Latest Netatalk vulnerability #
A critical vulnerability in the Netatalk open source file server software was found in some popular network attached storage (NAS) devices. Netatalk provides services for the deprecated AFP (Apple Filing Protocol, formerly known as Appletalk Filing Protocol), and runs on a number of operating systems including Linux, FreeBSD, OpenBSD, NetBSD, and Solaris.
Researchers with NCC's Exploit Development Group discovered and disclosed this vulnerability, which has been assigned CVE-2022-23121 and dubbed "Mooncake".
What is the impact of Mooncake? #
'Mooncake' requires a writable file share for exploitation, but does not require authentication, yielding root-level remote code execution. The report identified some popular NAS devices, including products in Western Digital's MyCloud line, as running vulnerable versions of Netatalk in their distributed firmware.
Are updates available for the vulnerability? #
Multiple vendors have made patches available to address the vulnerability. Project maintainers of Netatalk released version 3.1.13, which also included a number of other vulnerability fixes for "critical" and "high" scored CVEs. Users should either upgrade to this new release or consider disabling/removing Netatalk altogether in favor of SMB or NFS for network file shares. (Apple themselves no longer support AFP.) Western Digital also released updated firmware (v5.19.117) for affected devices, which removes Netatalk altogether from their firmware (and patched a number of other vulnerabilities). Western Digital recommends users upgrade to the latest firmware release and switch over to using SMB for network file sharing.
Synology NAS appliance and QNAP may be vulnerable #
On April 28, 2022, Synology announced that some of their network-attached storage (NAS) appliances may be exposed to attacks exploiting Netatalk vulnerabilities. In addition to CVE-2022-23121 , Synology called out three vulnerabilities CVE-2022-23125, CVE-2022-23122, CVE-2022-0194 that allow attackers to run arbitrary code remotely on unpatched systems. Another NAS appliance maker, QNAP, also urged their customers to disable AFP until they're able to resolve the Netatalk vulnerabilities.
Security updates for some of the impacted products may not be available yet. Affected customers are advised to check for updates frequently and apply them as soon as they are available.
How do I find potentially vulnerable Netatalk instances with runZero? #
From the Asset Inventory, use the following pre-built query to locate assets within your network that could be running vulnerable versions of Netatalk:
port:548 AND (type:nas OR hw:"Western Digital")
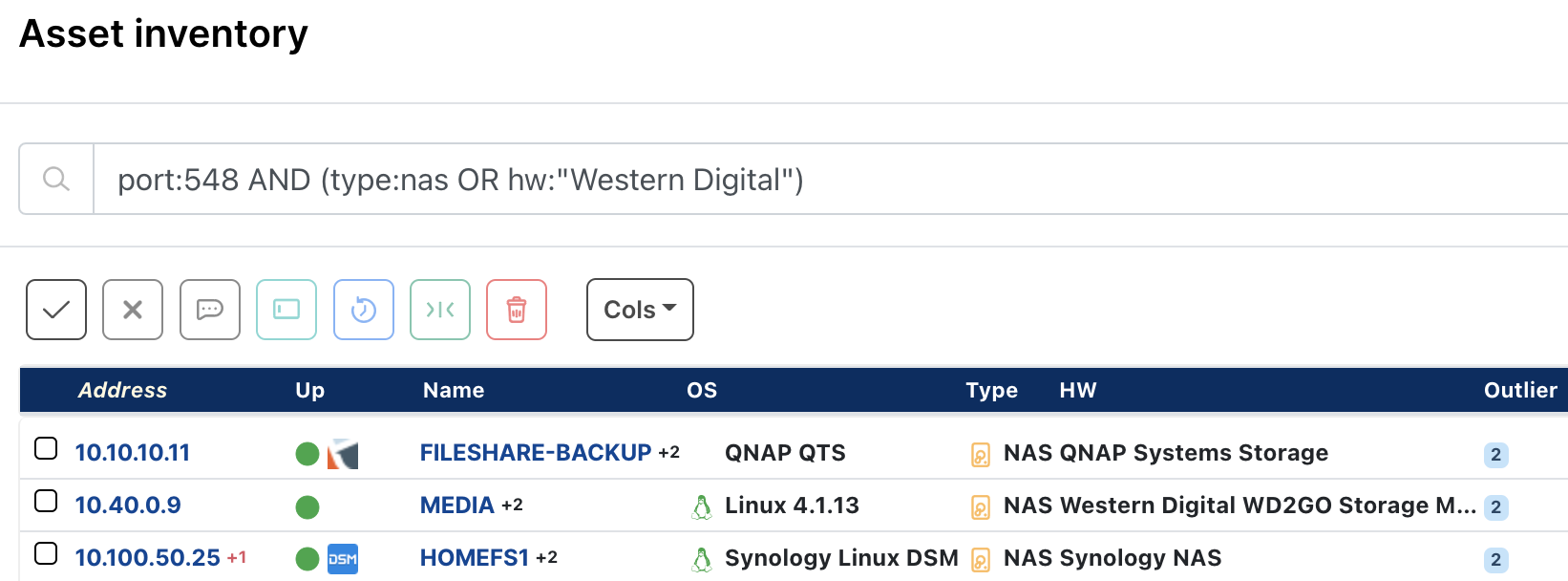
This query will surface NAS and Western Digital assets which appear to be running an AFP service, providing a starting point for additional investigation and triage.
As always, any prebuilt queries we create are available from our Queries Library. Check out the library for other useful inventory queries.