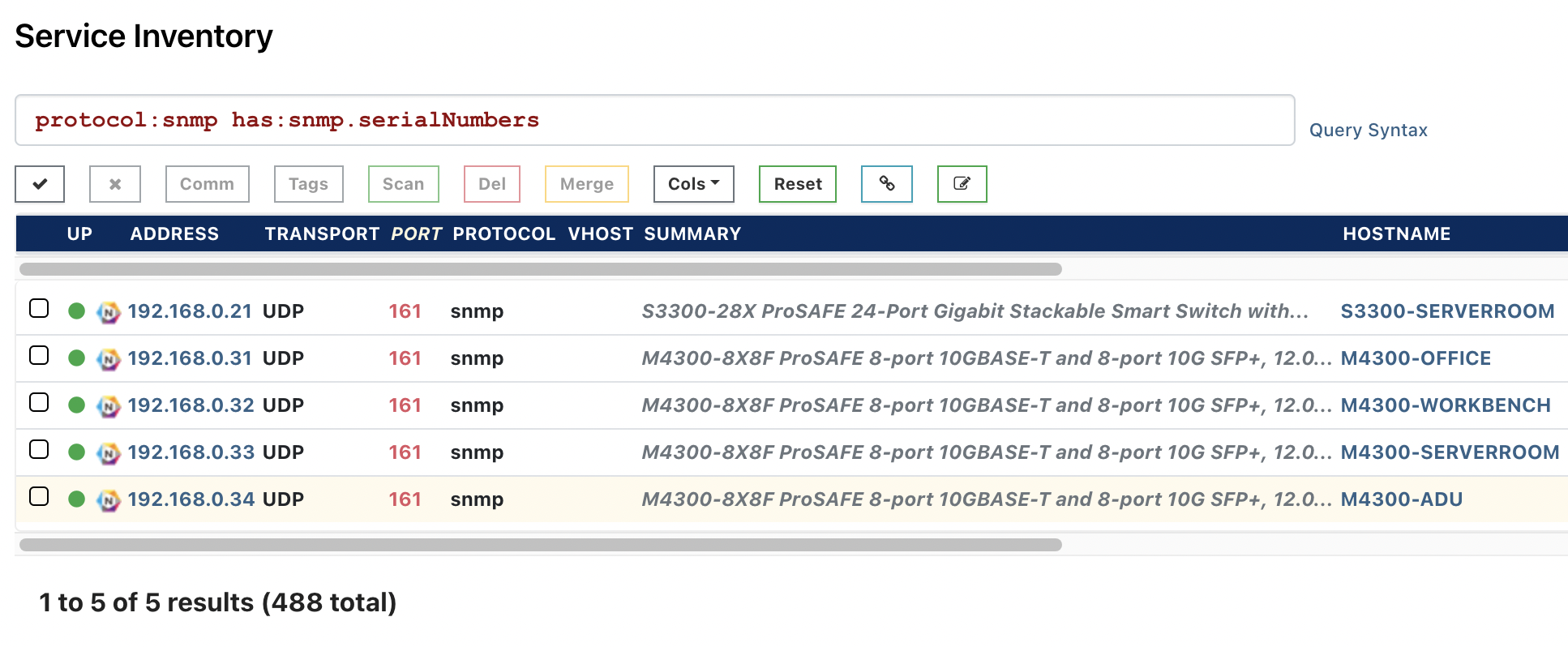
In your Rumble Console, go to Inventory in the left navigation and enter:
protocol:snmp has:snmp.serialNumbers
Clicking on a host in this list and scrolling down to the SNMP section, we see the serial number for this Netgear device:
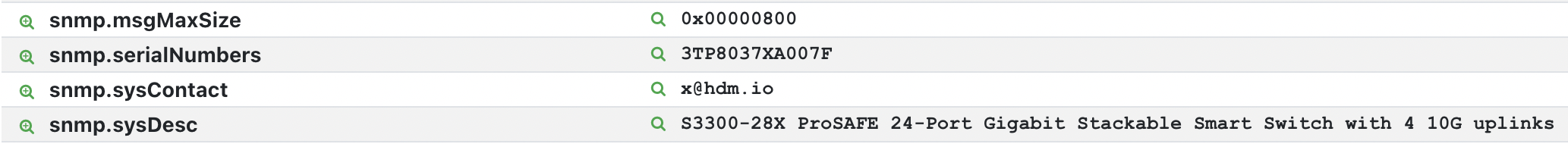
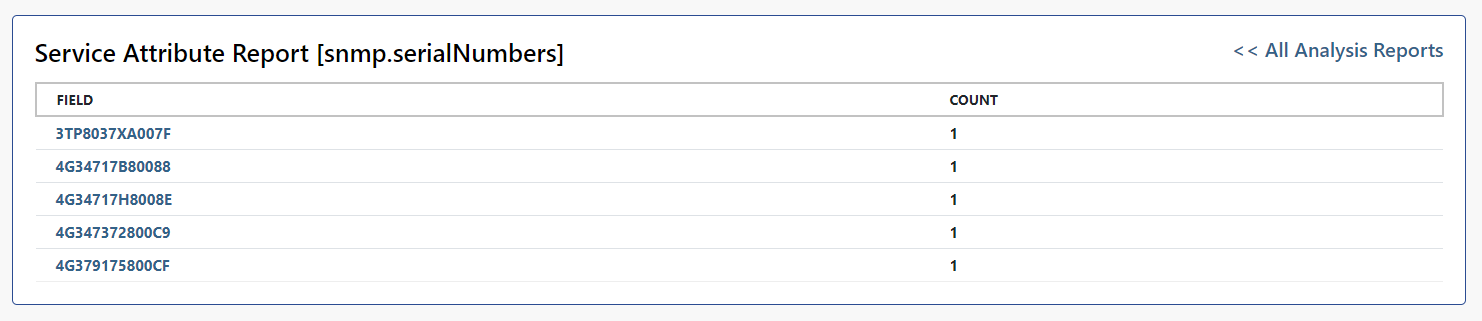
Clicking on the left-side search icon will produce a report of all serial numbers found across the organization:
Finding Asset Tags #
A similar feature enables you to find the asset tags of Dell iDRAC systems, which are stored in the snmp.sysName property. A good query to use to find these is:
protocol:snmp has:"snmp.sysName"
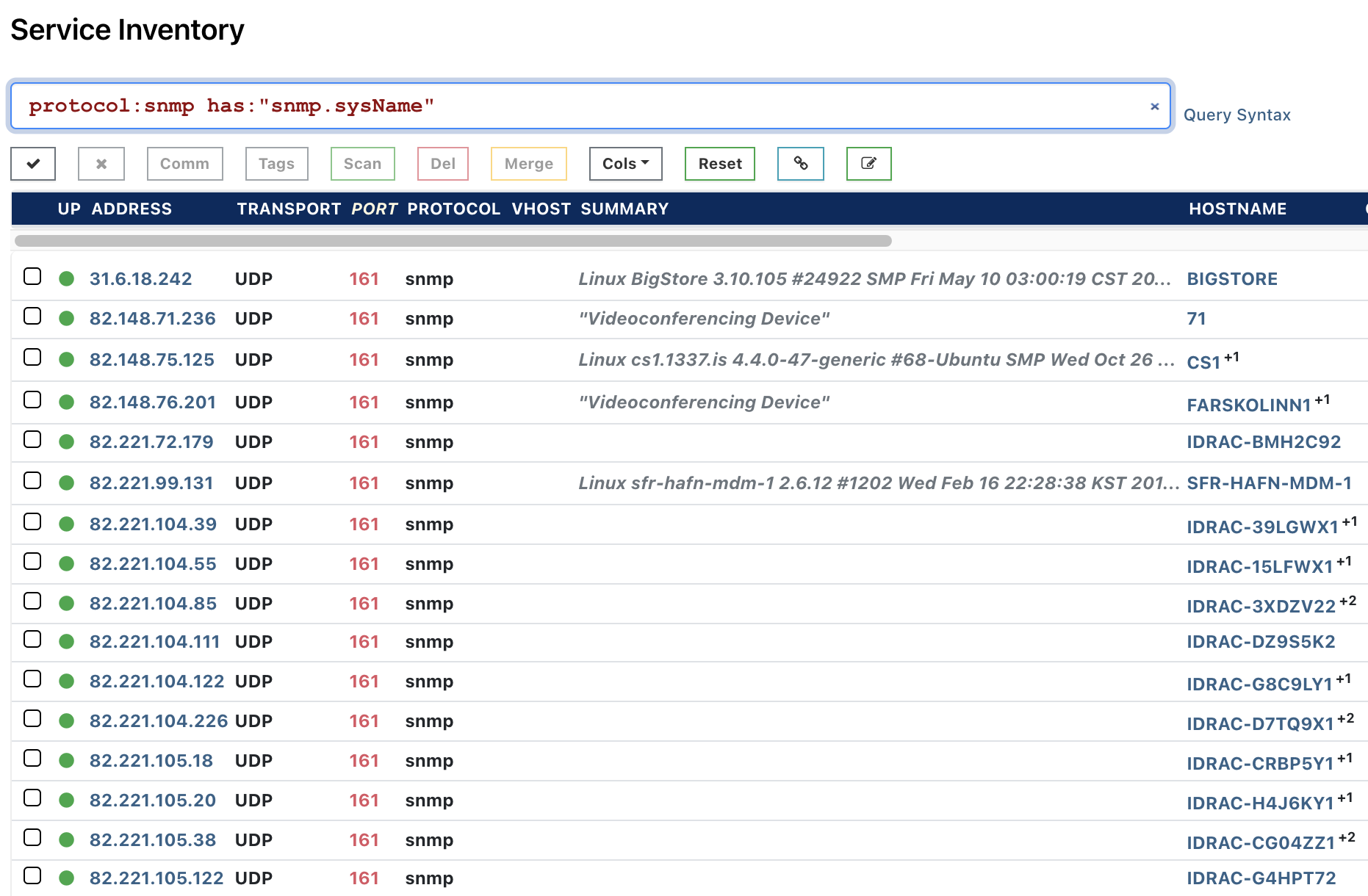
You can also filter for specific asset tags. A good query to find Dell iDRAC Asset Tags is:
protocol:snmp snmp.sysName:"drac-"
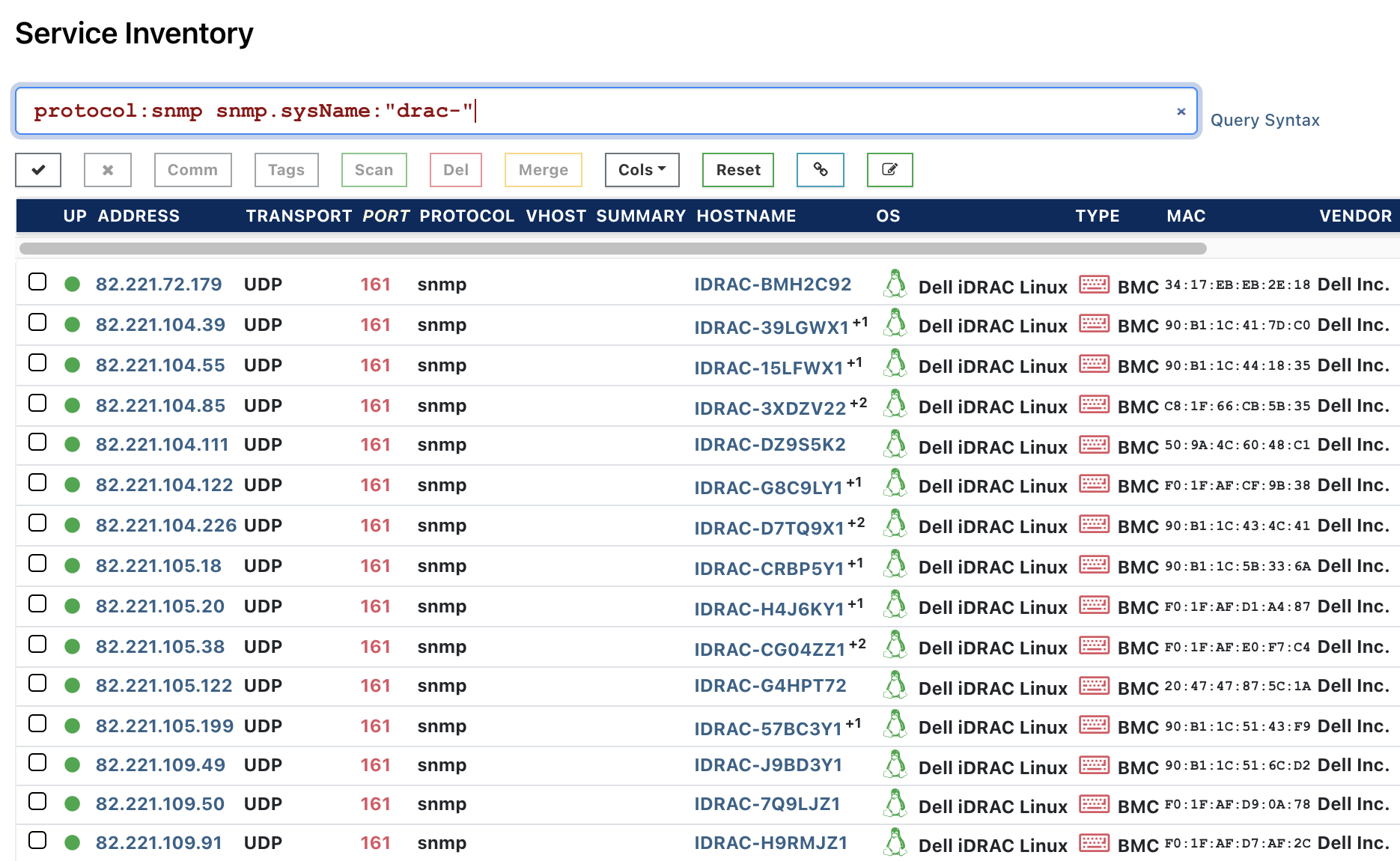
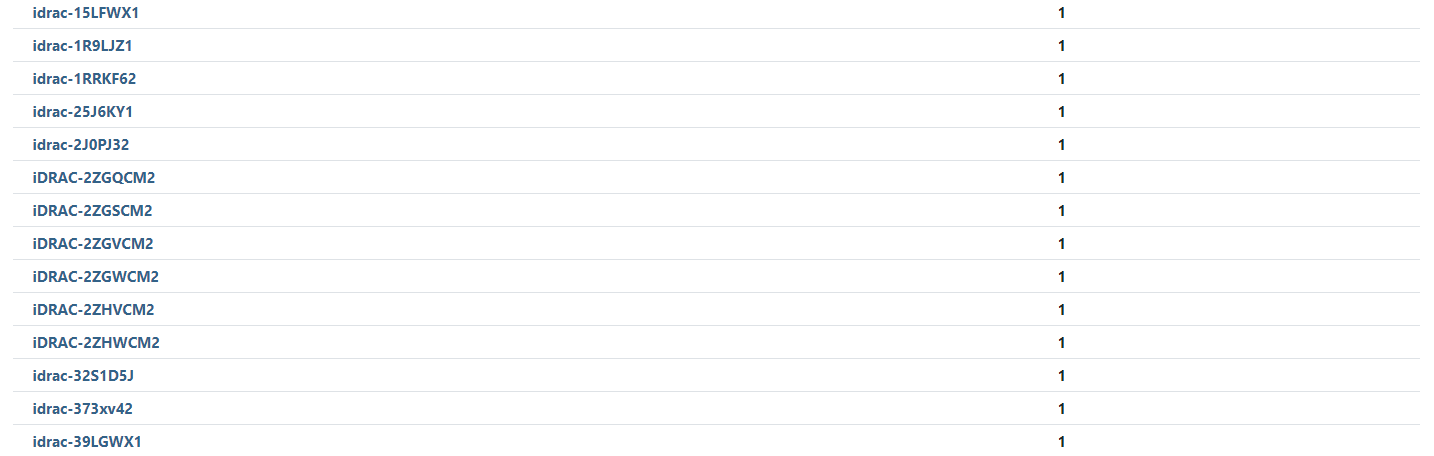
Clicking on the left-side search icon will produce a report of all SNMP system names across the organization, including the Dell iDRAC asset tags. These asset tags can be queried online from the Dell website to obtain the full specification of the hardware.
Exporting Cisco serials in Smart Net Total Care (SNTC) format #
For Rumble Enterprise users who need to manage Cisco device warranties or support warranty contracts, there is a new export format available that makes sharing data between Rumble and the Smart Net Total Care (SNTC) portal a lot easier. The Rumble Cisco SNTC CSV export is formatted specifically so you can export your data and directly import it into your SNTC portal.
In your Rumble Console, go to your inventory and filter only for Cisco devices (os:cisco). From the Export menu, you can see options to export all assets or queried asset results.
From the Export menu, choose Cisco SNTC CSV, located under Export Search Results.

This will only export the results from the os:cisco query. The export includes the host name, IP address, serial number, product ID, MAC address, system location, software type, and software version.
If you are not seeing any results, make sure that a valid SNMP v2 or v3 credential was provided as part of the discovery scan.
Try Rumble to Manage Your Network #
If you haven't had a chance to try runZero, or would like to find serial numbers & asset tags on your internal network, sign up for a free trial and let us know what you think!
















