Many organizations use an endpoint detection and response (EDR) solution to protect the assets on their network. However, EDR requires the use of an agent to secure their assets, and it can be difficult to know if all your assets are covered. After all, if you aren’t aware of unmanaged IT assets on your network, how can you know if you’re protecting that link to your network? Before we go over how runZero can help find endpoints that are missing the CrowdStrike Falcon Sensor, we’ll take a look at why having an EDR matters and how active scanning offers a solution for identifying missing IT assets in your network.
Why having an EDR matters #
Devices without an EDR solution lack alerts to immediate response capabilities, which creates risks for enterprise monitoring systems. Having EDR agents installed on as many endpoints as possible is an effective way to improve your security posture.
EDRs provide data on threat signals found across endpoints and continuously monitor events so that patterns or abnormalities can be identified. This allows you to investigate and respond to threats in a timely manner, mitigating risks, and boosting your security. The Mandiant IR reports indicate that threats are becoming more difficult to detect, so a quick response time can save money and help protect your data.
How active scanning can help #
Active scanners can identify both managed and unmanaged assets, providing you with the full scope of your network. This knowledge can help you answer questions like, "How many total assets do I have?" and "How many agents do I need to install for full coverage?"
runZero Explorers perform unauthenticated active scans powered by high-fidelity fingerprinting that provide a complete and accurate asset inventory. However, the runZero solution is more than just a scanner–it also integrates with a number of third-party solutions to enrich and round out your inventory. The runZero and CrowdStrike integration can show you which assets have an EDR agent installed, what version of the agent is installed, and which assets are missing an EDR agent.
Run through with runZero #
There are three core steps for runZero to identify endpoint assets that are missing the CrowdStrike Falcon Sensor.
Step 1: Run a network scan with runZero Explorer #
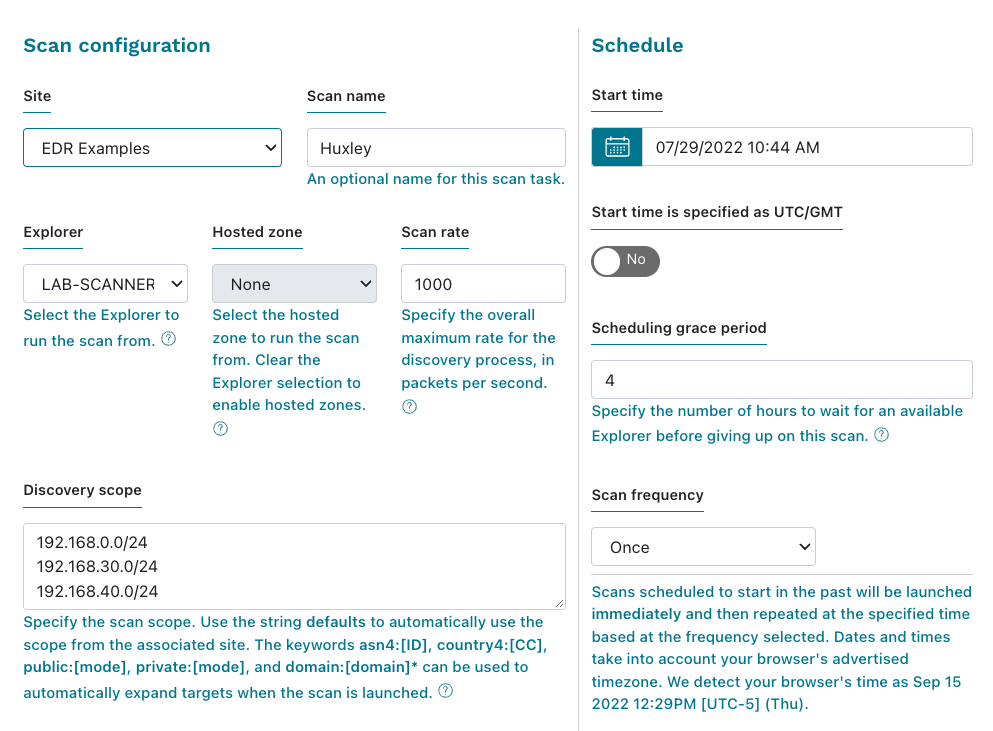
Log in to your runZero and go to the inventory. From there, go to the Scan dropdown and select Standard scan. This will take you to the Scan configuration page. Under site, you should select the site you want to populate with results. In this example, we used a site called EDR Examples. For your site, provide a descriptive name, so you can remember which assets have been grouped into it. Scroll down and click the Initiate scan button when you have finished configuring your scan (default settings are usually fine). Confirm your scan and you’ll have an active scan going.
Step 2: Connect to CrowdStrike Falcon API #
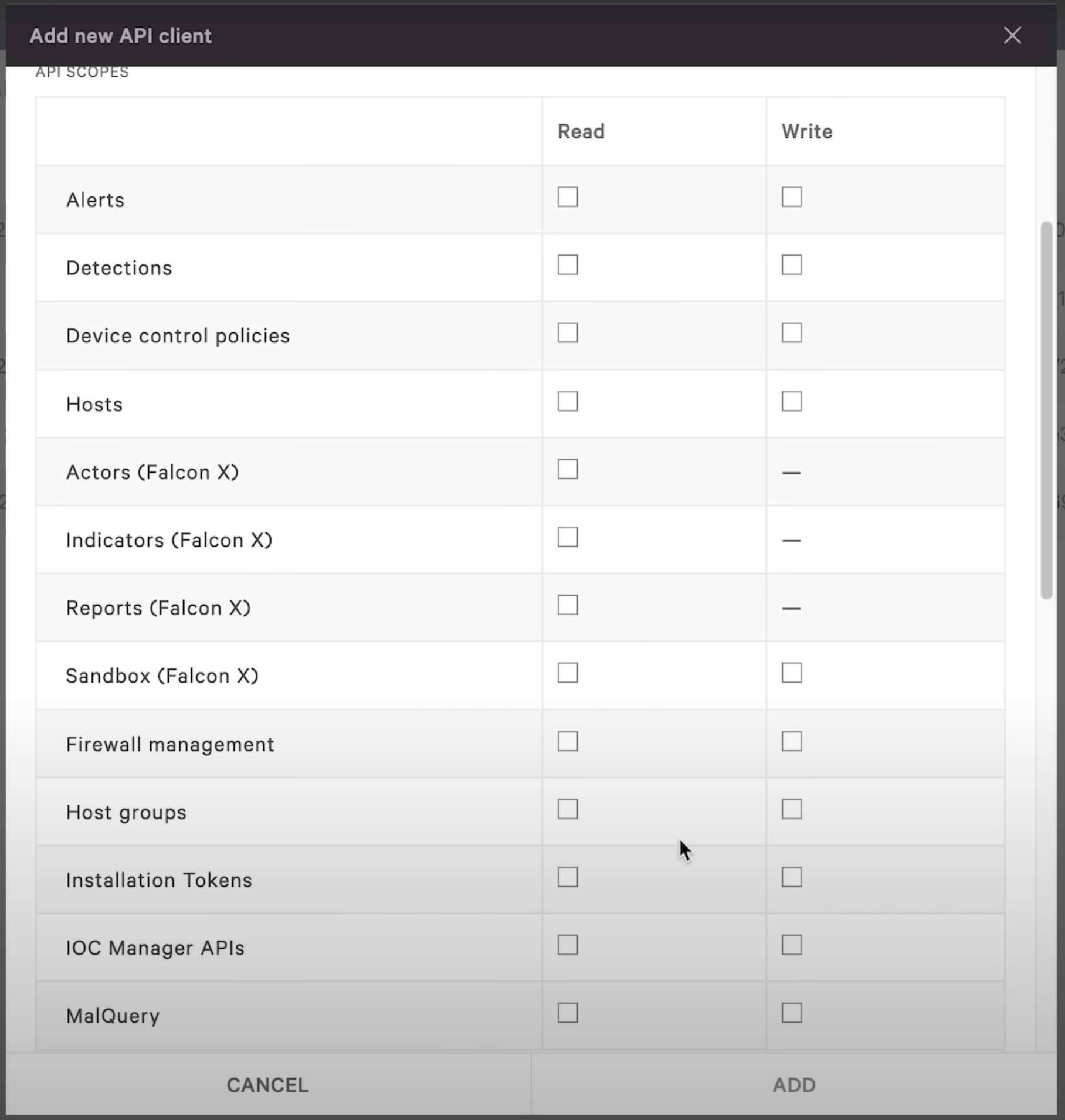
Next, you need to connect runZero to the backend of your EDR, which is CrowdStrike Falcon in this example. Log in to the Falcon platform as an admin and add a new API key from the API Clients and Keys area. You will need to name your key, provide a description, and specify the required the scopes. In order for this integration to work properly, you’ll need to allow read access to hosts and host groups under the API scopes section of the new API key.
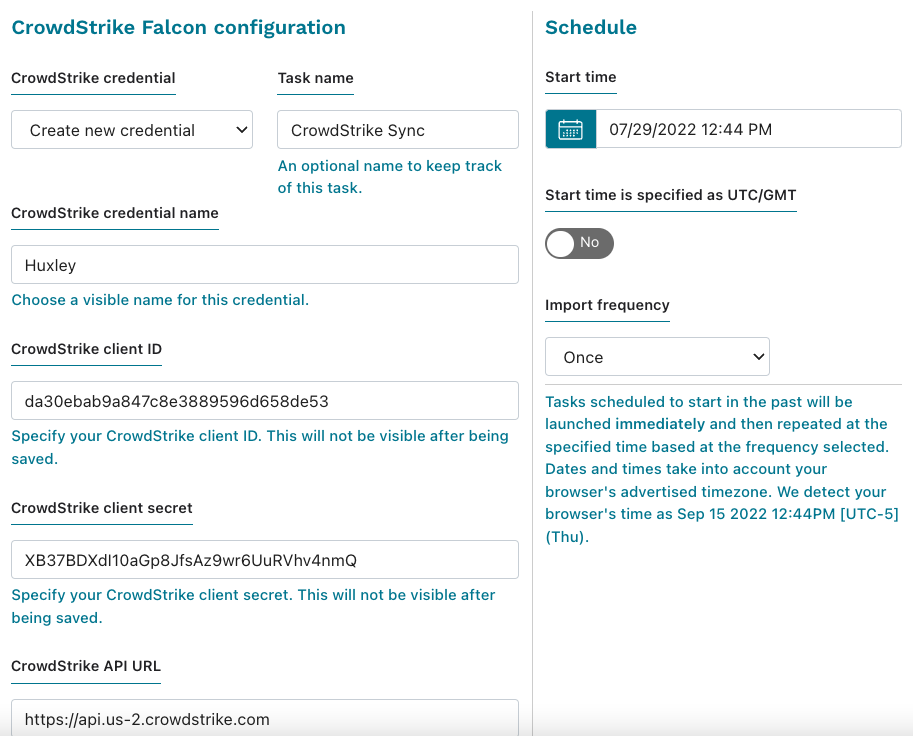
After the key has been created, go back to your inventory, find the Connect dropdown, and select CrowdStrike. Create a new credential and copy the client ID, client secret, and API URL that you created earlier, then have your site match your previous scan. If you need to, you can create a schedule to sync the data. Activate the connection when you are ready. This will create two active tasks, the scan and the integration.
Step 3: List out all agents missing the EDR agent #
Now that your scan has completed, your inventory has a list of live assets on your network. From the Queries Library, find the predefined query for CrowdStrike. Running this query will show you a list of laptops and desktops missing the CrowdStrike EDR name attribute.