Latest TP-Link router vulnerability #
A vulnerability has been disclosed in TP-Link Archer AX50 routers. This vulnerability would allow a remote, unauthenticated attacker to execute arbitrary code with root privileges on vulnerable devices.
This vulnerability has been designated CVE-2025-40634 and has a CVSS score of 9.2 (critical).
What is the impact? #
Successful exploitation of this vulnerability would allow an attacker to execute arbitrary code on vulnerable routers, allowing them to take complete control of affected devices.
Are any updates or workarounds available? #
Reports indicate that versions of the Archer AX50 firmware after 1.0.15 are no longer vulnerable, but this has not yet been confirmed by TP-Link.
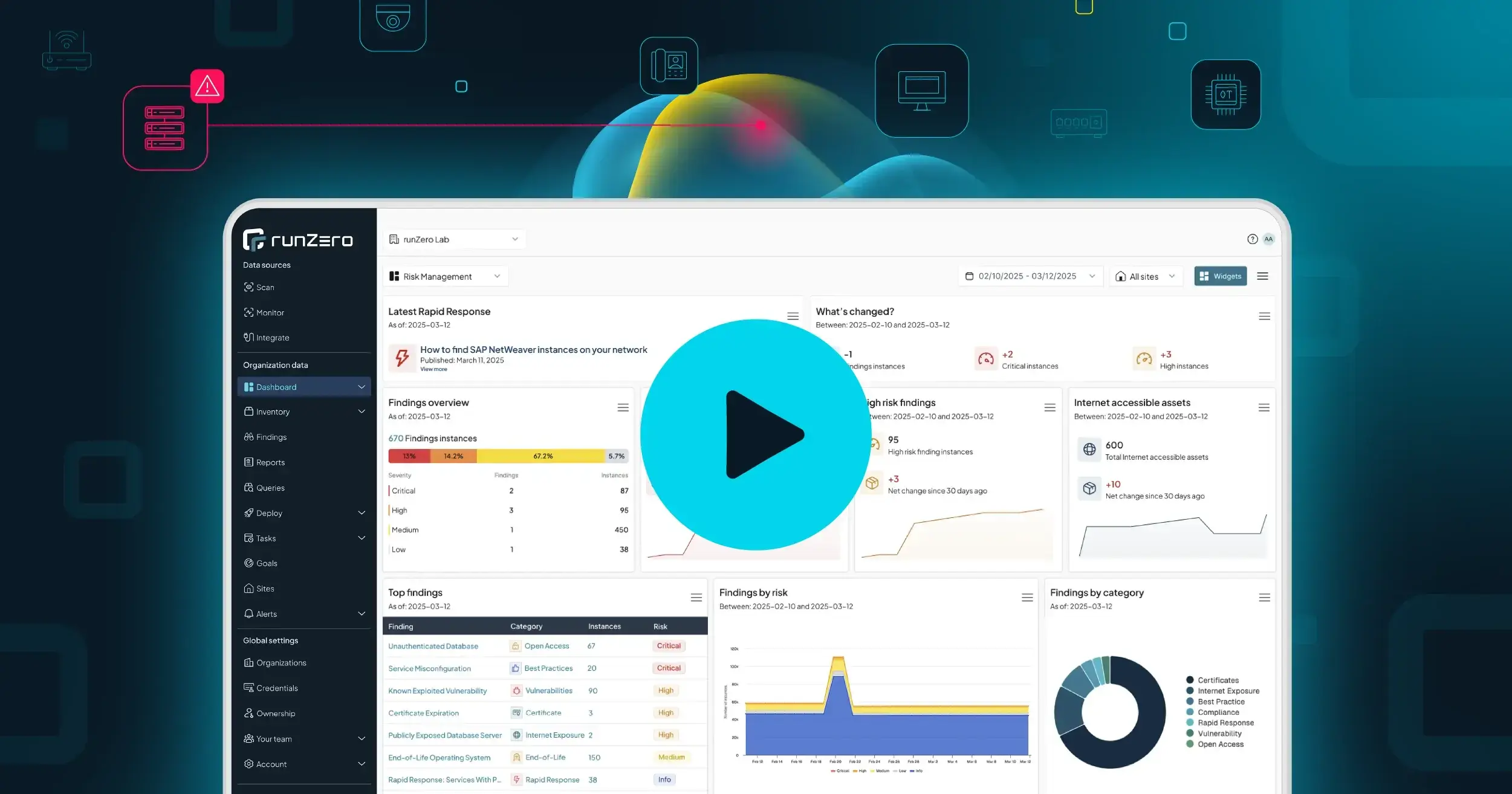
How do I find TP-Link Archer AX50 routers with runZero? #
From the Asset Inventory, use the following query to locate potentially impacted assets:
hw:="TP-Link Archer AX50"