The Ripple20 vulnerabilities identified by JSOF impact millions of devices running the Treck operating system, many of which have not and will not receive updates. Finding exposed devices can be tricky since many of the device types (battery backups, printers, etc) are often excluded from normal vulnerability scans, sometimes automatically. Fortunately, Rumble's scan engine is safe to use with embedded devices of all types and already collects enough information to identify many affected systems.
To support this effort, we have added two new entries to the Query Library:
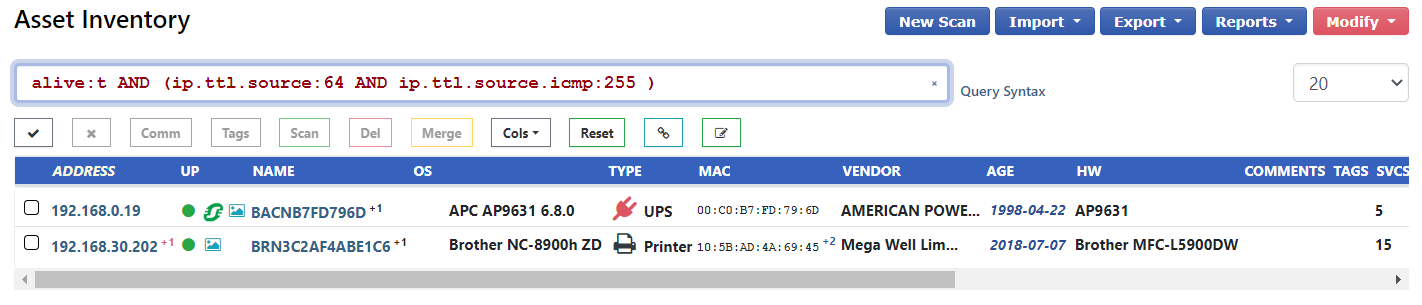
These queries use the IP TTL differences between the ICMP and TCP replies as well as a specific HTTP server banner to find Treck OS devices.
Please note that the IP TTL query may include false positives as quite a few firewalls along with a handful of non-Treck devices exhibit the same behavior.
Happy Scanning!
-HD
If you haven't had a chance to try runZero before, or would like to play with the new features, sign up for a free trial and let us know what you think!
















