Overview #
Today's update comes with two significant features: Analysis Reports and the Query Library.
This work brings practical analytic capabilities to the inventory data and makes it easier than ever to create and share custom queries with your team and the wider community.
Analysis Reports #
Analysis Reports are now accessible via the Explore link in the navigation menu. This section includes the three existing reports (Topology, Subnets, Bridges) and introduces two new ones.
The Domain Membership report uses information gathered from the NTLMSSP responses of the SMB and RDP protocols to identify machines that are not joined to the primary domain. This report can quickly highlight unmanaged, misconfigured, and third-party systems.
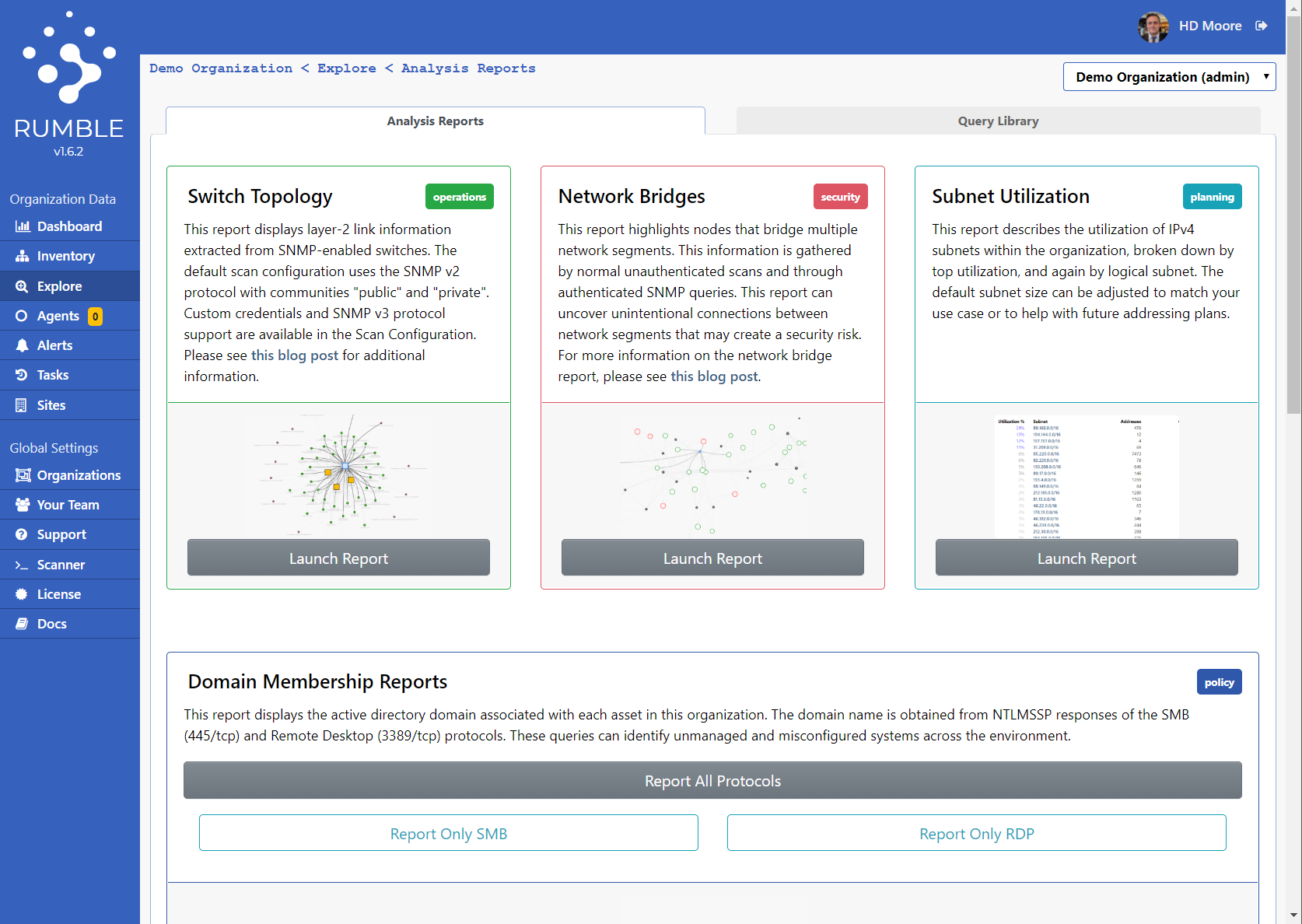
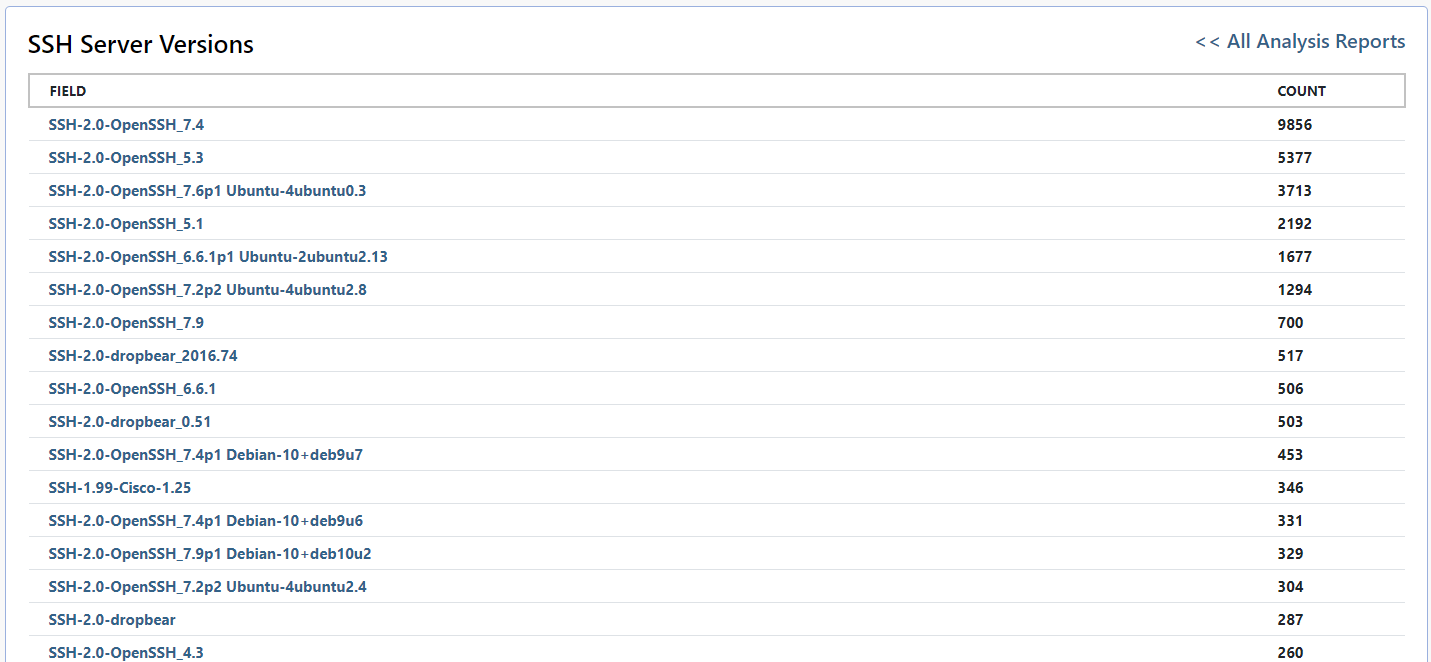
The Service Attribute report offers a combination of pre-built and configurable queries for unique service attributes. This report can highlight the most and least common values of a given attribute, using an optional attribute filter.
The pre-built service attribute queries cover two-dozen common and noteworthy service attributes.
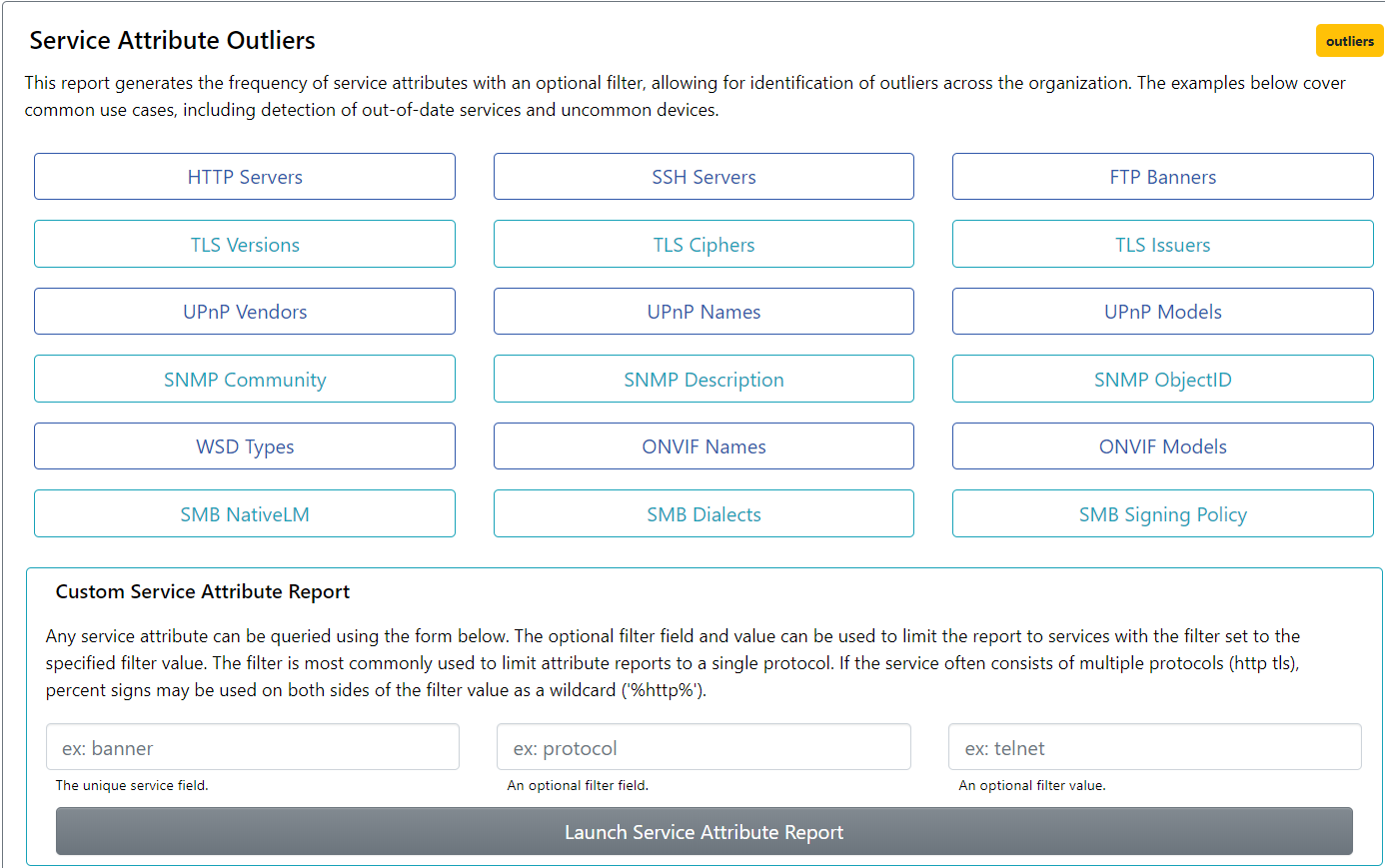
This report provides one of the most interesting perspectives of a network. Looking at the top entries for a given attribute, as well as the long tail of unique entries, can highlight both the intended configuration and the exceptions in a way that is otherwise difficult to see.
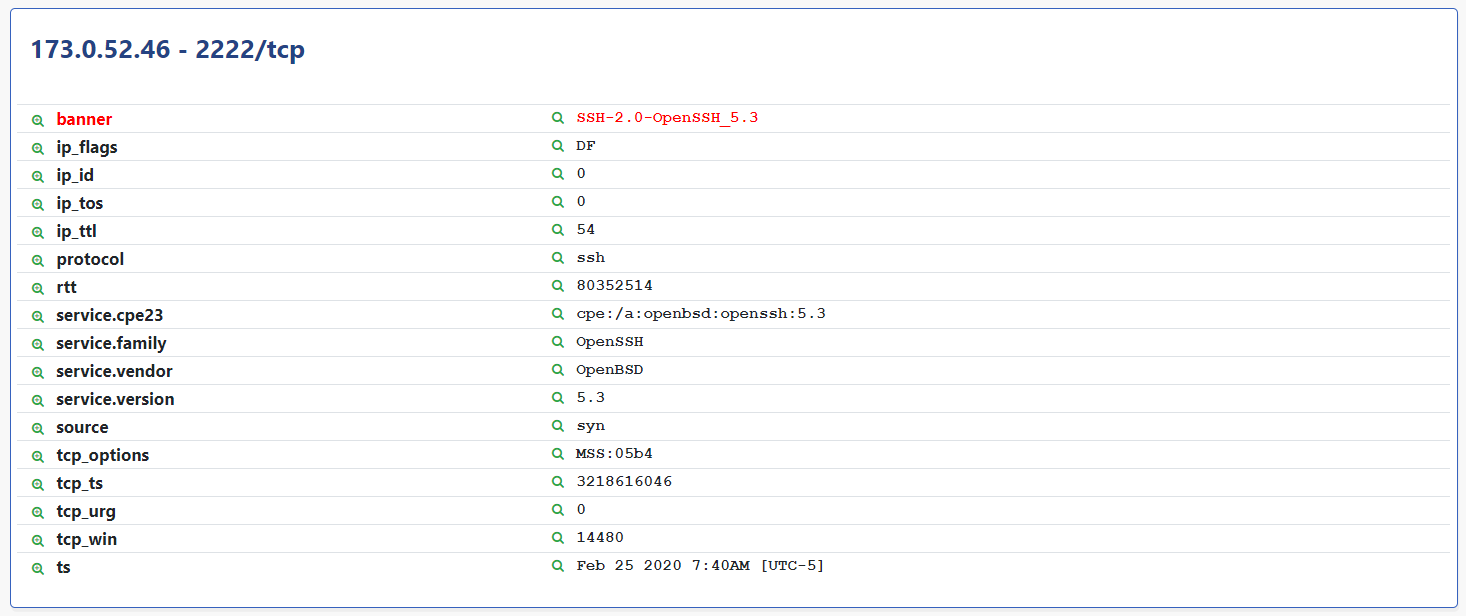
This report can be run against any attribute from the Analysis Reports page or via the Asset Detail page by clicking the green magnifying glass icon next to an attribute name.
Keep in mind that these queries only cover Live Assets, are limited to 1,000 results, and can be a little slow depending on the number of assets involved.
Query Library #
The Inventory search provided by Rumble keeps getting better with each release, but can be tricky to get used to, and the right solution isn't always obvious. To help folks become familiar with the query language and to make it easy to share useful queries, this release introduces the Query Library. Accessible via the tab in the Explore section, this library provides pre-built queries for common tasks and allows new saved queries to be created, imported, and exported.
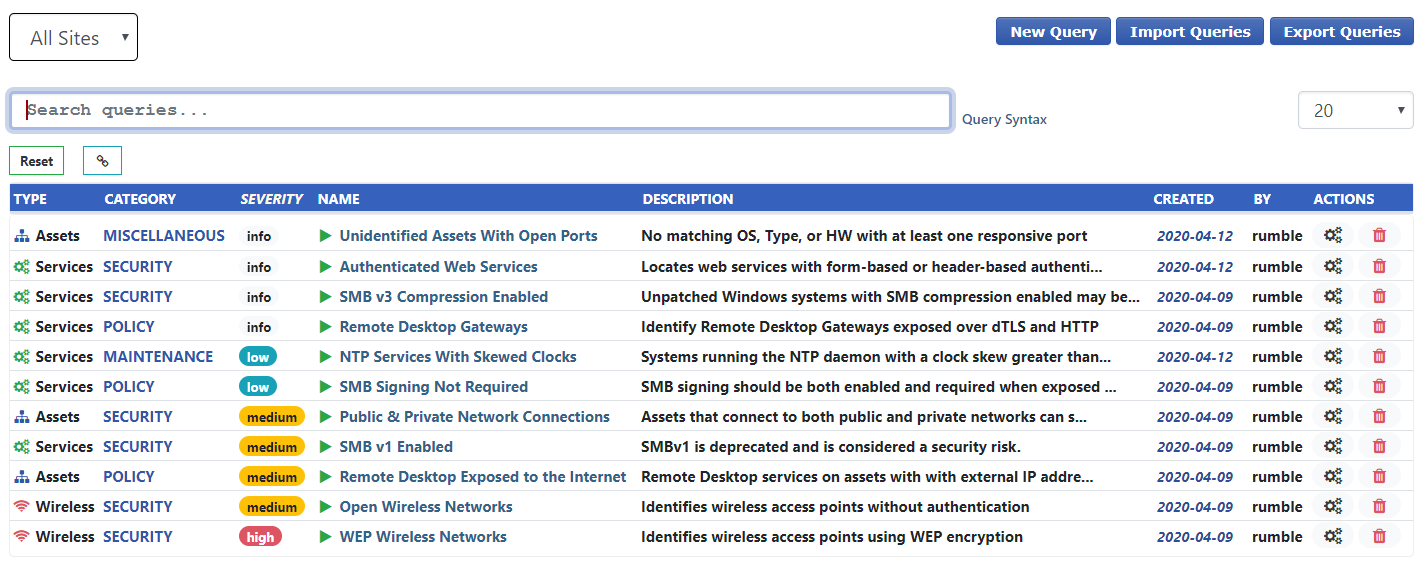
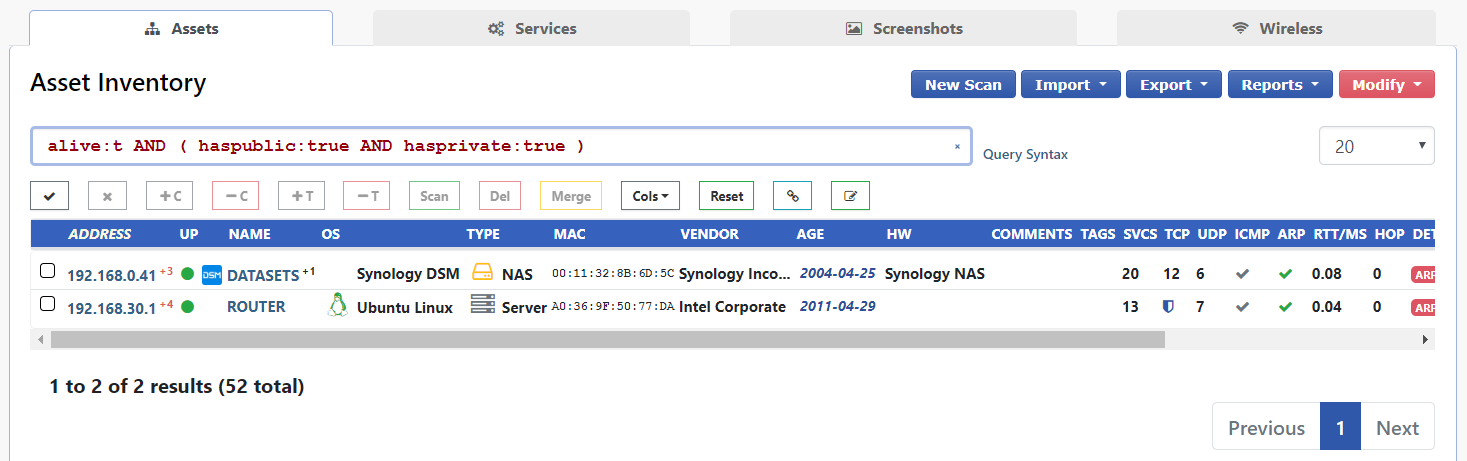
The Public & Private Network Connections query quickly finds any asset that might be bridging the internal network to the open internet.
If you come up with an awesome query and want to see it in the default library, please drop us a line and we can make that happen. We hope you find these updates useful and we would love your feedback.
If you haven't had a chance to try runZero before, or would like to play with the new features, sign up for a free trial and let us know what you think!
-HD
















