Latest OMI software vulnerability #
Details on vulnerabilities present in some Azure Linux VMs, collectively referred to as "OMIGOD", came to light this week via published research by the cloud security folks at Wiz.io. These vulnerabilities are found in the Open Management Infrastructure software that Microsoft automatically installs in certain Azure Linux VMs. They include an unauthenticated root-level code execution vulnerability (CVE-2021-38647; CVSS base score of 9.8) and three privilege escalation vulnerabilities:
While patches were made last month for OMIGOD vulnerabilities, there have been reports this week that some new Azure Linux VM instances are still provisioning the vulnerable OMI code. Microsoft has provided guidance on ensuring folks are running the latest, patched OMI software. Wiz provided remediation recommendations via limiting network access to OMI WSMAN ports 5985, 5986, and 1270.
Fingerprinting WSMAN #
We recently added support to the v2.6.4 runZero Explorers and scanners to discover WSMAN services on your network-connected assets. Web Services-Management (WSMAN) is a protocol designed for the management of systems and services, and it can be found in a number of technologies, including Microsoft's WinRM and some BMC devices. The OMI WSMAN implementation is where the OMIGOD vulnerabilities exist, and Rumble scans can identify the vendor and version of a WSMAN service with exposed ports.
Pulling WSMAN details can be done via POST request of a short SOAP message containing the wsmid:Identify operation. A successful reply to this request will arrive in the form of a SOAP message containing product details. While adding this capability, we discovered that the OMI WSMAN implementation does not reply to HTTP requests unless a valid Content-Type header is present in the request, which was unexpected.
How to find assets running OMI services #
Once you have scanned your assets with a v2.6.4+ explorer or scanner, navigate to your Services Inventory and use the following pre-built query to identify systems running the OMI WSMAN service:
_asset.protocol:wsman AND wsman.productVendor:="Open Management Infrastructure" AND (wsman.productVersion:=0.% or wsman.productVersion:=1.0.% or wsman.productVersion:=1.1.% or wsman.productVersion:1.2.% or wsman.productVersion:=1.3.% or wsman.productVersion:=1.4.% or wsman.productVersion:=1.5.% or wsman.productVersion:=1.6.0-% or wsman.productVersion:=1.6.1-% or wsman.productVersion:=1.6.2-% or wsman.productVersion:=1.6.3-% or wsman.productVersion:=1.6.4-% or wsman.productVersion:=1.6.5-% or wsman.productVersion:=1.6.6-% or wsman.productVersion:=1.6.7-% or wsman.productVersion:=1.6.8-0)
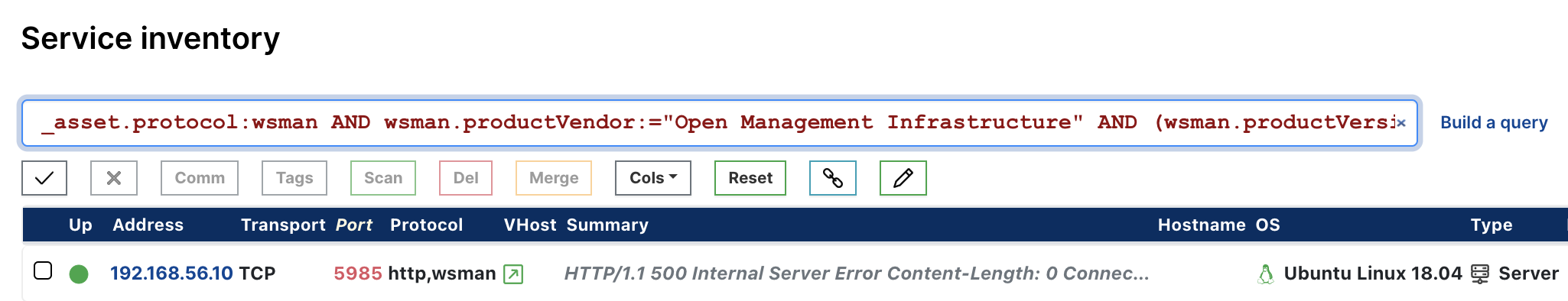
As always, any prebuilt queries we create are available from our Queries Library. Check out the library for other useful inventory queries.