-
Exposure Management Platform
Complete security visibility across IT, OT, IoT, cloud, mobile, and remote assets.
-
Asset Fingerprinting & Contextualization
runZero employs a multi-faceted approach to perform high-fidelity fingerprinting for IT, OT, and IoT assets – no agents or credentials required.
-
Integrations
runZero seamlessly integrates with a wide variety of tools, enhancing network visibility, enriching asset data, and uncovering control gaps.
-
Community Edition
Our completely free version of the runZero Platform is ideal for home use and environments with fewer than 100 assets.
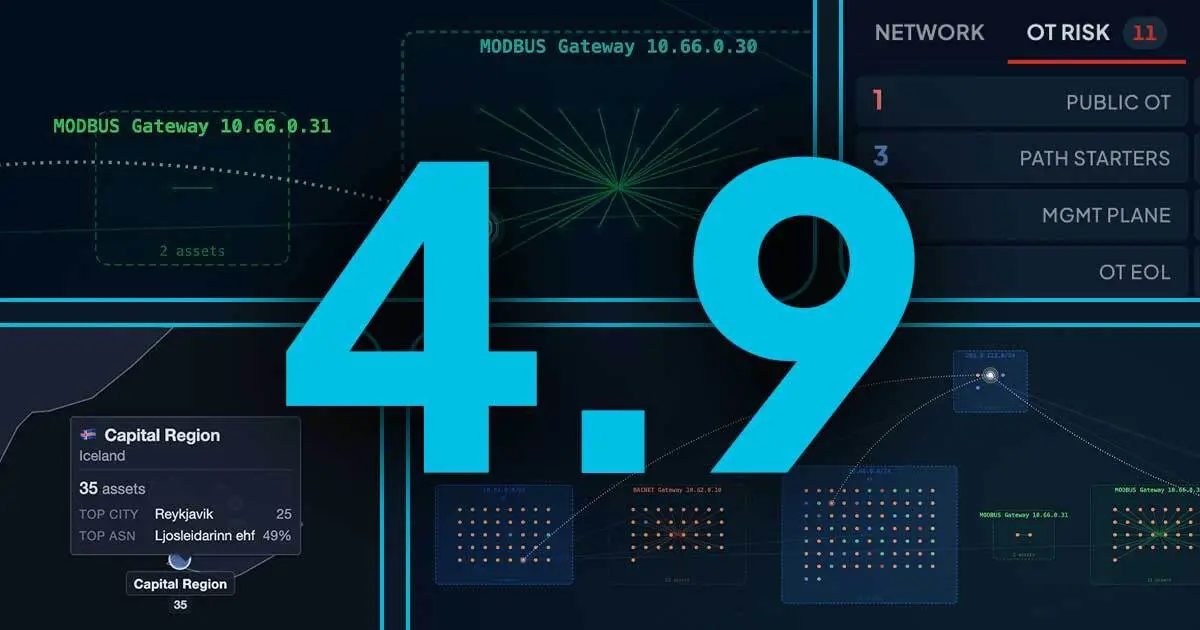
Advanced toplogy, attack path mapping & deep OT intelligence!
With our latest release you can see exactly how an attacker could move through your network, allowing you to harden critical choke points and remediate exposures before they are exploited. Plus we expanded our OT telemetry to provide deep insights into the role and risk profile of every device.
-
Solutions
Gain visibility, control the unknowns, and ensure compliance with confidence.
-
Regulatory Compliance
Ensure compliance and stay resilient against evolving cyber threats.
Join HD Moore on June 25 for a conversation on securing the modern IT/OT attack surface.
runZero Founder & CEO HD Moore and GigaOm Analyst Chris Ray will explore new methods for hardening OT defenses & share key insights from the just-released OT Radar.
-
Resource Center
Dive into a treasure trove of resources to expand your exposure management knowledge.
-
runZero Research
Explore the world of exposure management through the runZero lens.
-
runZero Blog
See what's happening at runZero and read up on the latest ideas, opinions, and articles from our experts and researchers.
-
Support Resources
Everything you need to maximize your experience with the runZero Platform.
Watch the runZero Day replay!
The inaugural runZero Day livestream was one for the books! From the inner workings of the CVE program and modern cyber journalism to the realities of OT security and the startup investment ecosystem, our wonderful guests helped us cover the trends that are defining our industry.
-
Our Customers
Our customers are everything. We're super proud to be trusted by leading organizations around the globe to help them improve their security.
-
Case Studies
See how runZero has empowered security teams to take control of their networks, uncover their unknowns, and save significant time and money.
-
Testimonials
Read reviews of the runZero Platform and see how teams have improved their security with our technology.
Case Study: How runZero established North Carolina’s K–12 exposure management program
Learn how runZero became the foundation for exposure management across 343 North Carolina Public School Units.
-
About Us
Wondering who the heck are these people? Meet the team and get the story behind runZero... once upon a time called Rumble.
-
Events
Track down runZero Yetis in the wild! Join us in-person or virtually at one of our upcoming events.
-
Investors
Meet the cybersecurity investors, trailblazers, and innovators who help us navigate our journey and the evolving security landscape.
-
Newsroom
Read the latest articles, announcements, and press releases from runZero.
-
Careers
Want to join our forces? We're looking for bright minds and passionate souls who want to write the next chapter in exposure management.
Meet runZero at Infosecurity Europe 2026!
Join us June 2-4 in London for Infosec! If you plan to be there, we’d love you to meet with our executive team and technical experts. We're ready to explore security challenges, provide customized product demos, chat about our product roadmap, hear about your experience with runZero, and more!
-
Infinity Partner Program
See how we can work together to provide best-in-class security solutions and outcomes for our joint customers.
-
Partner Directory
Explore our directory of trusted (and awesome) partners.
-
Partner Sign In
Sign in to our Infinity Partner Portal.
Join our Infinity Partner Program
Designed with a partner-first mindset, the runZero Infinity Partner Program offers incredibly valuable resources, relationships, and rewards to partners who choose to grow their business with us.