runZero can help you build an up-to-date asset inventory and search for assets that may be affected by Log4J vulnerabilities, such as Log4shell. runZero is not a vulnerability scanner, but you can share runZero’s results with your security team for investigation and mitigation.
What is Log4j? #
Internet discussion was abuzz on December 9th about an 0-day vulnerability that can yield remote code execution (RCE) in Apache’s popular Log4J logging library for Java. This particular vulnerability — tracked as CVE-2021-44228 with the maximum “critical” CVSS score of 10 — resides in Log4J’s lookup capability, combined with JNDI (Java Naming and Directory Interface). This issue is widespread because many developers were unaware that Log4J was dangerous to use with unfiltered input.
The most significant impact is that an attacker can cause a string to reach the logger, that when processed by Log4J, executes arbitrary code. The first examples of this used the ${jndi:ldap} path, which could lead to arbitrary code being loaded from a remote URL. This path is partially mitigated by the use of newer Java runtimes that block the URL-based class loader by default. Unfortunately, a modern version of Java may not be enough to prevent exploitation, as the application itself may expose classes that can be used to run arbitrary code.
While Apache released fixes to CVE-2021-44228 in Log4J version 2.15.0, it was discovered these fixes were “incomplete in certain non-default configurations”, allowing for exploitation in certain circumstances (tracked as CVE-2021-45046 (with a “critical” CVSS core of 9.0), leading to a Log4J 2.16.0 release to address CVE-2021-45046.
Following that release, a new vulnerability was raised which can yield a denial-of-service attack via infinite recursion. Tracked as CVE-2021-45105 (and with a “high” CVSS score of 7.5), this vulnerability appeared to affect Log4J versions 2.8 through the most recent 2.16.0 release, and was fixed in versions 2.17.0 (for Java 8) and 2.12.3 (for Java 7).
Then on December 28th, security researchers at Checkmarx published findings of another RCE present in Log4J 2.17.0, one which requires the attacker have permissions to update the logging configuration and, when successful, can yield RCE. Tracked as CVE-2021-44832 (and with a “medium” CVSS score of 6.6), Apache released a fix for this latest vulnerability in Log4J versions 2.17.1 (for Java 8 and later), 2.12.4 (for Java 7), and 2.3.2 (for Java 6).
Impact of Log4J vulnerabilities #
The broad popularity of Log4J–coupled with the relative ease of exploiting this vulnerability–creates potential conditions for far-reaching exploitation (similar to Shellshock).
Google’s security team have scanned the contents of Maven Central and found over 35,000 affected packages, amounting to over 8% of those in the repository. Any application making use of the affected packages as dependencies may be vulnerable.
Affected applications include Elastic Search, Elastic LogStash, GrayLog2, Minecraft (client and server), Neo4J, many Apache projects (Druid, Dubbo, Flink, Flume, Hadoop, Kafka, Solr, Spark, Struts, Tapestry, Wicket), many VMware products (Horizon, vCenter, vRealize, HCX, NSX-T, UAG, Tanzu), Grails, and dozens if not hundreds of others. Log4J versions since 2.0 are reported to contain this vulnerability, which was originally disclosed to Apache several weeks ago by the security team at Alibaba Cloud.
How to stay on top of Log4Shell #
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) recently created a repo for tracking products/applications affected by Log4Shell, which will likely become the most reliable, long-term source-of-truth.
Note: runZero components–cloud platform, self-hosted, explorer, and CLI scanner–are not affected by this issue.
Patching and remediating vulnerable Log4J instances will continue to be an ongoing effort. Recently, an advanced persistent threat (APT) group has been observed installing rootkits in Windows systems vulnerable to Log4Shell. In fact, even some recent Log4J patching efforts themselves have led to other problems.
Government entities, such as CISA and the FTC, have reinforced the importance of patching, along with leveraging fines against businesses failing to take action. While it has been a long-haul response effort, the importance of remediating software and systems vulnerable to Log4Shell remains clear.
How to mitigate Log4J vulnerabilities #
Patches were made available to prevent code execution Log4J version 2.15.0, but these patches did not disable inline message lookup, which can expose things like environment variables and system configuration settings to an attacker that can observe the generated logs. Additional patches were made available in Log4J version 2.16.0 to make JNDI lookups disabled by default, limited to certain protocols, and only localhost allowed by default. Further patches have been made in Log4J version 2.17.0 to protect from uncontrolled recursion via self-referential lookups, along with additional patches in Log4J version 2.17.1 for limiting JNDI data source names to the java protocol.
For mitigations that folks can take immediately, Apache has offered some guidance.
Note: Initially it was thought that the problem could be mitigated by setting log4j2.formatMsgNoLookups or the environment variable LOG4J_FORMAT_MSG_NO_LOOKUPS. Apache have now clarified that those mitigation strategies are insufficient.
Mitigating these issues requires one of the following actions:
- Upgrading your Log4J version:
- This will remediate all recent known vulnerabilities.
- Log4J v2.17.1 or higher (for Java 8 users).
- Log4J v2.12.4 or higher (for Java 7 users).
- Log4J v2.3.2 or higher (for Java 6 users).
- Removing the JndiLookup class from the jars in the classpath:
- This only mitigates CVE-2021-44228 and CVE-2021-45046.
- NOTE: that this mitigation is not valid for Log4J version 2.16.0.
$ zip -q -d log4j-core-*.jar org/apache/logging/log4j/core/lookup/JndiLookup.class
- Overriding the
org.apache.logging.log4j.core.lookup.JndiLookupclass by making appropriate changes to your classloader configuration:- This only mitigates CVE-2021-44228 and CVE-2021-45046.
It is worth noting that an updated version of the Java runtime is not a sufficient mitigation. Newer versions of Java block the URL class loader by default, but can still be abused to leak secrets from the environment, and deserialization attacks may still succeed using classes already loaded by the process.
How to find applications that use Log4J with runZero #
Identifying every application, device, and service using the Log4J library is going to be an ongoing effort for security professionals. We will continue updating this post and our pre-built queries as more information becomes available.
The following query can be used to identify applications that are likely to be affected by this issue:
product:atlassian or product:avaya or product:coldfusion or product:coyote or product:cpanel or product:druid or product:"elastic search" or product:"epolicy orchestrator" or product:flink or product:graylog or product:hadoop or product:horizon or product:imc or product:jamf or product:jboss or product:jetty or (product:"kerio connect" and protocol:http) or product:logstash or product:metabase or product:minecraft or product:mongodb or product:neo4j or product:openfire or product:pega or product:recoverpoint or product:resin or product:rundeck or product:symantec or product:sonicwall or product:solarwinds or product:sophos or product:splunk or product:tableau or product:tomcat or product:="ubiquiti unifi" or product:"vmware horizon" or product:"vmware vcenter" or product:"vmware vrealize" or product:"vmware site recovery" or product:vmanage or product:wowza or hw:netapp or hw:imc or hw:"ucs manager" or hw:"crosswork son appliance" or hw:"site recovery manager" or hw:sonicwall or tcp_port:8983 or tcp_port:9092 or tcp_port:7077 or tcp_port:5347 or protocol:cassandra or protocol:elasticsearch
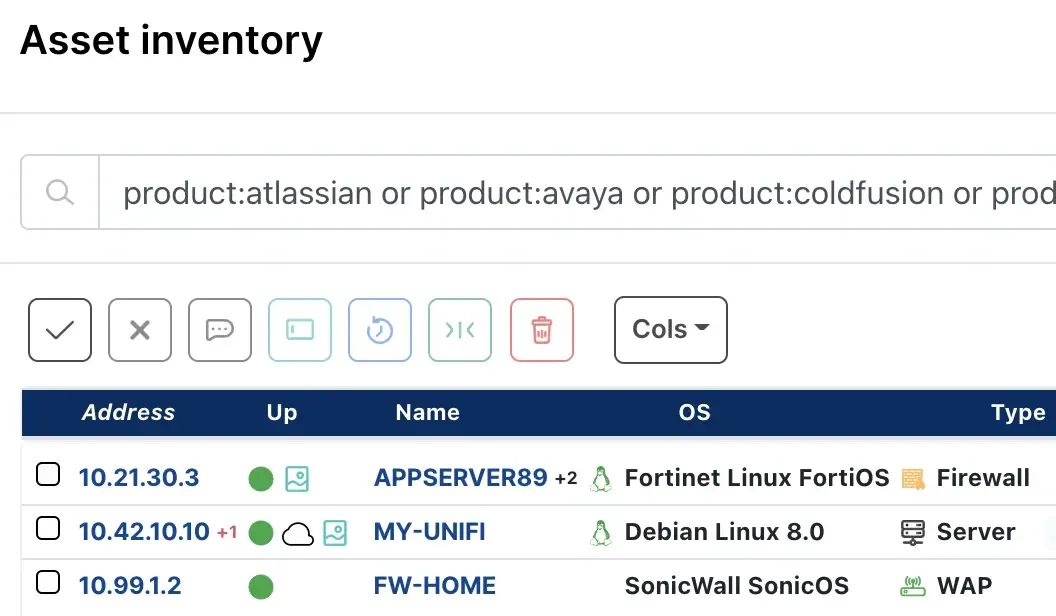
As always, any prebuilt queries we create are available from our Queries Library. Check out the library for other useful inventory queries. Self-hosted customers may copy the query above, or use the Export System Queries option to download an importable query set from the cloud console.
Scan with runZero to help with Log4J #
Get runZero free for 21 days. Build your asset inventory and identify apps using Log4J–in minutes.
Acknowledgements #
- Thanks to LunarSec for their initial and continued efforts.
- Thanks to Bishop Fox for tracking open source applications early on.
- Thanks to YfryTchsG for testing everything on the internet and sharing screenshots.
- Thanks to SwitHak for building the Blue Team Log4Shell Cheat Sheet.
- Thanks to Royce Williams for his extensive list.
Affected products and services #
ABB #
 ABB Remote Service — Versions affected: ABB Remote Platform (RAP)
ABB Remote Service — Versions affected: ABB Remote Platform (RAP)
Adobe #
Akamai #
 SIEM Splunk Connector — Versions affected: All
SIEM Splunk Connector — Versions affected: All
Amazon #
Apache #
 Cassandra — via appender.
Cassandra — via appender. Druid
Druid Dubbo
Dubbo Flink
Flink Geode
Geode Hadoop
Hadoop James
James Kafka
Kafka Karaf — Depends on PAX logging which is affected.
Karaf — Depends on PAX logging which is affected. Solr
Solr Spark
Spark Storm — via Docker.
Storm — via Docker. Struts
Struts Tapestry
Tapestry Tika
Tika Wicket
Wicket
APC #
 PowerChute Business Edition — Unknown to 10.0.2.301 affected.
PowerChute Business Edition — Unknown to 10.0.2.301 affected. PowerChute Network Shutdown — Unknown to 4.2.0 affected.
PowerChute Network Shutdown — Unknown to 4.2.0 affected.
Apereo #
Appeon #
 PowerBuilder — Versions affected: Appeon PowerBuilder 2017-2021 regardless of product edition
PowerBuilder — Versions affected: Appeon PowerBuilder 2017-2021 regardless of product edition
Aptible #
 Aptible — Versions affected: ElasticSearch 5.X
Aptible — Versions affected: ElasticSearch 5.X
Arista #
 Analytics Node for Converged Cloud Fabric — Affected: DMF (BMF) 7.0.0 and later.
Analytics Node for Converged Cloud Fabric — Affected: DMF (BMF) 7.0.0 and later.
CloudVision
 CloudVision Portal — Affected: 2019.1.0 and all later releases
CloudVision Portal — Affected: 2019.1.0 and all later releases
Cognitive Wi-Fi
 CloudVision Wi-Fi, virtual appliance or physical appliance — Affected: 8.8 and all later releases
CloudVision Wi-Fi, virtual appliance or physical appliance — Affected: 8.8 and all later releases
DANZ Monitoring Fabric
 Analytics Node for DANZ Monitoring Fabric — Affected: DMF (BMF) 7.0.0 and later.
Analytics Node for DANZ Monitoring Fabric — Affected: DMF (BMF) 7.0.0 and later. Embedded Analytics for Converged Cloud Fabric — Affected: Embedded Analytics for Converged Cloud Fabric
Embedded Analytics for Converged Cloud Fabric — Affected: Embedded Analytics for Converged Cloud Fabric
Ascertia #
 Advanced Digital Signing Server — include Log4J jar files in their packages.
Advanced Digital Signing Server — include Log4J jar files in their packages. PrimeKey EJBCA — include Log4J jar files in their packages.
PrimeKey EJBCA — include Log4J jar files in their packages. PrimeKey SignServer — include Log4J jar files in their packages.
PrimeKey SignServer — include Log4J jar files in their packages.
Atlassian #
 Atlassian Products — Self-hosted if configured with log4j.
Atlassian Products — Self-hosted if configured with log4j. Bamboo — Self-hosted if configured with log4j.
Bamboo — Self-hosted if configured with log4j. Confluence — Self-hosted if configured with log4j.
Confluence — Self-hosted if configured with log4j. Crowd — Self-hosted if configured with log4j.
Crowd — Self-hosted if configured with log4j. Cruicible — Self-hosted if configured with log4j.
Cruicible — Self-hosted if configured with log4j. Fisheye — Self-hosted if configured with log4j.
Fisheye — Self-hosted if configured with log4j. Jira — Self-hosted if configured with log4j.
Jira — Self-hosted if configured with log4j.
Avaya #
The current list can be found in the advisory. Some products are still under investigation.
 Avaya ACCS IPO on Azure — Afffected versions: 11.0.4.1 to 11.0.4.6, 11.1.0.0 to 11.1.2.0
Avaya ACCS IPO on Azure — Afffected versions: 11.0.4.1 to 11.0.4.6, 11.1.0.0 to 11.1.2.0 Avaya Analytics — Affected versions: 4.1.0.0, 4.1.0.1, 4.1.1.0
Avaya Analytics — Affected versions: 4.1.0.0, 4.1.0.1, 4.1.1.0 Avaya Aura Application Enablement Services — All versions affected.
Avaya Aura Application Enablement Services — All versions affected. Avaya Aura Call Center Elite Multichannel — Affected versions: 6.6. and its service packs
Avaya Aura Call Center Elite Multichannel — Affected versions: 6.6. and its service packs Avaya Aura Contact Center — Affected versions: 7.0.3, 7.1.X
Avaya Aura Contact Center — Affected versions: 7.0.3, 7.1.X Avaya Aura Device Services — Affected versions: s 8.0.1.X, 8.0.2.X ,8.1.3.X, 8.1.4.X, 8.1.5.X, 10.1.0.0
Avaya Aura Device Services — Affected versions: s 8.0.1.X, 8.0.2.X ,8.1.3.X, 8.1.4.X, 8.1.5.X, 10.1.0.0 Avaya Aura Media Server — Affected versions: 8.0.0, 8.0.1, 8.0.2
Avaya Aura Media Server — Affected versions: 8.0.0, 8.0.1, 8.0.2 Avaya Aura Presence Services — Afected versions: 7.X, 8.X, 10.1.0.0
Avaya Aura Presence Services — Afected versions: 7.X, 8.X, 10.1.0.0 Avaya Aura Session Manager — All versions affected.
Avaya Aura Session Manager — All versions affected. Avaya Aura System Manager — Affected versions: 8.0 - 8.1.2, 8.1.3, 10.1
Avaya Aura System Manager — Affected versions: 8.0 - 8.1.2, 8.1.3, 10.1 Avaya Aura Web Gateway — Affected versions: 3.7.0.1 - 3.11.0.0
Avaya Aura Web Gateway — Affected versions: 3.7.0.1 - 3.11.0.0 Avaya Aura Workforce Optimization (WFO) — All versions affected.
Avaya Aura Workforce Optimization (WFO) — All versions affected. Avaya Aura Workforce Optimization Advanced — Affected versions: 15.2 HFR7
Avaya Aura Workforce Optimization Advanced — Affected versions: 15.2 HFR7 Avaya Breeze — Affected versions: 3.6.X, 3.7.X, 3.8.X
Avaya Breeze — Affected versions: 3.6.X, 3.7.X, 3.8.X Avaya Co-Browsing Snap-in — Affected versions: 3.4, 3.6, 3.6.1, 3.7, 3.8, 3.8.1, 3.8.1.1
Avaya Co-Browsing Snap-in — Affected versions: 3.4, 3.6, 3.6.1, 3.7, 3.8, 3.8.1, 3.8.1.1 Avaya Contact Center Select — Affected versions: 7.0.3, 7.1.X
Avaya Contact Center Select — Affected versions: 7.0.3, 7.1.X Avaya Converged Platform 4200 — Affected versions: 4.0
Avaya Converged Platform 4200 — Affected versions: 4.0 Avaya CRM Connector - Connected Desktop — Affected versions: 2.2
Avaya CRM Connector - Connected Desktop — Affected versions: 2.2 Avaya IP Office — Affected versions: 3.0.3, 3.0.4
Avaya IP Office — Affected versions: 3.0.3, 3.0.4 Avaya IP Office Platform — Affected versions: 11.0.4.1 to 11.0.4.6, 11.1.0.0 to 11.1.2.0
Avaya IP Office Platform — Affected versions: 11.0.4.1 to 11.0.4.6, 11.1.0.0 to 11.1.2.0 Avaya Meetings Management — Affected versions 9.1.X
Avaya Meetings Management — Affected versions 9.1.X Avaya Meetings Server — All versions affected.
Avaya Meetings Server — All versions affected. Avaya Meetings Streaming and Recording — All versions affected.
Avaya Meetings Streaming and Recording — All versions affected. Avaya Oceana Solution — All versions affected.
Avaya Oceana Solution — All versions affected. Avaya Oceana Workspaces — All versions affected.
Avaya Oceana Workspaces — All versions affected. Avaya Session Border Controller for Enterprise — All versions affected.
Avaya Session Border Controller for Enterprise — All versions affected. Avaya Social Media Hub — Affected versions: 1.1
Avaya Social Media Hub — Affected versions: 1.1 Avaya Solutions Platform 4200 — Affected versions: 4.0, 4.1.X
Avaya Solutions Platform 4200 — Affected versions: 4.0, 4.1.X Avaya WebRTC Connect — Affected versions: 4.0, 4.1.X
Avaya WebRTC Connect — Affected versions: 4.0, 4.1.X Avaya Workforce Engagement — All versions affected.
Avaya Workforce Engagement — All versions affected. Avaya Workforce Engagement Select — Affected versions: 5.3, 5.3.0.1, 5.3.0.2
Avaya Workforce Engagement Select — Affected versions: 5.3, 5.3.0.1, 5.3.0.2 Avaya Workspaces — All versions affected.
Avaya Workspaces — All versions affected. Business Rules Engine — Affected versions: 3.3, 3.4, 3.5, 3.6, 3.7
Business Rules Engine — Affected versions: 3.3, 3.4, 3.5, 3.6, 3.7 Callback Assist — Affected versions: 5.0.0.X, 5.0.1.X
Callback Assist — Affected versions: 5.0.0.X, 5.0.1.X Control Manager — Affected versions: 9.0.2.X
Control Manager — Affected versions: 9.0.2.X Device Enrollment Service — Version 3.1 affected.
Device Enrollment Service — Version 3.1 affected. Equinox Conferencing — Versions affected: 9.1.2
Equinox Conferencing — Versions affected: 9.1.2 GSMB: Hospitality - Middleware FOIS — Versions affected: 6.1, 6.3
GSMB: Hospitality - Middleware FOIS — Versions affected: 6.1, 6.3 GSMB: Medial — Versions affected: 6, 6.1, 6.5
GSMB: Medial — Versions affected: 6, 6.1, 6.5 Interaction Center — All versions affected.
Interaction Center — All versions affected. IP Office Platform — Affected versions: 11.0.4.1 to 11.0.4.6, 11.1.0.0 to 11.1.2.0
IP Office Platform — Affected versions: 11.0.4.1 to 11.0.4.6, 11.1.0.0 to 11.1.2.0 Proactive Outreach Manager — Affected versions: 3.1.2.X, 3.1.3.X, 4.0.X, 4.0.1.X
Proactive Outreach Manager — Affected versions: 3.1.2.X, 3.1.3.X, 4.0.X, 4.0.1.X
BeyondTrust #
 Privilege Management (PM) Cloud — Affected, version not reported.
Privilege Management (PM) Cloud — Affected, version not reported. Privilege Management Reporting (PMR) — Affected versions: 21.2 (for BeyondInsight 21.3)
Privilege Management Reporting (PMR) — Affected versions: 21.2 (for BeyondInsight 21.3)
BMC Software #
The current list can be found in the advisory.
 Bladelogic Database Automation
Bladelogic Database Automation BMC AMI Ops Common Rest API (CRA)
BMC AMI Ops Common Rest API (CRA) BMC AMI Ops Infrastructure (MVI)
BMC AMI Ops Infrastructure (MVI) BMC AMI Ops Insight
BMC AMI Ops Insight BMC AMI Ops UI
BMC AMI Ops UI BMC Client Management
BMC Client Management BMC Discovery
BMC Discovery BMC Helix Continuous Optimization
BMC Helix Continuous Optimization BMC License Usage Collection Utility
BMC License Usage Collection Utility CMDB
CMDB Control-M
Control-M Helix Data Manager
Helix Data Manager MainView Middleware Monitor
MainView Middleware Monitor Remedy Smart Reporting
Remedy Smart Reporting Sentry Storage All-in-One ETL
Sentry Storage All-in-One ETL Sentry Storage Analyzer KM
Sentry Storage Analyzer KM Sybase KM
Sybase KM TrueSight App Visibility Manager
TrueSight App Visibility Manager TrueSight Automation Console
TrueSight Automation Console TrueSight Automation for Networks
TrueSight Automation for Networks TrueSight Automation for Servers
TrueSight Automation for Servers TrueSight Infrastructure Management
TrueSight Infrastructure Management TrueSight IT Data Analytics
TrueSight IT Data Analytics TrueSight Operations Management
TrueSight Operations Management TrueSight Smart Reporting
TrueSight Smart Reporting TSOM Smart Reporting
TSOM Smart Reporting
Brainworks #
 Kerio Connect — version <9.4 is affected by the vulnerability CVE-2021-44228.
Kerio Connect — version <9.4 is affected by the vulnerability CVE-2021-44228.
Broadcom (CA, Symantec) #
The current list can be found in the advisory.
 CA Advanced Authentication, CA Risk Authentication, CA Strong Authentication
CA Advanced Authentication, CA Risk Authentication, CA Strong Authentication CA Automic & CA Continuous Delivery
CA Automic & CA Continuous Delivery Layer7 API Developer Portal — Versions 4.4, 4.5, 5.0, 5.0 CR1, 5.0.2, and 5.0.2.1 affected.
Layer7 API Developer Portal — Versions 4.4, 4.5, 5.0, 5.0 CR1, 5.0.2, and 5.0.2.1 affected. Layer7 API Developer Portal SaaS — Version 5.0.3 affected.
Layer7 API Developer Portal SaaS — Version 5.0.3 affected. Layer7 API Gateway — Versions 9.4, 10.0, and 10.1 affected.
Layer7 API Gateway — Versions 9.4, 10.0, and 10.1 affected. Layer7 Live API Creator — Versions 5.1-5.3 (EOS) and 5.4 affected.
Layer7 Live API Creator — Versions 5.1-5.3 (EOS) and 5.4 affected. LiveUpdate Administrator (LUA) — Possibly affected.
LiveUpdate Administrator (LUA) — Possibly affected. Symantec Endpoint Detection and Response (EDR) On-premise — Versions 2.X, 3.X, and 4.X affected.
Symantec Endpoint Detection and Response (EDR) On-premise — Versions 2.X, 3.X, and 4.X affected. Symantec Endpoint Protection Manager (SEPM) — Versions 14.2 and above are affected.
Symantec Endpoint Protection Manager (SEPM) — Versions 14.2 and above are affected. Symantec Identity Governance and Administration — Versions 14.2, 14.3, and 14.4 affected.
Symantec Identity Governance and Administration — Versions 14.2, 14.3, and 14.4 affected. Symantec PAM Server Control — Versions 14.0.X and 14.1.X affected.
Symantec PAM Server Control — Versions 14.0.X and 14.1.X affected. Symantec Privileged Access Manager — Versions 3.4.X and 4.0.X affected.
Symantec Privileged Access Manager — Versions 3.4.X and 4.0.X affected. Symantec Privileged Identity Manager — Versions 12.9.X and 14.0 affected.
Symantec Privileged Identity Manager — Versions 12.9.X and 14.0 affected. Symantec SiteMinder (CA Single Sign-on) — Some 12.7.X and 12.8.X components affected.
Symantec SiteMinder (CA Single Sign-on) — Some 12.7.X and 12.8.X components affected. VIP Authentication Hub (separate from VIP SaaS) — All supported versions affected.
VIP Authentication Hub (separate from VIP SaaS) — All supported versions affected.
CaseWare #
 Cloud — Versions affected: unknown
Cloud — Versions affected: unknown
CIS-CAT #
 CIS-CAT Pro Assessor Service v4 — Versions < 1.13.0 affected.
CIS-CAT Pro Assessor Service v4 — Versions < 1.13.0 affected. CIS-CAT Pro Assessor v3 — Versions < 3.0.77 affected.
CIS-CAT Pro Assessor v3 — Versions < 3.0.77 affected. CIS-CAT Pro Assessor v4 — Versions < 4.13.0 affected.
CIS-CAT Pro Assessor v4 — Versions < 4.13.0 affected. CSAT Pro — Versions < 1.7.1 affected.
CSAT Pro — Versions < 1.7.1 affected.
CIS-CAT #
Cisco #
The current list can be found in the advisory. Many other products are still under investigation.
Cisco Cloud Hosted Services
 Cisco DNA Spaces
Cisco DNA Spaces Cisco Kinetic for Cities
Cisco Kinetic for Cities Cisco Umbrella
Cisco Umbrella Cisco Unified Communications Manager Cloud
Cisco Unified Communications Manager Cloud Cisco Webex Cloud-Connected UC (CCUC)
Cisco Webex Cloud-Connected UC (CCUC) CloudLock
CloudLock Duo
Duo Managed Services Accelerator (MSX) Network Access Control Service
Managed Services Accelerator (MSX) Network Access Control Service ThousandEyes
ThousandEyes
Collaboration and Social Media
Network and Content Security Devices
 Cisco Advanced Web Security Reporting Application
Cisco Advanced Web Security Reporting Application Cisco Identity Services Engine (ISE)
Cisco Identity Services Engine (ISE) Cisco Registered Envelope Service
Cisco Registered Envelope Service
Network Management and Provisioning
 Cisco CloudCenter Suite Admin
Cisco CloudCenter Suite Admin Cisco Crosswork Change Automation
Cisco Crosswork Change Automation Cisco Evolved Programmable Network Manager
Cisco Evolved Programmable Network Manager Cisco Integrated Management Controller (IMC) Supervisor
Cisco Integrated Management Controller (IMC) Supervisor Cisco Intersight Virtual Appliance
Cisco Intersight Virtual Appliance Cisco Network Services Orchestrator (NSO)
Cisco Network Services Orchestrator (NSO) Cisco Nexus Dashboard (formerly Cisco Application Services Engine)
Cisco Nexus Dashboard (formerly Cisco Application Services Engine) Cisco WAN Automation Engine (WAE)
Cisco WAN Automation Engine (WAE)
Routing and Switching - Enterprise and Service Provider
Unified Computing
Video, Streaming, TelePresence, and Transcoding Devices
Voice and Unified Communications Devices
 Cisco BroadCloud
Cisco BroadCloud Cisco Computer Telephony Integration Object Server (CTIOS)
Cisco Computer Telephony Integration Object Server (CTIOS) Cisco Packaged Contact Center Enterprise
Cisco Packaged Contact Center Enterprise Cisco Unified Contact Center Enterprise
Cisco Unified Contact Center Enterprise Cisco Unified Contact Center Enterprise - Live Data server
Cisco Unified Contact Center Enterprise - Live Data server Cisco Unified Intelligent Contact Management Enterprise
Cisco Unified Intelligent Contact Management Enterprise Cisco Unified SIP Proxy Software
Cisco Unified SIP Proxy Software
Other
Cloudera #
 Ambari — Versions affected: 2.X, 1.X
Ambari — Versions affected: 2.X, 1.X Arcadia Enterprise — Versions affected: 7.1.X
Arcadia Enterprise — Versions affected: 7.1.X CDH, HDP, and HDF — Versions affected: 6.X
CDH, HDP, and HDF — Versions affected: 6.X CDP Private Cloud Base — Versions affected: 7.X
CDP Private Cloud Base — Versions affected: 7.X CDS 3 Powered by Apache Spark — Versions affected: All versions
CDS 3 Powered by Apache Spark — Versions affected: All versions CDS 3.2 for GPUs — Versions affected: All versions
CDS 3.2 for GPUs — Versions affected: All versions Cloudera Cybersecurity Platform — Versions affected: All versions
Cloudera Cybersecurity Platform — Versions affected: All versions Cloudera Data Engineering (CDE) — Versions affected: All versions
Cloudera Data Engineering (CDE) — Versions affected: All versions Cloudera Data Science Workbench (CDSW) — Versions affected: 2.X, 3.X
Cloudera Data Science Workbench (CDSW) — Versions affected: 2.X, 3.X Cloudera Data Warehouse (CDW) — Versions affected: All versions
Cloudera Data Warehouse (CDW) — Versions affected: All versions Cloudera Edge Management (CEM) — Versions affected: All versions
Cloudera Edge Management (CEM) — Versions affected: All versions Cloudera Enterprise — Versions affected: 6.X
Cloudera Enterprise — Versions affected: 6.X Cloudera Flow Management (CFM) — Versions affected: All versions
Cloudera Flow Management (CFM) — Versions affected: All versions Cloudera Machine Learning (CML) — Versions affected: All versions
Cloudera Machine Learning (CML) — Versions affected: All versions Cloudera Manager (Including Backup Disaster Recovery (BDR) and Replication Manager) — Versions affected: All versions
Cloudera Manager (Including Backup Disaster Recovery (BDR) and Replication Manager) — Versions affected: All versions Cloudera Runtime (including Cloudera Data Hub and all Data Hub templates) — Versions affected: 7.0.X, 7.1.X, 7.2.X
Cloudera Runtime (including Cloudera Data Hub and all Data Hub templates) — Versions affected: 7.0.X, 7.1.X, 7.2.X Cloudera Stream Processing (CSP) — Versions affected: All versions
Cloudera Stream Processing (CSP) — Versions affected: All versions Data Steward Studio (DSS) — Versions affected: All versions
Data Steward Studio (DSS) — Versions affected: All versions Hortonworks Data Platform (HDP) — Versions affected: 7.1.X, 2.7.X, 2.6.X
Hortonworks Data Platform (HDP) — Versions affected: 7.1.X, 2.7.X, 2.6.X Management Console — Versions affected: All versions
Management Console — Versions affected: All versions Workload XM — Versions affected: All versions
Workload XM — Versions affected: All versions
Cloudogu #
 Ecosystem — Versions affected: All
Ecosystem — Versions affected: All
Commvault #
Confluent #
 Confluent ElasticSearch Sink Connector — Versions affected: < 11.1.7
Confluent ElasticSearch Sink Connector — Versions affected: < 11.1.7 Confluent Google DataProc Sink Connector — Versions affected: < 1.1.5
Confluent Google DataProc Sink Connector — Versions affected: < 1.1.5 Confluent HDFS 2 Sink Connector — Versions affected: < 10.1.3
Confluent HDFS 2 Sink Connector — Versions affected: < 10.1.3 Confluent HDFS 3 Sink Connector — Versions affected: < 1.1.8
Confluent HDFS 3 Sink Connector — Versions affected: < 1.1.8 Confluent Platform — Versions affected: < 7.0.1
Confluent Platform — Versions affected: < 7.0.1 Confluent Splunk Sink Connector — Versions affected: < 2.05
Confluent Splunk Sink Connector — Versions affected: < 2.05 Confluent VMWare Tanzu GemFire Sink Connector — Versions affected: < 1.0.8
Confluent VMWare Tanzu GemFire Sink Connector — Versions affected: < 1.0.8
Decos #
 JOIN Zaak & Document (Private Cloud) — Versions affected: All
JOIN Zaak & Document (Private Cloud) — Versions affected: All
Dell #
EMC
 EMC Avamar
EMC Avamar EMC BSN Controller Node
EMC BSN Controller Node EMC Cloud Disaster Recovery
EMC Cloud Disaster Recovery EMC Data Protection Advisor
EMC Data Protection Advisor EMC Data Protection Central — Versions 1.0.0, 1.0.1, 18.1, 18.2, 19.1, 19.2, 19.3, 19.4 affected.
EMC Data Protection Central — Versions 1.0.0, 1.0.1, 18.1, 18.2, 19.1, 19.2, 19.3, 19.4 affected. EMC Data Protection Search — Affected
EMC Data Protection Search — Affected EMC ECS
EMC ECS EMC Enterprise Storage Analytics for vRealize Operations
EMC Enterprise Storage Analytics for vRealize Operations EMC IDPA System Manager — Versions 18.1, 18.2, 19.2 affected.
EMC IDPA System Manager — Versions 18.1, 18.2, 19.2 affected. EMC Integrated System for Azure Stack HCI
EMC Integrated System for Azure Stack HCI EMC Integrated System for Microsoft Azure Stack Hub
EMC Integrated System for Microsoft Azure Stack Hub EMC Metro Node
EMC Metro Node EMC NetWorker / NetWorker VE
EMC NetWorker / NetWorker VE EMC Networking Virtual Edge Platform with VersaOS
EMC Networking Virtual Edge Platform with VersaOS EMC ObjectScale — Affected
EMC ObjectScale — Affected EMC Open Management Enterprise - Modular
EMC Open Management Enterprise - Modular EMC OpenManage Enterprise Services
EMC OpenManage Enterprise Services EMC PowerFlex Appliance — Affected,
EMC PowerFlex Appliance — Affected, EMC PowerFlex Manager — Affected
EMC PowerFlex Manager — Affected EMC PowerFlex Rack — Affected
EMC PowerFlex Rack — Affected EMC PowerFlex Software (SDS)
EMC PowerFlex Software (SDS) EMC PowerProtect Data Manager — Affected; Workaround expected 12/15
EMC PowerProtect Data Manager — Affected; Workaround expected 12/15 EMC PowerProtect DP Series Appliance (iDPA) — Affected; Workaround expected 12/15
EMC PowerProtect DP Series Appliance (iDPA) — Affected; Workaround expected 12/15 EMC PowerStore — Affected; Workaround expected 12/31
EMC PowerStore — Affected; Workaround expected 12/31 EMC RecoverPoint — Affected.
EMC RecoverPoint — Affected. EMC Ruckus SmartZone 100 Controller
EMC Ruckus SmartZone 100 Controller EMC Ruckus SmartZone 300 Controller
EMC Ruckus SmartZone 300 Controller EMC Ruckus Virtual Software
EMC Ruckus Virtual Software EMC SRM vApp
EMC SRM vApp EMC Streaming Data Platform — Affected
EMC Streaming Data Platform — Affected EMC Unity — Affected; Workaround expected 12/31
EMC Unity — Affected; Workaround expected 12/31 EMC VxRail Appliance — 4.5.x versions affected.
EMC VxRail Appliance — 4.5.x versions affected. EMC XC
EMC XC Networker — Affected; Workaround expected 12/15
Networker — Affected; Workaround expected 12/15 Networker VE — Affected
Networker VE — Affected
Other
 Apex Console
Apex Console Apex Data Storage Services
Apex Data Storage Services Cloud IQ
Cloud IQ Connectrix (Cisco MDS DCNM)
Connectrix (Cisco MDS DCNM) Connectrix B-Series SANnav
Connectrix B-Series SANnav Data Domain OS — Versions 6.1 and 6.2 to 7.3 to 7.6 affected.
Data Domain OS — Versions 6.1 and 6.2 to 7.3 to 7.6 affected. Open Management Enterprise - Modular — Affected; Workaround expected 12/17
Open Management Enterprise - Modular — Affected; Workaround expected 12/17 OpenManage Enterprise
OpenManage Enterprise Secure Connect Gateway (SCG) 5.0 Appliance — Affected
Secure Connect Gateway (SCG) 5.0 Appliance — Affected Secure Connect Gateway (SCG) Policy Manager
Secure Connect Gateway (SCG) Policy Manager SmartFabric Director
SmartFabric Director SMR — Versions prior to 4.5.0.1 affected.
SMR — Versions prior to 4.5.0.1 affected. SRM — Versions prior to 4.5.0.1 affected.
SRM — Versions prior to 4.5.0.1 affected. SRS Policy Manager
SRS Policy Manager Storage Center - Dell Storage Manager
Storage Center - Dell Storage Manager SupportAssist Enterprise — Affected
SupportAssist Enterprise — Affected Unisphere Central — Affected
Unisphere Central — Affected Vblock — Affected
Vblock — Affected VNXe 1600, 3200 — Affected
VNXe 1600, 3200 — Affected vRealize Data Protection Extension Data Management
vRealize Data Protection Extension Data Management vRealize Orchestrator (vRO) Plug-ins for Dell EMC Storage
vRealize Orchestrator (vRO) Plug-ins for Dell EMC Storage VxBlock — Affected
VxBlock — Affected VxFlex — Affected; Workaround expected 12/15
VxFlex — Affected; Workaround expected 12/15 Wyse Management Suite — Version 3.5 and earlier affected.
Wyse Management Suite — Version 3.5 and earlier affected. Wyse Windows Embedded — Affected
Wyse Windows Embedded — Affected
Dell #
Other
 Enterprise Hybrid Cloud — Affected
Enterprise Hybrid Cloud — Affected
Eaton #
 Undisclosed — Versions affected: undisclosed
Undisclosed — Versions affected: undisclosed
Elastic #
Elastic has confirmed the vulnerability, but believes their mitigations make it difficult to exploit.
EVL Labs #
 JGAAP — Versions affected: < 8.0.2
JGAAP — Versions affected: < 8.0.2
Ewon #
 eCatcher — Versions affected: < 6.7.8
eCatcher — Versions affected: < 6.7.8
ExtraHop #
 Reveal(x) — Versions affected: <=8.4.6, <=8.5.3, <=8.6.4
Reveal(x) — Versions affected: <=8.4.6, <=8.5.3, <=8.6.4
F-Secure #
 F-Secure Elements Connector
F-Secure Elements Connector F-Secure Endpoint Proxy
F-Secure Endpoint Proxy F-Secure Messaging Security Gateway
F-Secure Messaging Security Gateway F-Secure Policy Manager — Note: Only the Policy Manager Server component is affected. Standalone installations of Policy Manager Console are not affected.
F-Secure Policy Manager — Note: Only the Policy Manager Server component is affected. Standalone installations of Policy Manager Console are not affected. F-Secure Policy Manager for Linux
F-Secure Policy Manager for Linux F-Secure Policy Manager Proxy
F-Secure Policy Manager Proxy F-Secure Policy Manager Proxy for Linux
F-Secure Policy Manager Proxy for Linux
F5 #
 Traffix SDC — Versions 5.2.0 CF1 and 5.1.0 CF-30 - 5.1.0 CF-33 affected, other F5 products themselves are not vulnerable. F5 published guidance on mitigating through BIG-IP ASM/Advanced WAF and NGINX App Protect
Traffix SDC — Versions 5.2.0 CF1 and 5.1.0 CF-30 - 5.1.0 CF-33 affected, other F5 products themselves are not vulnerable. F5 published guidance on mitigating through BIG-IP ASM/Advanced WAF and NGINX App Protect
Filecloud #
 Filecloud — FileCloud uses Apache Solr which in turn uses the log4j library.
Filecloud — FileCloud uses Apache Solr which in turn uses the log4j library.
ForgeRock #
Fortinet #
 FortiAIOps
FortiAIOps FortiCASB — Fixed on 2021-12-10
FortiCASB — Fixed on 2021-12-10 FortiConverter Portal — Fixed on 2021-12-10
FortiConverter Portal — Fixed on 2021-12-10 FortiCWP — Fixed on 2021-12-10
FortiCWP — Fixed on 2021-12-10 FortiEDR Cloud — Not exploitable. Additional precautionary mitigations put in place on 2021-12-10
FortiEDR Cloud — Not exploitable. Additional precautionary mitigations put in place on 2021-12-10 FortiInsight — Not exploitable. Additional precautionary mitigations being investigated.
FortiInsight — Not exploitable. Additional precautionary mitigations being investigated. FortiIsolator — Fix scheduled for version 2.3.4
FortiIsolator — Fix scheduled for version 2.3.4 FortiMonitor — Mitigations for NCM & Elastiflow available
FortiMonitor — Mitigations for NCM & Elastiflow available FortiPortal
FortiPortal FortiSIEM — Mitigation available
FortiSIEM — Mitigation available ShieldX
ShieldX
Github #
 GitHub Enterprise Server — CVE-2021-44228 is only exposed to authenticated users. If an instance has been configured to not use private mode, this vulnerability may also be exposed to unauthenticated users.
GitHub Enterprise Server — CVE-2021-44228 is only exposed to authenticated users. If an instance has been configured to not use private mode, this vulnerability may also be exposed to unauthenticated users. GitHub.com and GitHub Enterprise Cloud — Still investigating.
GitHub.com and GitHub Enterprise Cloud — Still investigating.
Google Cloud #
See Google Cloud Log4j security advisory.
 Actifio
Actifio Dataproc, Dataproc Metastore
Dataproc, Dataproc Metastore Google Cloud Data Fusion — Customer action needed.
Google Cloud Data Fusion — Customer action needed. Google Cloud VMware Engine
Google Cloud VMware Engine Looker — Customer action needed.
Looker — Customer action needed. Migrate for Compute Engine (M4CE)
Migrate for Compute Engine (M4CE)
Gradle #
 Gradle Enterprise — Versions affected: < 2021.3.6
Gradle Enterprise — Versions affected: < 2021.3.6 Gradle Enterprise Build Cache Node — Versions affected: < 10.1
Gradle Enterprise Build Cache Node — Versions affected: < 10.1 Gradle Enterprise Test Distribution Agent — Versions affected: < 1.6.2
Gradle Enterprise Test Distribution Agent — Versions affected: < 1.6.2
GuardedBox #
 GuardedBox — Versions affected: < 3.1.2
GuardedBox — Versions affected: < 3.1.2
HCL #
See the KB entries matching CVE-2021-44228 for additional details.
HPE #
 3PAR Service Processor — Version 5.x affected.
3PAR Service Processor — Version 5.x affected. Aruba NetInsight Network Analytics — All versions affected.
Aruba NetInsight Network Analytics — All versions affected. Authentication Server Function (AUSF) — AUSF: 1.2107.0, 1.2109.0, 1.2112.0 affected.
Authentication Server Function (AUSF) — AUSF: 1.2107.0, 1.2109.0, 1.2112.0 affected. Cray EX System Monitoring Application — All versions affected.
Cray EX System Monitoring Application — All versions affected. Cray View for ClusterStor — Versions 1.3.1 affected.
Cray View for ClusterStor — Versions 1.3.1 affected. Data Access Gateway (DAG) — v2.x and older affected.
Data Access Gateway (DAG) — v2.x and older affected. Data Management Framework 7 — Version 7 affected.
Data Management Framework 7 — Version 7 affected. Device Entitlement Gateway — Version 5 affected.
Device Entitlement Gateway — Version 5 affected. Dragon — Versions 7.2 & 7.3 affected.
Dragon — Versions 7.2 & 7.3 affected. Dynamic SIM Provisioning (DSP) — DSP3.3, DSP3.1, DSP3.4 affected.
Dynamic SIM Provisioning (DSP) — DSP3.3, DSP3.1, DSP3.4 affected. Edge Infrastructure Automation — Versions 2.0x affected.
Edge Infrastructure Automation — Versions 2.0x affected. Enhanced Internet Usage Manage — Version 10.6.3 affected.
Enhanced Internet Usage Manage — Version 10.6.3 affected. Ezmeral Container Platform — Version 5.x affected.
Ezmeral Container Platform — Version 5.x affected. Ezmeral Container Platform Bluedata EPIC — Version 3.x and 4.x affected.
Ezmeral Container Platform Bluedata EPIC — Version 3.x and 4.x affected. Ezmeral Data Fabric Ezmeral Data Fabric Core / Client — v6.2.0; MCS - v6.0.1, v6.1.0, v6.1.1 & v6.2.0; Installer – v1.17.0.0 and older affected.
Ezmeral Data Fabric Ezmeral Data Fabric Core / Client — v6.2.0; MCS - v6.0.1, v6.1.0, v6.1.1 & v6.2.0; Installer – v1.17.0.0 and older affected. Ezmeral Ecosystem Pack (EEP) Elastic Search — v6.8.8 and older versions affected.
Ezmeral Ecosystem Pack (EEP) Elastic Search — v6.8.8 and older versions affected. HBase — v1.4.13 and older affected.
HBase — v1.4.13 and older affected. Hive — v2.3.x and older affected.
Hive — v2.3.x and older affected. Hyper Converged 250 System — All versions affected.
Hyper Converged 250 System — All versions affected. Hyper Converged 380 — All versions affected.
Hyper Converged 380 — All versions affected. Infosight for Storage — All versions affected.
Infosight for Storage — All versions affected. Integrated Home Subscriber Server Software Series — I-HSS 4.0.x only when using nHSS 4G/5G IWK function.
Integrated Home Subscriber Server Software Series — I-HSS 4.0.x only when using nHSS 4G/5G IWK function. Intelligent Assurance — Only Analytics on Metrics affected.
Intelligent Assurance — Only Analytics on Metrics affected. Intelligent Management Center (iMC) — HPE IMC Standard and Enterprise 7.3 (E0706) and 7.3 (E0706P06) affected.
Intelligent Management Center (iMC) — HPE IMC Standard and Enterprise 7.3 (E0706) and 7.3 (E0706P06) affected. Kafka HDFS Connector — v10.0.0 and older affected.
Kafka HDFS Connector — v10.0.0 and older affected. Media Workflow Master — All versions affected.
Media Workflow Master — All versions affected. Network Function Virtualization Director (NFV Director) — Versions 5.1.x & 6.0.x affected.
Network Function Virtualization Director (NFV Director) — Versions 5.1.x & 6.0.x affected. Real Time Management System (RTMS) — RTMS 3.0.x, RTMS 3.1.x affected.
Real Time Management System (RTMS) — RTMS 3.0.x, RTMS 3.1.x affected. Remote SIM Provisioning Manager (RSPM) — RSPM1.3.2 & RSPM1.4.1 affected.
Remote SIM Provisioning Manager (RSPM) — RSPM1.3.2 & RSPM1.4.1 affected. Revenue Intelligence Software Series — All versions affected.
Revenue Intelligence Software Series — All versions affected. SANnav Management Software — Version 2.0.0/2.1.1 affected
SANnav Management Software — Version 2.0.0/2.1.1 affected Service Director (SD) — All versions affected.
Service Director (SD) — All versions affected. Shasta Monitoring Framework — All versions affected.
Shasta Monitoring Framework — All versions affected. Silver Peak Orchestrator — All customer managed Orchestrator and legacy GMS products are affected by this vulnerability
Silver Peak Orchestrator — All customer managed Orchestrator and legacy GMS products are affected by this vulnerability SimpliVity 325 — All versions affected.
SimpliVity 325 — All versions affected. SimpliVity 380 Gen 9 & 10 — All versions affected.
SimpliVity 380 Gen 9 & 10 — All versions affected. SimpliVity OmniCube — All versions affected.
SimpliVity OmniCube — All versions affected. StoreServ Management Console (SSMC) — All versions affected.
StoreServ Management Console (SSMC) — All versions affected. Telecom Analytics Smart Profile Server (TASPS) — All versions affected.
Telecom Analytics Smart Profile Server (TASPS) — All versions affected. Telecom Management Information Platform Software Series — Only TeMIP Rest Server 8.3.2; TMB 3.4.0 affected.
Telecom Management Information Platform Software Series — Only TeMIP Rest Server 8.3.2; TMB 3.4.0 affected. Trueview Inventory Software Series — Versions 8.6x & 8.7x affected.
Trueview Inventory Software Series — Versions 8.6x & 8.7x affected. Unified Data Management (UDM) UDM — Versions 1.2107.0, 1.2109.0, 1.2109.1, 1.2112.0 affected.
Unified Data Management (UDM) UDM — Versions 1.2107.0, 1.2109.0, 1.2109.1, 1.2112.0 affected. Universal IoT (UioT) Platform — All versions affected.
Universal IoT (UioT) Platform — All versions affected. Unstructured Data Storage Function — UDSF: 1.2108.0, 1.2110.0, 1.2112.0 affected.
Unstructured Data Storage Function — UDSF: 1.2108.0, 1.2110.0, 1.2112.0 affected. User Data Repository (UDR) — UDR: 1.2106.0, 1.2110.0, 1.2112.0 affected.
User Data Repository (UDR) — UDR: 1.2106.0, 1.2110.0, 1.2112.0 affected. Virtual Headend Manager — All versions affected.
Virtual Headend Manager — All versions affected. XP Performance Advisor Software — Versions 7.5 through 8.4 affected.
XP Performance Advisor Software — Versions 7.5 through 8.4 affected.
HPE #
 SimpliVity 2600 Gen10 — All versions affected.
SimpliVity 2600 Gen10 — All versions affected.
Huawei #
 Agile Controller-Campus — Affected
Agile Controller-Campus — Affected Agile Controller-DCN — Affected
Agile Controller-DCN — Affected CloudCampus@AC-Campus — Affected
CloudCampus@AC-Campus — Affected eSight — Affected
eSight — Affected eSight Network — Affected
eSight Network — Affected iMaster NCE-Campus — Affected
iMaster NCE-Campus — Affected NCE-Fabric — Affected
NCE-Fabric — Affected NCE-WAN — Affected
NCE-WAN — Affected SD-WAN@AC-Campus — Affected
SD-WAN@AC-Campus — Affected SMS Gateway
SMS Gateway
IBM #
Analytics
 Cognos Analytics — Affected versions: 11.0.6 to 11.0.13 FP4, 11.1.X, 1.2.X
Cognos Analytics — Affected versions: 11.0.6 to 11.0.13 FP4, 11.1.X, 1.2.X Cognos Controller — Affected versions: 10.4.2
Cognos Controller — Affected versions: 10.4.2 Netezza Analytics — Affected versions: <= 3.3.9
Netezza Analytics — Affected versions: <= 3.3.9 Netezza Analytics for NPS — Affected versions: <= 11.2.21
Netezza Analytics for NPS — Affected versions: <= 11.2.21 Operations Analytics - Log Analysis — Affected versions: 1.3.5.3, 1.3.6, 1.3.6.1, 1.3.7, 1.3.7.1
Operations Analytics - Log Analysis — Affected versions: 1.3.5.3, 1.3.6, 1.3.6.1, 1.3.7, 1.3.7.1 Operations Analytics Predictive Insights — Affected versions: 1.3.6
Operations Analytics Predictive Insights — Affected versions: 1.3.6 Planning Analytics Workspace — Affected versions: 2.0.57+
Planning Analytics Workspace — Affected versions: 2.0.57+ QRadar User Behavior Analytics — All versions affected.
QRadar User Behavior Analytics — All versions affected. SPSS Analytic Server — Affected versions: 3.2.2.0, 3.3.0.0
SPSS Analytic Server — Affected versions: 3.2.2.0, 3.3.0.0 SPSS Statistics — Affected versions: 25.0, 26.0, 27.0.1, 28.0.1
SPSS Statistics — Affected versions: 25.0, 26.0, 27.0.1, 28.0.1
Data Management
 Db2 / Db2 Warehouse — Version 11.5, if DVM JDBC wrapper driver, NoSQL wrapper driver or blockchain wrapper driver enabled
Db2 / Db2 Warehouse — Version 11.5, if DVM JDBC wrapper driver, NoSQL wrapper driver or blockchain wrapper driver enabled Db2 on Openshift / Db2 on Cloud Pak for Data — Upgrade to 11.5.7.0+ (Openshift), upgrade to 4.0.4+ (Cloud Pak for Data)
Db2 on Openshift / Db2 on Cloud Pak for Data — Upgrade to 11.5.7.0+ (Openshift), upgrade to 4.0.4+ (Cloud Pak for Data) Decision Optimization for Cloud Pak for Data — Affected versions: 4.0.X
Decision Optimization for Cloud Pak for Data — Affected versions: 4.0.X InfoSphere Data Replication — Affected versions: 11.4, 11.4.0
InfoSphere Data Replication — Affected versions: 11.4, 11.4.0 InfoSphere Global Name Management — Affected versions: 6.0
InfoSphere Global Name Management — Affected versions: 6.0 InfoSphere Information Server — Affected versions: 11.7 (also 11.5 and 11.3, which are EOL)
InfoSphere Information Server — Affected versions: 11.7 (also 11.5 and 11.3, which are EOL) Watson Assistant for Cloud Pak for Data — Affected versions: 1.5.0, 4.0.0, 4.0.2
Watson Assistant for Cloud Pak for Data — Affected versions: 1.5.0, 4.0.0, 4.0.2
Spectrum
 Spectrum Conductor — Affected versions: 2.4.1, 2.5.0, 2.5.1
Spectrum Conductor — Affected versions: 2.4.1, 2.5.0, 2.5.1 Spectrum Control — Affected versions: 5.4.0 - 5.4.5
Spectrum Control — Affected versions: 5.4.0 - 5.4.5 Spectrum Protect Backup Archive Client — Affected versions: 7.1.8.10-7.1.8.12 (VMware only), 8.1.11.0-8.1.13.0
Spectrum Protect Backup Archive Client — Affected versions: 7.1.8.10-7.1.8.12 (VMware only), 8.1.11.0-8.1.13.0 Spectrum Protect Client Web User Interface / Spectrum Protect for Virtual Environments — Affected versions: 7.1.8.10-7.1.8.12 (VMware only), 8.1.11.0-8.1.13.0 (the Data Movers in 8.1.11 and above are affected)
Spectrum Protect Client Web User Interface / Spectrum Protect for Virtual Environments — Affected versions: 7.1.8.10-7.1.8.12 (VMware only), 8.1.11.0-8.1.13.0 (the Data Movers in 8.1.11 and above are affected) Spectrum Protect Copy Data Management — Affected versions: 2.2.14.0
Spectrum Protect Copy Data Management — Affected versions: 2.2.14.0 Spectrum Protect for Space Management — Affected versions: 7.1.8.10-7.1.8.11, 8.1.11.0-8.1.13.0
Spectrum Protect for Space Management — Affected versions: 7.1.8.10-7.1.8.11, 8.1.11.0-8.1.13.0 Spectrum Protect Operations Center — Affected versions: 7.1.0.000-7.1.14.000, 8.1.0.000-8.1.13.000
Spectrum Protect Operations Center — Affected versions: 7.1.0.000-7.1.14.000, 8.1.0.000-8.1.13.000 Spectrum Protect Plus — Affected versions: 10.1.0.0 - 10.1.9.0
Spectrum Protect Plus — Affected versions: 10.1.0.0 - 10.1.9.0 Spectrum Protect Plus Container Backup and Restore for Kubernetes and OpenShift — Affected versions: 10.1.9.0
Spectrum Protect Plus Container Backup and Restore for Kubernetes and OpenShift — Affected versions: 10.1.9.0 Spectrum Protect Snapshot for VMware — Affected versions: 4.1.6.10 - 4.1.6.12
Spectrum Protect Snapshot for VMware — Affected versions: 4.1.6.10 - 4.1.6.12 Spectrum Protect Snapshot on Windows — Affected versions: 4.1.6.10 - 4.1.6.X, 8.1.11.0 - 8.1.13.0
Spectrum Protect Snapshot on Windows — Affected versions: 4.1.6.10 - 4.1.6.X, 8.1.11.0 - 8.1.13.0 Spectrum Scale — Affected versions: 5.3.6.0 - 5.3.7.3, 6.0.1.0 - 6.1.2.0
Spectrum Scale — Affected versions: 5.3.6.0 - 5.3.7.3, 6.0.1.0 - 6.1.2.0 Spectrum Symphony — Affected versions: 7.2.0.2, 7.2.1, 7.2.1.1, 7.3, 7.3.1, 7.3.2
Spectrum Symphony — Affected versions: 7.2.0.2, 7.2.1, 7.2.1.1, 7.3, 7.3.1, 7.3.2
Sterling
 Sterling B2B Integrator — Affected versions: 6.0.0.0 - 6.1.1.0
Sterling B2B Integrator — Affected versions: 6.0.0.0 - 6.1.1.0 Sterling Configure, Price, Quote — Affected versions: 10.X
Sterling Configure, Price, Quote — Affected versions: 10.X Sterling Connect:Direct File Agent — Affected versions: 1.4
Sterling Connect:Direct File Agent — Affected versions: 1.4 Sterling Connect:Direct for Unix — Affected versions: 4.3.0, 6.0.0, 6.1.0, 6.2.0
Sterling Connect:Direct for Unix — Affected versions: 4.3.0, 6.0.0, 6.1.0, 6.2.0 Sterling Connect:Direct Web Services — Affected versions: 1.0 (Sterling Connect Direct Web Services), 6.0 (IBM Connect:Direct Web Services)
Sterling Connect:Direct Web Services — Affected versions: 1.0 (Sterling Connect Direct Web Services), 6.0 (IBM Connect:Direct Web Services) Sterling File Gateway — Affected versions: 6.0.0.0 - 6.1.1.0
Sterling File Gateway — Affected versions: 6.0.0.0 - 6.1.1.0 Sterling Global Mailbox — Affected versions: 6.0.3-6.1.1.0
Sterling Global Mailbox — Affected versions: 6.0.3-6.1.1.0 Sterling Partner Engagement Manager — Affected versions: 6.1 to 6.1.2.3, 6.2 to 6.2.0.1
Sterling Partner Engagement Manager — Affected versions: 6.1 to 6.1.2.3, 6.2 to 6.2.0.1
WebSphere
 WebSphere Application Server — Affected versions: 7.0, 8.0, 8.5, 9.0
WebSphere Application Server — Affected versions: 7.0, 8.0, 8.5, 9.0 WebSphere Application Server Liberty z/OS — Affected versions: continuous delivery
WebSphere Application Server Liberty z/OS — Affected versions: continuous delivery WebSphere Automation for IBM Cloud Pak for Watson AIOps — All versions affected.
WebSphere Automation for IBM Cloud Pak for Watson AIOps — All versions affected. WebSphere Hybrid Edition — Affected versions: 8.5, 9.0
WebSphere Hybrid Edition — Affected versions: 8.5, 9.0 WebSphere Remote Server — Affected versions: 8.5, 9.0
WebSphere Remote Server — Affected versions: 8.5, 9.0
Other
 Analyst’s Notebook Premium — Affected versions: 9.2.2, 9.3.0, 9.3.1
Analyst’s Notebook Premium — Affected versions: 9.2.2, 9.3.0, 9.3.1 App Connect Enterprise — Affected versions: 11.0.0.7 to 11.0.0.15, 12.0.1.0 to 12.0.3.0
App Connect Enterprise — Affected versions: 11.0.0.7 to 11.0.0.15, 12.0.1.0 to 12.0.3.0 App Connect for Manufacturing — Affected versions: 2.0.0.5 to 2.0.0.7
App Connect for Manufacturing — Affected versions: 2.0.0.5 to 2.0.0.7 App Connect operands — Affected versions: App Connect Enterprise Certified Container (with Operator) versions 1.1-eus, 1.4, 1.5, 2.0, 2.1, 3.0
App Connect operands — Affected versions: App Connect Enterprise Certified Container (with Operator) versions 1.1-eus, 1.4, 1.5, 2.0, 2.1, 3.0 App Connect Professional — Affected versions: 7.5.3.0, 7.5.4.0, 7.5.5.0
App Connect Professional — Affected versions: 7.5.3.0, 7.5.4.0, 7.5.5.0 Application Navigator — Affected versions: 2.5.0
Application Navigator — Affected versions: 2.5.0 Business Automation Workflow — Installs WebSphere with Log4j, affected versions: 18.0.0.0.2, 19.0, 20.0, 21.0
Business Automation Workflow — Installs WebSphere with Log4j, affected versions: 18.0.0.0.2, 19.0, 20.0, 21.0 Cloud Application Business Insights — Affected versions: 1.1.5, 1.1.6, 1.1.7
Cloud Application Business Insights — Affected versions: 1.1.5, 1.1.6, 1.1.7 Cloud Object Storage File Access — Affected versions: 7.0.0
Cloud Object Storage File Access — Affected versions: 7.0.0 Cloud Object Storage Systems ClevOS — Affected versions: 3.16.0.0 - 3.16.0.47 (LTS), 3.16.1.0 - 3.16.1.39 (Active Release)
Cloud Object Storage Systems ClevOS — Affected versions: 3.16.0.0 - 3.16.0.47 (LTS), 3.16.1.0 - 3.16.1.39 (Active Release) Cloud Pak for Automation — Affected versions: 19.X, 20.X, 21.0.1, some versions of 21.0.2, some versions of 21.0.3
Cloud Pak for Automation — Affected versions: 19.X, 20.X, 21.0.1, some versions of 21.0.2, some versions of 21.0.3 Cloud Pak for Data — Affected versions: 2.0.0.0 - 2.0.1.1
Cloud Pak for Data — Affected versions: 2.0.0.0 - 2.0.1.1 Cloud Pak for Integration — Affected versions: 2021.2.1, 2021.4.1
Cloud Pak for Integration — Affected versions: 2021.2.1, 2021.4.1 Cloud Pak for Security — Affected versions: 1.7.2.0, 1.8.0.0, 1.8.1.0, 1.9.0.0
Cloud Pak for Security — Affected versions: 1.7.2.0, 1.8.0.0, 1.8.1.0, 1.9.0.0 Cloud Private — Affected versions: 3.1.1, 3.1.2, 3.2.0, 3.2.1 CD, 3.2.2 CD
Cloud Private — Affected versions: 3.1.1, 3.1.2, 3.2.0, 3.2.1 CD, 3.2.2 CD Cloud Transformation Advisor — Affected versions: 2.5.0
Cloud Transformation Advisor — Affected versions: 2.5.0 Collaboration and Deployment Services — Affected versions: 8.3
Collaboration and Deployment Services — Affected versions: 8.3 Common Licensing License Key Server (LKS) Administration and Reporting Tool (ART) — Affected versions: 9.0
Common Licensing License Key Server (LKS) Administration and Reporting Tool (ART) — Affected versions: 9.0 Content Collector for Email — Affected versions: 4.0.X
Content Collector for Email — Affected versions: 4.0.X Content Collector for File Systems — Affected versions: 4.0.X
Content Collector for File Systems — Affected versions: 4.0.X Content Collector for IBM Connections — Affected versions: 4.0.X
Content Collector for IBM Connections — Affected versions: 4.0.X Content Collector for Sharepoint — Affected versions: 4.0.X
Content Collector for Sharepoint — Affected versions: 4.0.X Content Navigator — Affected versions: 3.0 Continuous Delivery
Content Navigator — Affected versions: 3.0 Continuous Delivery Cúram Social Program Management — Affected versions: 8.0.0.0 - 8.0.1.0
Cúram Social Program Management — Affected versions: 8.0.0.0 - 8.0.1.0 Data Risk Manager — Affected versions: 2.0.6
Data Risk Manager — Affected versions: 2.0.6 Disconnected Log Collector — Affected versions: 1.0 - 1.7
Disconnected Log Collector — Affected versions: 1.0 - 1.7 DS8000 Hardware Management Console — Affected versions: 88.5x.x.x (R8.5), 89.1x.0.0 (R9.1), 89.2x.0.0(R9.2)
DS8000 Hardware Management Console — Affected versions: 88.5x.x.x (R8.5), 89.1x.0.0 (R9.1), 89.2x.0.0(R9.2) Elastic Storage System — Affected versions: 6.0.1.0 - V6.0.2.3, 6.1.0.0 - V6.1.2.0
Elastic Storage System — Affected versions: 6.0.1.0 - V6.0.2.3, 6.1.0.0 - V6.1.2.0 Engineering Lifecycle Management products
Engineering Lifecycle Management products Engineering Requirements Management DOORS — Affected versions: 9.6.1.7 - 9.7.2.2
Engineering Requirements Management DOORS — Affected versions: 9.6.1.7 - 9.7.2.2 Engineering Systems Design Rhapsody — Affected versions: 8.4, 9.0, 9.0.1
Engineering Systems Design Rhapsody — Affected versions: 8.4, 9.0, 9.0.1 Event Streams — Affected versions: 10.0.0, 10.1.0, 10.2.0, 10.3.0, 10.3.1, 10.4.0, 2019.4.1, 2019.4.2, 2019.4.3, 2019.4.4
Event Streams — Affected versions: 10.0.0, 10.1.0, 10.2.0, 10.3.0, 10.3.1, 10.4.0, 2019.4.1, 2019.4.2, 2019.4.3, 2019.4.4 Financial Transaction Manager for Corporate Payment Services — Affected versions: 3.2.4.0 ifix 2, 3.2.4.0 ifix 6, 3.2.4.0 ifix 9
Financial Transaction Manager for Corporate Payment Services — Affected versions: 3.2.4.0 ifix 2, 3.2.4.0 ifix 6, 3.2.4.0 ifix 9 Financial Transaction Manager for Digital Payments — Affected versions: 3.2.3.0 ifix 2, 3.2.4.0 ifix 6, 3.2.5.0 ifix 3, 3.2.6.1 ifix 4, 3.2.7.0 ifix 1
Financial Transaction Manager for Digital Payments — Affected versions: 3.2.3.0 ifix 2, 3.2.4.0 ifix 6, 3.2.5.0 ifix 3, 3.2.6.1 ifix 4, 3.2.7.0 ifix 1 i2 Analyze — Affected versions: 4.3.1.0, 4.3.1.1, 4.3.2.0, 4.3.3.0, 4.3.4.0, 4.3.5.0
i2 Analyze — Affected versions: 4.3.1.0, 4.3.1.1, 4.3.2.0, 4.3.3.0, 4.3.4.0, 4.3.5.0 i2 Connect — Affected versions: 1.0.1.0, 1.0.1.1, 1.0.2, 1.0.3, 1.1.0, 1.1.1
i2 Connect — Affected versions: 1.0.1.0, 1.0.1.1, 1.0.2, 1.0.3, 1.1.0, 1.1.1 Jazz for Service Management — Affected versions: 1.1.3
Jazz for Service Management — Affected versions: 1.1.3 Kenexa LCMS Premier On Premise — Affected versions: <= 14.0
Kenexa LCMS Premier On Premise — Affected versions: <= 14.0 Kenexa LMS On Premise — Affected versions: <= 6.1
Kenexa LMS On Premise — Affected versions: <= 6.1 License Metric Tool — Affected versions: 9.2.21.0 - 9.2.25.0
License Metric Tool — Affected versions: 9.2.21.0 - 9.2.25.0 MaaS360 Enterprise Gateway — Affected versions: <= 2.105.200
MaaS360 Enterprise Gateway — Affected versions: <= 2.105.200 MQ Blockchain Bridge — Affected versions: 9.1 CD, 9.2 CD, 9.2 LTS
MQ Blockchain Bridge — Affected versions: 9.1 CD, 9.2 CD, 9.2 LTS Novalink — Affected versions: 1.0.0.16, 2.0, 2.0.1, 2.0.2, 2.0.2.1
Novalink — Affected versions: 1.0.0.16, 2.0, 2.0.1, 2.0.2, 2.0.2.1 OpenPages with Watson — Affected versions: 8.2.0.4
OpenPages with Watson — Affected versions: 8.2.0.4 Performance Management — Affected versions: 8.1.4
Performance Management — Affected versions: 8.1.4 Power Hardware Management Console — Affected versions: 9.2.950.0+, 10.1.1010.0+
Power Hardware Management Console — Affected versions: 9.2.950.0+, 10.1.1010.0+ Security Access Manager / Security Verify Access — Affected versions: 9.0.7.1 (SAM), 10.0.0.0 (SVA)
Security Access Manager / Security Verify Access — Affected versions: 9.0.7.1 (SAM), 10.0.0.0 (SVA) Security Guardium — Affected versions: 10.5, 10.6, 11.0, 11.1, 11.2, 11.3, 11.4
Security Guardium — Affected versions: 10.5, 10.6, 11.0, 11.1, 11.2, 11.3, 11.4 Spectrum Archive Enterprise Edition — Affected versions: 1.3.0.0 - 1.3.2.1
Spectrum Archive Enterprise Edition — Affected versions: 1.3.0.0 - 1.3.2.1 Tivoli Monitoring — Affected versions: 6.3.0 fix pack 7 service pack 5+
Tivoli Monitoring — Affected versions: 6.3.0 fix pack 7 service pack 5+ Tivoli Netcool Impact — Affected versions: 7.1.0.18 - 7.1.0.24
Tivoli Netcool Impact — Affected versions: 7.1.0.18 - 7.1.0.24 Transformation Extender — Affected versions: 10.0.3.0, 10.1.0.0, 10.1.0.1, 10.1.1.0
Transformation Extender — Affected versions: 10.0.3.0, 10.1.0.0, 10.1.0.1, 10.1.1.0 Watson Explorer - Analytical Components — Affected versions: 11.0.0.0 - 11.0.0.3, 11.0.1, 11.0.2.0 - 11.0.2.11
Watson Explorer - Analytical Components — Affected versions: 11.0.0.0 - 11.0.0.3, 11.0.1, 11.0.2.0 - 11.0.2.11 Watson Explorer - Foundational Components — Affected versions: 11.0.0.0 - 11.0.0.3, 11.0.1, 11.0.2.0 - 11.0.2.11
Watson Explorer - Foundational Components — Affected versions: 11.0.0.0 - 11.0.0.3, 11.0.1, 11.0.2.0 - 11.0.2.11 Watson Explorer DAE - Analytical Components — Affected versions: 12.0.0.0, 12.0.1, 12.0.2.0 - 12.0.2.2, 12.0.3.0 - 12.0.3.7
Watson Explorer DAE - Analytical Components — Affected versions: 12.0.0.0, 12.0.1, 12.0.2.0 - 12.0.2.2, 12.0.3.0 - 12.0.3.7 Watson Explorer DAE - Foundational Components — Affected versions: 12.0.0.0, 12.0.1, 12.0.2.0 - 12.0.2.2, 12.0.3.0 - 12.0.3.7
Watson Explorer DAE - Foundational Components — Affected versions: 12.0.0.0, 12.0.1, 12.0.2.0 - 12.0.2.2, 12.0.3.0 - 12.0.3.7 Watson Explorer DAE - oneWEX — Affected versions: 12.0.0.0, 12.0.1, 12.0.2.0 - 12.0.2.2, 12.0.3.0 - 12.0.3.7
Watson Explorer DAE - oneWEX — Affected versions: 12.0.0.0, 12.0.1, 12.0.2.0 - 12.0.2.2, 12.0.3.0 - 12.0.3.7 Watson Knowledge Catalog InstaScan — Affected versions: <= 1.1.6
Watson Knowledge Catalog InstaScan — Affected versions: <= 1.1.6
Informatica #
Informatica state that their cloud remediation is complete, and have an advisory listing vulnerable on-premises products.
 ActiveVOS — Affected versions: 9.2.4.3, 9.2.4.4, 9.2.4.5, 9.2.4.6
ActiveVOS — Affected versions: 9.2.4.3, 9.2.4.4, 9.2.4.5, 9.2.4.6 Axon Data Governance — Affected versions: 6.0, 6.1, 6.2, 6.3, 7.0, 7.1, 7.2, 7.2.1, 7.2.2
Axon Data Governance — Affected versions: 6.0, 6.1, 6.2, 6.3, 7.0, 7.1, 7.2, 7.2.1, 7.2.2 Customer 360 — Affected versions: > 10.2, <= 10.4 Hotfix 3
Customer 360 — Affected versions: > 10.2, <= 10.4 Hotfix 3 Customer 360 Insights — All versions affected.
Customer 360 Insights — All versions affected. Data Engineering Integration — Affected versions: 10.2, 10.2 HF2, 10.4.1, 10.4.1.3, 10.5.1
Data Engineering Integration — Affected versions: 10.2, 10.2 HF2, 10.4.1, 10.4.1.3, 10.5.1 Data Engineering Quality — Affected versions: 10.4.1, 10.4.1.3, 10.5.1
Data Engineering Quality — Affected versions: 10.4.1, 10.4.1.3, 10.5.1 Data Engineering Streaming — Affected versions: 10.4.1, 10.4.1.3, 10.5.1
Data Engineering Streaming — Affected versions: 10.4.1, 10.4.1.3, 10.5.1 Data Privacy Management — Affected versions: 10.5, 10.5.1
Data Privacy Management — Affected versions: 10.5, 10.5.1 Data Replication — Affected versions: 9.8.0
Data Replication — Affected versions: 9.8.0 Enterprise Data Catalog — Affected versions: 10.5 - 10.5.1.0.3, still investigating 10.4.X
Enterprise Data Catalog — Affected versions: 10.5 - 10.5.1.0.3, still investigating 10.4.X Enterprise Data Preparation — Affected versions: 10.5, 10.5.1
Enterprise Data Preparation — Affected versions: 10.5, 10.5.1 Fast Clone — Affected versions: 11.0
Fast Clone — Affected versions: 11.0 Informatica Data Quality — Affected versions: 10.2.2 - 10.5.1
Informatica Data Quality — Affected versions: 10.2.2 - 10.5.1 Metadata Manager — Affected versions: 10.4.1, 10.5, 10.5.1
Metadata Manager — Affected versions: 10.4.1, 10.5, 10.5.1 Multidomain MDM — Affected versions: > 10.2 and <= 10.4 HotFix 3
Multidomain MDM — Affected versions: > 10.2 and <= 10.4 HotFix 3 PowerCenter — Affected versions: 10.5, 10.5.1
PowerCenter — Affected versions: 10.5, 10.5.1 PowerExchange CDC Publisher — Affected versions: 1.2.0, 1.3.0
PowerExchange CDC Publisher — Affected versions: 1.2.0, 1.3.0 PowerExchange for CDC and Mainframe — Affected versions: 10.4, 10.4.1, 10.5, 10.5.1
PowerExchange for CDC and Mainframe — Affected versions: 10.4, 10.4.1, 10.5, 10.5.1 Product 360 — Affected versions: 8.1.1 HotFix 6, 10.0 HotFix 1 - 4, 10.1, 10.1 HotFix 1 - 3
Product 360 — Affected versions: 8.1.1 HotFix 6, 10.0 HotFix 1 - 4, 10.1, 10.1 HotFix 1 - 3 Supplier 360 — Affected versions: 10.2, 10.4, 10.4 HF1, 10.2 HF5, 10.4 HF2, 10.4 HF3
Supplier 360 — Affected versions: 10.2, 10.4, 10.4 HF1, 10.2 HF5, 10.4 HF2, 10.4 HF3 Ultra Messaging — Affected versions: 6.14
Ultra Messaging — Affected versions: 6.14
Intel #
 Audio Development Kit — Affected
Audio Development Kit — Affected Datacenter Manager — Affected
Datacenter Manager — Affected oneAPI sample browser plugin for Eclipse — Affected
oneAPI sample browser plugin for Eclipse — Affected Secure Device Onboard — Affected
Secure Device Onboard — Affected System Debugger — Affected
System Debugger — Affected
Intland #
 codebeamer — Versions affected: <= 20.11-SP11, <= 21.09-SP3
codebeamer — Versions affected: <= 20.11-SP11, <= 21.09-SP3
Ivanti #
 Avalache — Versions affected: 6.3.0, 6.3.1, 6.3.2, 6.3.3
Avalache — Versions affected: 6.3.0, 6.3.1, 6.3.2, 6.3.3
Juniper #
Cloud Services
 Security Director, but not Security Director Insights — Vulnerable/affected: 21 version 21.1 and later versions; 22 version 22.2 and later versions.
Security Director, but not Security Director Insights — Vulnerable/affected: 21 version 21.1 and later versions; 22 version 22.2 and later versions.
Paragon Automation
 Juniper Networks Paragon Insights — Vulnerable/affected: 21 version 21.1 and later versions; 22 version 22.2 and later versions.
Juniper Networks Paragon Insights — Vulnerable/affected: 21 version 21.1 and later versions; 22 version 22.2 and later versions. Juniper Networks Paragon Pathfinder — Vulnerable/affected: 21 version 21.1 and later versions; 22 version 22.2 and later versions.
Juniper Networks Paragon Pathfinder — Vulnerable/affected: 21 version 21.1 and later versions; 22 version 22.2 and later versions. Juniper Networks Paragon Planner — Vulnerable/affected: 21 version 21.1 and later versions; 22 version 22.2 and later versions.
Juniper Networks Paragon Planner — Vulnerable/affected: 21 version 21.1 and later versions; 22 version 22.2 and later versions.
Security
 Secure Analytics — May be affected.
Secure Analytics — May be affected.
Other
 JSA Series — May be affected.
JSA Series — May be affected. Junos Space Management Applications — May be affected.
Junos Space Management Applications — May be affected. Junos Space Network Management Platform — May be affected.
Junos Space Network Management Platform — May be affected. Network Director — May be affected.
Network Director — May be affected.
Kronos #
 Kronos Private Cloud — Affected, Kronos Private Cloud solutions are currently unavailable.
Kronos Private Cloud — Affected, Kronos Private Cloud solutions are currently unavailable.
Lenovo #
Networking Switches
 B300 FC SAN Switch — Brocade BNA and SANnav affected.
B300 FC SAN Switch — Brocade BNA and SANnav affected. B6505 FC SAN Switch — Brocade BNA and SANnav affected.
B6505 FC SAN Switch — Brocade BNA and SANnav affected. B6510 FC SAN Switch — Brocade BNA and SANnav affected.
B6510 FC SAN Switch — Brocade BNA and SANnav affected. ThinkSystem DB400D FC Switch — Brocade BNA and SANnav affected.
ThinkSystem DB400D FC Switch — Brocade BNA and SANnav affected. ThinkSystem DB610S FC Switch — Brocade BNA and SANnav affected.
ThinkSystem DB610S FC Switch — Brocade BNA and SANnav affected. ThinkSystem DB620S FC Switch — Brocade BNA and SANnav affected.
ThinkSystem DB620S FC Switch — Brocade BNA and SANnav affected. ThinkSystem DB630S FC Switch — Brocade BNA and SANnav affected.
ThinkSystem DB630S FC Switch — Brocade BNA and SANnav affected. ThinkSystem DB720S FC Switch — Brocade BNA and SANnav affected.
ThinkSystem DB720S FC Switch — Brocade BNA and SANnav affected. ThinkSystem DB800D FC Switch — Brocade BNA and SANnav affected.
ThinkSystem DB800D FC Switch — Brocade BNA and SANnav affected.
Software
 DSS-G — Affected
DSS-G — Affected XClarity Administrator — Affected
XClarity Administrator — Affected XClarity Administrator Virtual Appliance Full Image (For KVM) — Affected
XClarity Administrator Virtual Appliance Full Image (For KVM) — Affected XClarity Administrator Virtual Appliance Full Image (For VMWare) — Affected
XClarity Administrator Virtual Appliance Full Image (For VMWare) — Affected XClarity Administrator Virtual Appliance Full Image (For Windows) — Affected
XClarity Administrator Virtual Appliance Full Image (For Windows) — Affected
Software
 XClarity Energy Manager — Affected
XClarity Energy Manager — Affected XClarity Integrator (LXCI) for VMware vCenter — Affected
XClarity Integrator (LXCI) for VMware vCenter — Affected
Storage
 ONTAP Tools for VMware vSphere (OTV) for DM Series — DM120S, DM240N, DM240S, DM3000H, DM5000F, DM5000H, DM5100F, DM600S, DM7000F, DM7000H, DM7100F, DM7100H ThinkSystem affected.
ONTAP Tools for VMware vSphere (OTV) for DM Series — DM120S, DM240N, DM240S, DM3000H, DM5000F, DM5000H, DM5100F, DM600S, DM7000F, DM7000H, DM7100F, DM7100H ThinkSystem affected. SnapCenter Plug-in for VMware DM Series — DM120S, DM240N, DM240S, DM3000H, DM5000F, DM5000H, DM5100F, DM600S, DM7000F, DM7000H, DM7100F, DM7100H ThinkSystem affected.
SnapCenter Plug-in for VMware DM Series — DM120S, DM240N, DM240S, DM3000H, DM5000F, DM5000H, DM5100F, DM600S, DM7000F, DM7000H, DM7100F, DM7100H ThinkSystem affected. ThinkSystem Intelligent Monitoring Unified Manager for Linux for DM Series — DM120S, DM240N, DM240S, DM3000H, DM5000F, DM5000H, DM5100F, DM600S, DM7000F, DM7000H, DM7100F, DM7100H ThinkSystem affected.
ThinkSystem Intelligent Monitoring Unified Manager for Linux for DM Series — DM120S, DM240N, DM240S, DM3000H, DM5000F, DM5000H, DM5100F, DM600S, DM7000F, DM7000H, DM7100F, DM7100H ThinkSystem affected. ThinkSystem Intelligent Monitoring Unified Manager for VMware for DM Series — DM120S, DM240N, DM240S, DM3000H, DM5000F, DM5000H, DM5100F, DM600S, DM7000F, DM7000H, DM7100F, DM7100H ThinkSystem affected.
ThinkSystem Intelligent Monitoring Unified Manager for VMware for DM Series — DM120S, DM240N, DM240S, DM3000H, DM5000F, DM5000H, DM5100F, DM600S, DM7000F, DM7000H, DM7100F, DM7100H ThinkSystem affected. ThinkSystem Intelligent Monitoring Unified Manager for Windows for DM Series — DM120S, DM240N, DM240S, DM3000H, DM5000F, DM5000H, DM5100F, DM600S, DM7000F, DM7000H, DM7100F, DM7100H ThinkSystem affected.
ThinkSystem Intelligent Monitoring Unified Manager for Windows for DM Series — DM120S, DM240N, DM240S, DM3000H, DM5000F, DM5000H, DM5100F, DM600S, DM7000F, DM7000H, DM7100F, DM7100H ThinkSystem affected.
ThinkAgile
 CP-CB-10 (Lenovo) — ThinkAgile CP-Management Web Console affected.
CP-CB-10 (Lenovo) — ThinkAgile CP-Management Web Console affected. CP-CB-10E (Lenovo) — ThinkAgile CP-Management Web Console affected.
CP-CB-10E (Lenovo) — ThinkAgile CP-Management Web Console affected. CP-CN-10 (ThinkAgile) — ThinkAgile CP-Management Web Console affected.
CP-CN-10 (ThinkAgile) — ThinkAgile CP-Management Web Console affected. CP-CN-10E (ThinkAgile) — ThinkAgile CP-Management Web Console affected.
CP-CN-10E (ThinkAgile) — ThinkAgile CP-Management Web Console affected. CP-I-10 (ThinkAgile) — ThinkAgile CP-Management Web Console affected.
CP-I-10 (ThinkAgile) — ThinkAgile CP-Management Web Console affected. CP-SB-D20 (ThinkAgile) — ThinkAgile CP-Management Web Console affected.
CP-SB-D20 (ThinkAgile) — ThinkAgile CP-Management Web Console affected. CP-SB-D20E (ThinkAgile) — ThinkAgile CP-Management Web Console affected.
CP-SB-D20E (ThinkAgile) — ThinkAgile CP-Management Web Console affected. CP-SB-S10 (ThinkAgile) — ThinkAgile CP-Management Web Console affected.
CP-SB-S10 (ThinkAgile) — ThinkAgile CP-Management Web Console affected. CP6000 (ThinkAgile) — ThinkAgile CP-Management Web Console affected.
CP6000 (ThinkAgile) — ThinkAgile CP-Management Web Console affected. ThinkAgile HX — VMware Components affected.
ThinkAgile HX — VMware Components affected. ThinkAgile VX — VMware Components affected.
ThinkAgile VX — VMware Components affected.
ThinkStation
 P920 Rack Workstation (ThinkStation) — Lenovo XClarity Energy Manager (LXEM) affected.
P920 Rack Workstation (ThinkStation) — Lenovo XClarity Energy Manager (LXEM) affected.
ThinkSystem
 Storman command line tool (For Linux) — SR530, SR550, SR570, SR590, SR630, SR630V2, SR645, SR650, SR650V2, SR665, SR850V2, SR860V2, ST550, ST558 ThinkSystems affected.
Storman command line tool (For Linux) — SR530, SR550, SR570, SR590, SR630, SR630V2, SR645, SR650, SR650V2, SR665, SR850V2, SR860V2, ST550, ST558 ThinkSystems affected. Storman command line tool (For VMWare) — SR530, SR550, SR570, SR590, SR630, SR630V2, SR645, SR650, SR650V2, SR665, SR850V2, SR860V2, ST550, ST558 ThinkSystems affected.
Storman command line tool (For VMWare) — SR530, SR550, SR570, SR590, SR630, SR630V2, SR645, SR650, SR650V2, SR665, SR850V2, SR860V2, ST550, ST558 ThinkSystems affected. Storman command line tool (For Windows) — SR530, SR550, SR570, SR590, SR630, SR630V2, SR645, SR650, SR650V2, SR665, SR850V2, SR860V2, ST550, ST558 ThinkSystems affected.
Storman command line tool (For Windows) — SR530, SR550, SR570, SR590, SR630, SR630V2, SR645, SR650, SR650V2, SR665, SR850V2, SR860V2, ST550, ST558 ThinkSystems affected.
Lightbend #
 Lagom Framework — Uses log4j, affected if not updated.
Lagom Framework — Uses log4j, affected if not updated.
LOGalyze #
 SIEM & log analyzer tool — Versions affected: v4.X
SIEM & log analyzer tool — Versions affected: v4.X
McAfee #
 Advanced Threat Defense — Affected versions: 4.2.X, 4.4.X, 4.6.X, 4.8.X, 4.12.X
Advanced Threat Defense — Affected versions: 4.2.X, 4.4.X, 4.6.X, 4.8.X, 4.12.X Application and Change Control — Affected versions: 6.1, 6.2.X - 6.5.X, 7.0.X, 8.0.X, 8.2.X, 8.3.X
Application and Change Control — Affected versions: 6.1, 6.2.X - 6.5.X, 7.0.X, 8.0.X, 8.2.X, 8.3.X Cloud Workload Security — Affected versions: 5.2.X, 5.3.X
Cloud Workload Security — Affected versions: 5.2.X, 5.3.X Content Security Reporter — Affected versions: 1.X - 2.X
Content Security Reporter — Affected versions: 1.X - 2.X Data Exchange Layer — Affected versions: 5.X, 6.X
Data Exchange Layer — Affected versions: 5.X, 6.X Data Loss Prevention Endpoint — Affected versions: 11.6.X
Data Loss Prevention Endpoint — Affected versions: 11.6.X Data Loss Prevention Monitor — Affected versions: 11.X
Data Loss Prevention Monitor — Affected versions: 11.X Data Loss Prevention Prevent — Affected versions: 11.X
Data Loss Prevention Prevent — Affected versions: 11.X Database Activity Monitoring — Affected versions: 4.6.X, 4.7.X, 4.8.X, 5.2.X, 5.3.X
Database Activity Monitoring — Affected versions: 4.6.X, 4.7.X, 4.8.X, 5.2.X, 5.3.X Drive Encryption — Affected versions: 7.2, 7.3.X
Drive Encryption — Affected versions: 7.2, 7.3.X Endpoint Security Firewall — Affected versions: 10.6.X, 10.7.X
Endpoint Security Firewall — Affected versions: 10.6.X, 10.7.X Endpoint Security for Linux Firewall — Affected versions: 10.6.X, 10.7.X
Endpoint Security for Linux Firewall — Affected versions: 10.6.X, 10.7.X Endpoint Security for Linux Threat Prevention — Affected versions: 10.X
Endpoint Security for Linux Threat Prevention — Affected versions: 10.X Endpoint Security for Mac Firewall — Affected versions: 10.X
Endpoint Security for Mac Firewall — Affected versions: 10.X Endpoint Security for Mac Threat Prevention — Affected versions: 10.X
Endpoint Security for Mac Threat Prevention — Affected versions: 10.X Endpoint Security for Mac Web Control — Affected versions: 10.X
Endpoint Security for Mac Web Control — Affected versions: 10.X Endpoint Security for Servers — Affected versions: 5.0.X, 5.1.X
Endpoint Security for Servers — Affected versions: 5.0.X, 5.1.X Endpoint Security Threat Prevention — Affected versions: 10.6.X, 10.7.X
Endpoint Security Threat Prevention — Affected versions: 10.6.X, 10.7.X Endpoint Security Web Control — Affected versions: 10.6.X, 10.7.X
Endpoint Security Web Control — Affected versions: 10.6.X, 10.7.X ePolicy Orchestrator — Affected versions: 5.10.X
ePolicy Orchestrator — Affected versions: 5.10.X File and Removable Media Protection — Affected versions: 5.1.X, 5.2.X, 5.3.X, 5.4.X
File and Removable Media Protection — Affected versions: 5.1.X, 5.2.X, 5.3.X, 5.4.X Management of Native Encryption — Affected versions: 4.X, 5.X
Management of Native Encryption — Affected versions: 4.X, 5.X McAfee Active Response — Affected versions: 2.X
McAfee Active Response — Affected versions: 2.X McAfee Agent — Affected versions: 10.6.X, 10.7.X
McAfee Agent — Affected versions: 10.6.X, 10.7.X McAfee Client Proxy — Affected versions: 2.3.X, 2.4.X, 2.5.X, 3.X, 4.X
McAfee Client Proxy — Affected versions: 2.3.X, 2.4.X, 2.5.X, 3.X, 4.X MOVE Antivirus Agentless — Affected versions: 4.7.X, 4.8.X, 4.9.X
MOVE Antivirus Agentless — Affected versions: 4.7.X, 4.8.X, 4.9.X MOVE Antivirus Multi-platform — Affected versions: 4.6.X, 4.7.X, 4.8.X, 4.9.X
MOVE Antivirus Multi-platform — Affected versions: 4.6.X, 4.7.X, 4.8.X, 4.9.X MVISION Cloud CASB Connect — Affected.
MVISION Cloud CASB Connect — Affected. MVISION EDR — All versions affected.
MVISION EDR — All versions affected. MVISION Endpoint — All versions affected.
MVISION Endpoint — All versions affected. Network Security Manager — Affected versions: 9.1.X, 9.2.X
Network Security Manager — Affected versions: 9.1.X, 9.2.X Network Security Sensor Appliance — Affected versions: 9.1.X, 9.2.X, 10.X
Network Security Sensor Appliance — Affected versions: 9.1.X, 9.2.X, 10.X Network Security Signature Set — Affected.
Network Security Signature Set — Affected. Security for Microsoft Exchange — Affected versions: 8.5, 8.6, 8.7, 8.8
Security for Microsoft Exchange — Affected versions: 8.5, 8.6, 8.7, 8.8 SIEM Enterprise Security Manager — Affected versions: 11.1.X, 11.2.X, 11.3.X, 11.4.X, 11.5.X
SIEM Enterprise Security Manager — Affected versions: 11.1.X, 11.2.X, 11.3.X, 11.4.X, 11.5.X Threat Intelligence Exchange Server — Affected versions: 2.2.X, 3.X
Threat Intelligence Exchange Server — Affected versions: 2.2.X, 3.X Threat Prevention and Removal — Affected.
Threat Prevention and Removal — Affected. Unified Cloud Edge — Affected.
Unified Cloud Edge — Affected. VirusScan Enterprise — Affected.
VirusScan Enterprise — Affected. Vulnerability Response — Affected.
Vulnerability Response — Affected. Web Gateway — Affected versions: 7.8, 8.0.X - 8.2.X, 9.0.X - 9.2.X, 10.0.X - 10.2.X, 11.X
Web Gateway — Affected versions: 7.8, 8.0.X - 8.2.X, 9.0.X - 9.2.X, 10.0.X - 10.2.X, 11.X
Microfocus #
 ALM Octane — All versions affected.
ALM Octane — All versions affected. ALM/Quality Center — Affected versions: 15.5.0, 15.5.1 (SP1), 15.5.1 Patch 01, 15.5.1 Patch02, 16.0.0
ALM/Quality Center — Affected versions: 15.5.0, 15.5.1 (SP1), 15.5.1 Patch 01, 15.5.1 Patch02, 16.0.0 AMX — Affected versions: 2021.08, 2021.11
AMX — Affected versions: 2021.08, 2021.11 Application Performance Management (APM) — Affected versions: 9.40, 9.50, 9.51
Application Performance Management (APM) — Affected versions: 9.40, 9.50, 9.51
CyberRes
 ArcSight ArcSight Platform (Containerized) — All versions affected.
ArcSight ArcSight Platform (Containerized) — All versions affected. ArcSight Connectors — Affected versions: 8.2 and above
ArcSight Connectors — Affected versions: 8.2 and above ArcSight Enterprise Security Manager (ESM) — Affected versions: 7.2, 7.5
ArcSight Enterprise Security Manager (ESM) — Affected versions: 7.2, 7.5 ArcSight Interset — Affected versions: 5.X and above
ArcSight Interset — Affected versions: 5.X and above ArcSight Logger — Affected versions: 7.2 and above
ArcSight Logger — Affected versions: 7.2 and above ArcSight Recon — Affected versions: 1.1.1 and 1.2 (non SaaS)
ArcSight Recon — Affected versions: 1.1.1 and 1.2 (non SaaS) ArcSight Sentinel — Affected versions: 8.2 to 8.5
ArcSight Sentinel — Affected versions: 8.2 to 8.5 ArcSight Transformation Hub — All versions affected.
ArcSight Transformation Hub — All versions affected. AutoPass License Server (APLS) — Affected versions: 11.7.X, 11.8.X, 11.9.X, 12.0.X, 12.1.0, 12.1.1, 12.1.2
AutoPass License Server (APLS) — Affected versions: 11.7.X, 11.8.X, 11.9.X, 12.0.X, 12.1.0, 12.1.1, 12.1.2 Change Guardian — Affected versions: 5.2, 6.0, 6.1, 6.2
Change Guardian — Affected versions: 5.2, 6.0, 6.1, 6.2 Data Protector - Cell Console (CC) and Reporting Server (RS) components — Affected versions: 10.20, 10.30, 10.40, 10.50, 10.60, 10.70, 10.80, 10.90, 10.91, 11.00
Data Protector - Cell Console (CC) and Reporting Server (RS) components — Affected versions: 10.20, 10.30, 10.40, 10.50, 10.60, 10.70, 10.80, 10.90, 10.91, 11.00 Database and Middleware Automation (DMA) — Affected versions: 10.62.0.0
Database and Middleware Automation (DMA) — Affected versions: 10.62.0.0 Dimensions CM — Affected versions: 14.5.X
Dimensions CM — Affected versions: 14.5.X Fortify Application Defender — Affected versions: 20.1 and newer
Fortify Application Defender — Affected versions: 20.1 and newer Fortify Audit Assistant — Affected versions: 19.2 and newer
Fortify Audit Assistant — Affected versions: 19.2 and newer Fortify Java Runtime Agent — Affected versions: 20.1 and newer
Fortify Java Runtime Agent — Affected versions: 20.1 and newer Fortify ScanCentral (SAST) — Affected versions: 20.1 and newer
Fortify ScanCentral (SAST) — Affected versions: 20.1 and newer Fortify Software Security Center — Affected versions: 20.1 and newer
Fortify Software Security Center — Affected versions: 20.1 and newer Fortify Static Code Analyzer (SCA_and_Apps) — Affected versions: 20.1 and newer
Fortify Static Code Analyzer (SCA_and_Apps) — Affected versions: 20.1 and newer GroupWise — Affected versions: 18.0.0, 18.0.1, 18.0.2, 18.1, 18.1.1, 18.2, 18.2.1, 18.3, 18.3.1
GroupWise — Affected versions: 18.0.0, 18.0.1, 18.0.2, 18.1, 18.1.1, 18.2, 18.2.1, 18.3, 18.3.1 GroupWise TeamWorks — Affected versions: 18.1.1, 18.2.0, 18.2.1
GroupWise TeamWorks — Affected versions: 18.1.1, 18.2.0, 18.2.1 Identity Manager — Affected versions: 1.32.0
Identity Manager — Affected versions: 1.32.0 LoadRunner Enterprise — Affected versions: 2020, 2020SP1, 2020SP2, 2020SP3,2021, 2021R1, 2021R2
LoadRunner Enterprise — Affected versions: 2020, 2020SP1, 2020SP2, 2020SP3,2021, 2021R1, 2021R2 MF Connect — All versions affected.
MF Connect — All versions affected. NetIQ Access Manager — Affected versions: 4.5 and newer
NetIQ Access Manager — Affected versions: 4.5 and newer NetIQ Advanced Authentication — Affected versions: 6.0 and newer
NetIQ Advanced Authentication — Affected versions: 6.0 and newer NetIQ Change Guardian — Affected versions: 5.2 to 6.2
NetIQ Change Guardian — Affected versions: 5.2 to 6.2 NetIQ Risk Services — Affected versions: 1.0 and newer
NetIQ Risk Services — Affected versions: 1.0 and newer NetIQ SecureLogin Advanced Edition — Affected versions: 9.0.0.2
NetIQ SecureLogin Advanced Edition — Affected versions: 9.0.0.2 Operations Bridge Manager (OBM) — Affected versions: 2021.11 and older
Operations Bridge Manager (OBM) — Affected versions: 2021.11 and older PVCS Version Manager — Affected versions: 8.6.0, 8.6.1, 8.6.2, 8.6.3
PVCS Version Manager — Affected versions: 8.6.0, 8.6.1, 8.6.2, 8.6.3 Retain Unified Archiving — Affected versions: 4.9.2, 4.10
Retain Unified Archiving — Affected versions: 4.9.2, 4.10 Server Automation Reporting with OPTIC DL — Affected versions: 10.60, 2018.08, 2020.11
Server Automation Reporting with OPTIC DL — Affected versions: 10.60, 2018.08, 2020.11 Service Manager (SM) Chat Server — Affected versions: 9.64, 9.70, 9.71
Service Manager (SM) Chat Server — Affected versions: 9.64, 9.70, 9.71 Service Manager (SM) Mobility — Affected versions: 9.70, 9.71
Service Manager (SM) Mobility — Affected versions: 9.70, 9.71 Service Manager (SM) Server — Affected versions: 9.70, 9.71
Service Manager (SM) Server — Affected versions: 9.70, 9.71 Service Manager (SM) Web Tier — Affected versions: 9.70, 9.71
Service Manager (SM) Web Tier — Affected versions: 9.70, 9.71 SMAX — Affected versions: 2020.11, 2021.02, 2021.05, 2021.08, 2021.11
SMAX — Affected versions: 2020.11, 2021.02, 2021.05, 2021.08, 2021.11 Structured Data Manager (SDM) — Affected versions: 7.6.1, 7.6.2, 7.6.3, 7.6.4, 7.6.5 R2, 7.6.5 R3
Structured Data Manager (SDM) — Affected versions: 7.6.1, 7.6.2, 7.6.3, 7.6.4, 7.6.5 R2, 7.6.5 R3 UFT Developer (LeanFT) — Affected versions: 14.5x up to 2021
UFT Developer (LeanFT) — Affected versions: 14.5x up to 2021 Voltage SecureData Sentry — Affected versions: 4.3 and below
Voltage SecureData Sentry — Affected versions: 4.3 and below Voltage Structured Data Manager — Affected versions: 7.6.1 and newer
Voltage Structured Data Manager — Affected versions: 7.6.1 and newer ZENworks — Affected versions: 2020 Update 1, 2020 Update 2, Reporting Server 7.8.0
ZENworks — Affected versions: 2020 Update 1, 2020 Update 2, Reporting Server 7.8.0 ZMF4ECL — All versions affected.
ZMF4ECL — All versions affected.
Microsoft #
 Azure DevOps Server — Versions 2020 & earlier affected.
Azure DevOps Server — Versions 2020 & earlier affected. Team Foundation Server — Versions 2018.2+ affected.
Team Foundation Server — Versions 2018.2+ affected.
Mimecast #
 Mimecast — Affected services have been patched.
Mimecast — Affected services have been patched.
MobileIron #
 Core — Versions affected: All Versions
Core — Versions affected: All Versions Core Connector — Versions affected: All Versions
Core Connector — Versions affected: All Versions Reporting Database (RDB) — Versions affected: All Versions
Reporting Database (RDB) — Versions affected: All Versions Sentry — Versions affected: 9.13, 9.14
Sentry — Versions affected: 9.13, 9.14
Mulesoft #
 Anypoint Studio — Versions affected: 7.X
Anypoint Studio — Versions affected: 7.X Mule Agent — Versions affected: 6.X
Mule Agent — Versions affected: 6.X Mule Runtime — Versions affected: 3.X,4.X
Mule Runtime — Versions affected: 3.X,4.X
NetApp #
 Active IQ Unified Manager (Linux, Windows, vSphere) — Affected
Active IQ Unified Manager (Linux, Windows, vSphere) — Affected Brocade SAN Naviator — Affected
Brocade SAN Naviator — Affected Cloud Insights Acquisition Unit — Affected
Cloud Insights Acquisition Unit — Affected Cloud Manager — Affected
Cloud Manager — Affected Cloud Secure — Affected
Cloud Secure — Affected OnCommand Insight — Affected
OnCommand Insight — Affected ONTAP Tools for VMware vSphere — Affected
ONTAP Tools for VMware vSphere — Affected SnapCenter Plug-in for VMware vSphere — Affected
SnapCenter Plug-in for VMware vSphere — Affected
New Relic #
 Containerized Private Minion (CPM) — Affected, fixed in v3.0.58
Containerized Private Minion (CPM) — Affected, fixed in v3.0.58 Helm Charts (uses CPM) — Affected, fixed in v1.0.46
Helm Charts (uses CPM) — Affected, fixed in v1.0.46 New Relic Java Agent — Affected, fixed in v7.4.3
New Relic Java Agent — Affected, fixed in v7.4.3
Nutanix #
 AOS STS — Affected, patched in v6.0.2.4
AOS STS — Affected, patched in v6.0.2.4 File Analytics — Affected versions: 2.1.x, 2.2.x, 3.0+. Mitigation steps available for 2.1.x, 2.2.x, download available in 3.0.1.
File Analytics — Affected versions: 2.1.x, 2.2.x, 3.0+. Mitigation steps available for 2.1.x, 2.2.x, download available in 3.0.1. Karbon — All versions affected, mitigation steps available.
Karbon — All versions affected, mitigation steps available. Mine — All versions affected, mitigation steps available.
Mine — All versions affected, mitigation steps available. Objects — All versions affected, mitigation steps available.
Objects — All versions affected, mitigation steps available. SaaS-based Products — Most affected products have been patched, WAF mitigations in place.
SaaS-based Products — Most affected products have been patched, WAF mitigations in place. Witness VM — All versions affected, mitigation steps available.
Witness VM — All versions affected, mitigation steps available.
Okta #
 On-Prem MFA Agent — Radius Server Agent & On-Prem MFA Agent.
On-Prem MFA Agent — Radius Server Agent & On-Prem MFA Agent. RADIUS Server Agent
RADIUS Server Agent
OneSpan #
Digipass authentication products
 Application Shielding server sample code
Application Shielding server sample code Mobile Authenticator Studio (MAS) server sample code
Mobile Authenticator Studio (MAS) server sample code Mobile Security Suite (MSS) Notification SDK Server
Mobile Security Suite (MSS) Notification SDK Server
On-premises server products
Oracle #
 Enterprise Manager — Affected versions: 13.3.2, 13.4, & 13.5. Note that Oracle has currently restricted access to vulnerable product info, this info is from the CISA.
Enterprise Manager — Affected versions: 13.3.2, 13.4, & 13.5. Note that Oracle has currently restricted access to vulnerable product info, this info is from the CISA. Exadata — Affected versions: < 21.3.4. Note that Oracle has currently restricted access to vulnerable product info, this info is from the CISA.
Exadata — Affected versions: < 21.3.4. Note that Oracle has currently restricted access to vulnerable product info, this info is from the CISA.
OVHcloud #
 Hosted Private Cloud — Affected; Several products powered by VMware
Hosted Private Cloud — Affected; Several products powered by VMware Internal systems — Possibly affected; Still investigating
Internal systems — Possibly affected; Still investigating
OxygenXML #
 Batch Documents Converter — Versions affected: v3.2.0 and older
Batch Documents Converter — Versions affected: v3.2.0 and older Git Client — Versions affected: v3.0.0 & older
Git Client — Versions affected: v3.0.0 & older Oxygen Content Fusion — Versions affected: 2.0, 3.0, 4.1
Oxygen Content Fusion — Versions affected: 2.0, 3.0, 4.1 Oxygen Feedback Enterprise — Versions affected: 1.4.4 & older
Oxygen Feedback Enterprise — Versions affected: 1.4.4 & older Oxygen License Server — Versions affected: v22.1 to v24.0
Oxygen License Server — Versions affected: v22.1 to v24.0 Oxygen PDF Chemistry — Versions affected: v22.1, 23.0, 23.1, 24.0
Oxygen PDF Chemistry — Versions affected: v22.1, 23.0, 23.1, 24.0 Oxygen SDK — Versions affected: v22.1.0.0, v23.0.0.0 to v23.1.0.0, v24.0.0.0
Oxygen SDK — Versions affected: v22.1.0.0, v23.0.0.0 to v23.1.0.0, v24.0.0.0 Oxygen Web Author — Versions affected: v22.1.0, v23.0.0 to v23.1.1, v24.0.0
Oxygen Web Author — Versions affected: v22.1.0, v23.0.0 to v23.1.1, v24.0.0 Oxygen Web Author Test Server Add-on — Versions affected: between v22.1.0 and v24.0.0
Oxygen Web Author Test Server Add-on — Versions affected: between v22.1.0 and v24.0.0 Oxygen XML Author — Versions affected: between v16.1 and v22.0, v22.1, 23.0, 23.1, 24.0
Oxygen XML Author — Versions affected: between v16.1 and v22.0, v22.1, 23.0, 23.1, 24.0 Oxygen XML Developer — Versions affected: between v16.1 and v22.0, v22.1, 23.0, 23.1, 24.0
Oxygen XML Developer — Versions affected: between v16.1 and v22.0, v22.1, 23.0, 23.1, 24.0 Oxygen XML Editor — Versions affected: between v16.1 and v22.0, v22.1, 23.0, 23.1, 24.0
Oxygen XML Editor — Versions affected: between v16.1 and v22.0, v22.1, 23.0, 23.1, 24.0 Oxygen XML Publishing Engine — Versions affected: v22.1, v23.0 to v23.1, v24.0
Oxygen XML Publishing Engine — Versions affected: v22.1, v23.0 to v23.1, v24.0 Oxygen XML WebHelp — Versions affected: v22.1, 23.0, 23.1, 24.0
Oxygen XML WebHelp — Versions affected: v22.1, 23.0, 23.1, 24.0 Web Author PDF Plugin — Versions affected: v23.0.0.0, v24.0.0.0
Web Author PDF Plugin — Versions affected: v23.0.0.0, v24.0.0.0 XSD to JSON Schema Converter — Versions affected: v22.0 and v24.0
XSD to JSON Schema Converter — Versions affected: v22.0 and v24.0
Palo-Alto Networks #
 Palo-Alto Networks-OS for Panorama — Versions affected: 9.0, 9.1, 10.0
Palo-Alto Networks-OS for Panorama — Versions affected: 9.0, 9.1, 10.0
Ping Identity #
 PingAccess — Versions affected: 4.0 <= version <= 6.3.2
PingAccess — Versions affected: 4.0 <= version <= 6.3.2 PingFederate — Versions affected: 8.0 <= version <= 10.3.4
PingFederate — Versions affected: 8.0 <= version <= 10.3.4 PingFederate Java Integration Kit — Versions affected: < 2.7.2
PingFederate Java Integration Kit — Versions affected: < 2.7.2 PingFederate OAuth Playground — Versions affected: < 4.3.1
PingFederate OAuth Playground — Versions affected: < 4.3.1
Polycom #
 Poly Clariti Core/Edge (DMA/CCE) — Versions affected: 9.0 and above
Poly Clariti Core/Edge (DMA/CCE) — Versions affected: 9.0 and above
PortEx #
 Portex — Versions affected: <3.0.2
Portex — Versions affected: <3.0.2
Positive Technologies #
Progress #
PTV Group #
Software Solutions for Traffic & Mobility
 PTV MaaS Modeller — Affected.
PTV MaaS Modeller — Affected. PTV Map&Market — Possibly affected.
PTV Map&Market — Possibly affected. PTV Route Optimiser CL — Possibly affected.
PTV Route Optimiser CL — Possibly affected. PTV Route Optimiser ST — Possibly affected.
PTV Route Optimiser ST — Possibly affected. PTV xServer 1.34 (on prem) — Affected.
PTV xServer 1.34 (on prem) — Affected.
PureStorage #
 FlashArray — Affected versions: Purity//FA 5.3.x, Purity//FA 6.0.x, Purity//FA 6.1.x, Purity//FA 6.2.x
FlashArray — Affected versions: Purity//FA 5.3.x, Purity//FA 6.0.x, Purity//FA 6.1.x, Purity//FA 6.2.x FlashBlade — Affected versions: Purity//FB 3.0.x, Purity//FB 3.1.x, Purity//FB 3.2.x, Purity//FB 3.3.x
FlashBlade — Affected versions: Purity//FB 3.0.x, Purity//FB 3.1.x, Purity//FB 3.2.x, Purity//FB 3.3.x Portworx — Affected versions: 2.8.0+ with telemetry enabled
Portworx — Affected versions: 2.8.0+ with telemetry enabled Pure Cloud Block Store — Affected versions: 6.1.xPAZ, 6.1.xPAWS, 6.2.xPAZ, 6.2.xPAWS
Pure Cloud Block Store — Affected versions: 6.1.xPAZ, 6.1.xPAWS, 6.2.xPAZ, 6.2.xPAWS Pure VMA Collector — Affected versions: v3.x
Pure VMA Collector — Affected versions: v3.x
Qlik #
 Compose for Data Lakes — Version 6.6 affected.
Compose for Data Lakes — Version 6.6 affected. Compose for Data Warehouses versions 6.6, 6.6.1, 7.0 — Version 6.6+ affected.
Compose for Data Warehouses versions 6.6, 6.6.1, 7.0 — Version 6.6+ affected. Compose versions 2021.2, 2021.5, 2021.8 — Current version resolved
Compose versions 2021.2, 2021.5, 2021.8 — Current version resolved Enterprise Manager versions 6.6, 7.0, 2021.5, 2021.11 — Version 6.6, 7.0 and 2021.5+ affected.
Enterprise Manager versions 6.6, 7.0, 2021.5, 2021.11 — Version 6.6, 7.0 and 2021.5+ affected. GeoAnalytics and GeoAnalytics Plus — Version May 2021 and higher
GeoAnalytics and GeoAnalytics Plus — Version May 2021 and higher Qlik Catalog – May 2021 — May 2021 release and onward affected.
Qlik Catalog – May 2021 — May 2021 release and onward affected. Replicate versions 6.6, 7.0, 2021.5, 2021.11 — Version 6.6, 7.0 and 2021.5+ affected.
Replicate versions 6.6, 7.0, 2021.5, 2021.11 — Version 6.6, 7.0 and 2021.5+ affected.
QMATIC #
 Appointment Booking — Versions affected: 2.4+
Appointment Booking — Versions affected: 2.4+ Insights — Versions affected: Cloud
Insights — Versions affected: Cloud
Rapid7 #
 InsightOps DataHub — Versions affected: InsightOps DataHub <= 2.0
InsightOps DataHub — Versions affected: InsightOps DataHub <= 2.0 InsightOps r7insight_java logging library — Versions affected: <=3.0.8
InsightOps r7insight_java logging library — Versions affected: <=3.0.8 Logentries DataHub — Versions affected: Linux version <= 1.2.0.820; Windows version <= 1.2.0.820
Logentries DataHub — Versions affected: Linux version <= 1.2.0.820; Windows version <= 1.2.0.820 Logentries le_java logging library — Versions affected: All versions: this is a deprecated component
Logentries le_java logging library — Versions affected: All versions: this is a deprecated component
Real-Time Innovations (RTI) #
 RTI Micro Application Generator (MAG), as part of RTI Connext Micro — Versions affected: 3.0.0, 3.0.1, 3.0.2, 3.0.3
RTI Micro Application Generator (MAG), as part of RTI Connext Micro — Versions affected: 3.0.0, 3.0.1, 3.0.2, 3.0.3 RTI Micro Application Generator (MAG), as part of RTI Connext Professional — Versions affected: 6.0.0 and 6.0.1
RTI Micro Application Generator (MAG), as part of RTI Connext Professional — Versions affected: 6.0.0 and 6.0.1
Redhat #
Cloud Computing
 OpenShift 3.11 — This issue has been assigned CVE-2021-44228 and rated with a severity impact of Critical.
OpenShift 3.11 — This issue has been assigned CVE-2021-44228 and rated with a severity impact of Critical. OpenShift 4 — This issue has been assigned CVE-2021-44228 and rated with a severity impact of Critical.
OpenShift 4 — This issue has been assigned CVE-2021-44228 and rated with a severity impact of Critical. OpenShift Logging — This issue has been assigned CVE-2021-44228 and rated with a severity impact of Critical.
OpenShift Logging — This issue has been assigned CVE-2021-44228 and rated with a severity impact of Critical. OpenStack Platform 13 — This issue has been assigned CVE-2021-44228 and rated with a severity impact of Critical.
OpenStack Platform 13 — This issue has been assigned CVE-2021-44228 and rated with a severity impact of Critical.
Cloud Computing/Runtimes
 OpenShift Application Runtimes Vert.X 4 — This issue has been assigned CVE-2021-44228 and rated with a severity impact of Critical.
OpenShift Application Runtimes Vert.X 4 — This issue has been assigned CVE-2021-44228 and rated with a severity impact of Critical.
Integration & Automation
 AMQ Streaming — Upgrade to version 1.8.4.
AMQ Streaming — Upgrade to version 1.8.4. Fuse 7 — Upgrade to version 7.10.0.
Fuse 7 — Upgrade to version 7.10.0. Integration Camel K — Affected.
Integration Camel K — Affected. Integration Camel Quarkus — Affected.
Integration Camel Quarkus — Affected. Process Automation 7 — Affected.
Process Automation 7 — Affected.
Runtimes
 Data Grid 8 — Upgrade to version 8.2.2.
Data Grid 8 — Upgrade to version 8.2.2. JBoss Enterprise Application Platform 7 — Affected, apply security update for v7.4.
JBoss Enterprise Application Platform 7 — Affected, apply security update for v7.4.
Other
 CodeReady Studio 12 — Affected.
CodeReady Studio 12 — Affected.
Redis #
 Jedis — Versions affected: 3.7.1, 4.0.0-rc2
Jedis — Versions affected: 3.7.1, 4.0.0-rc2
Revenera #
 Code Aware — Affected, 2020 R2.
Code Aware — Affected, 2020 R2. FlexNet Embedded — Affected, FlexNet License Server Manager (FLSM).
FlexNet Embedded — Affected, FlexNet License Server Manager (FLSM). FlexNet Operations Cloud ALM — Affected, Revenera managed services: Core module, Updates and Insights, Data Access APIs
FlexNet Operations Cloud ALM — Affected, Revenera managed services: Core module, Updates and Insights, Data Access APIs FlexNet Operations On-Premises — Affected, Core module.
FlexNet Operations On-Premises — Affected, Core module. FlexNet Publisher — Affected, 2021 R4 (11.18.3.0), only when using lmadmin alerts example code.
FlexNet Publisher — Affected, 2021 R4 (11.18.3.0), only when using lmadmin alerts example code. InstallAnywhere — Affected, 2018 (only when using CodeAware).
InstallAnywhere — Affected, 2018 (only when using CodeAware). InstallShield — Affected, 2016 SP2, 2018 (only when using CodeAware).
InstallShield — Affected, 2016 SP2, 2018 (only when using CodeAware). Usage Intelligence — Affected, Java SDK.
Usage Intelligence — Affected, Java SDK.
Rockwell Automation #
 FactoryTalk Analytics DataFlowML — Versions affected: 4.00.00
FactoryTalk Analytics DataFlowML — Versions affected: 4.00.00 FactoryTalk Analytics DataView — Versions affected: 3.03.00
FactoryTalk Analytics DataView — Versions affected: 3.03.00 MES EIG — Versions affected: 3.03.00
MES EIG — Versions affected: 3.03.00 Warehouse Management — Versions affected: 4.01.00, 4.02.00, 4.02.01, 4.02.02
Warehouse Management — Versions affected: 4.01.00, 4.02.00, 4.02.01, 4.02.02
Ruckus #
 Virtual SmartZone (vSZ) — Versions affected: 5.1 to 6.0
Virtual SmartZone (vSZ) — Versions affected: 5.1 to 6.0
SBT #
 SBT — Versions affected: < 1.5.6
SBT — Versions affected: < 1.5.6
Schneider Electric #
 EASYFIT — Versions affected: Current software and earlier
EASYFIT — Versions affected: Current software and earlier Ecoreal XL — Versions affected: Current software and earlier
Ecoreal XL — Versions affected: Current software and earlier Eurotherm Data Reviewer — Versions affected: V3.0.2 and prior
Eurotherm Data Reviewer — Versions affected: V3.0.2 and prior MSE — Versions affected: Current software and earlier
MSE — Versions affected: Current software and earlier NetBotz750/755 — Versions affected: Software versions 5.0 through 5.3.0
NetBotz750/755 — Versions affected: Software versions 5.0 through 5.3.0 NEW630 — Versions affected: Current software and earlier
NEW630 — Versions affected: Current software and earlier SDK BOM — Versions affected: Current software and earlier
SDK BOM — Versions affected: Current software and earlier SDK-Docgen — Versions affected: Current software and earlier
SDK-Docgen — Versions affected: Current software and earlier SDK-TNC — Versions affected: Current software and earlier
SDK-TNC — Versions affected: Current software and earlier SDK-UMS — Versions affected: Current software and earlier
SDK-UMS — Versions affected: Current software and earlier SDK3D2DRenderer — Versions affected: Current software and earlier
SDK3D2DRenderer — Versions affected: Current software and earlier SDK3D360Widget — Versions affected: Current software and earlier
SDK3D360Widget — Versions affected: Current software and earlier Select and Config DATA — Versions affected: Current software and earlier
Select and Config DATA — Versions affected: Current software and earlier SNC-API — Versions affected: Current software and earlier
SNC-API — Versions affected: Current software and earlier SNC-CMM — Versions affected: Current software and earlier
SNC-CMM — Versions affected: Current software and earlier SNCSEMTECH — Versions affected: Current software and earlier
SNCSEMTECH — Versions affected: Current software and earlier SPIMV3 — Versions affected: Current software and earlier
SPIMV3 — Versions affected: Current software and earlier SWBEditor — Versions affected: Current software and earlier
SWBEditor — Versions affected: Current software and earlier SWBEngine — Versions affected: Current software and earlier
SWBEngine — Versions affected: Current software and earlier
Siemens #
 Advantage Navigator Energy & Sustainability — Versions affected: < 2021-12-13
Advantage Navigator Energy & Sustainability — Versions affected: < 2021-12-13 Advantage Navigator Software Proxy — Versions affected: All Versions
Advantage Navigator Software Proxy — Versions affected: All Versions Capital — Versions affected: >= 2019.1 SP1912 only if Teamcenter integration feature is used
Capital — Versions affected: >= 2019.1 SP1912 only if Teamcenter integration feature is used Cerberus DMS — Versions affected: V5.0, V5.1 with Advanced Reporting EM installed
Cerberus DMS — Versions affected: V5.0, V5.1 with Advanced Reporting EM installed Comos Desktop App — Versions affected: All Versions
Comos Desktop App — Versions affected: All Versions Desigo CC — Versions affected: V3.0, V4.0, V4.1, V4.2 with Advanced Reporting EM installed
Desigo CC — Versions affected: V3.0, V4.0, V4.1, V4.2 with Advanced Reporting EM installed E-Car OC Cloud Application — Versions affected: < 2021-12-13
E-Car OC Cloud Application — Versions affected: < 2021-12-13 Energy Engage — Versions affected: V3.1
Energy Engage — Versions affected: V3.1 EnergyIP — Versions affected: V8.5, V8.6, V8.7, V9.0
EnergyIP — Versions affected: V8.5, V8.6, V8.7, V9.0 EnergyIP Prepay — Versions affected: V3.7. V3.8
EnergyIP Prepay — Versions affected: V3.7. V3.8 Enlightened Amaze — Versions affected: <2021-12-10
Enlightened Amaze — Versions affected: <2021-12-10 Enlightened Where — Versions affected: <2021-12-11
Enlightened Where — Versions affected: <2021-12-11 Geolus Shape Search V10 — Versions affected: All Versions
Geolus Shape Search V10 — Versions affected: All Versions Geolus Shape Search V11 — Versions affected: All Version
Geolus Shape Search V11 — Versions affected: All Version GMA-Manager — Versions affected: All Version >=V8.6.2j-398 and <V8.6.2-472
GMA-Manager — Versions affected: All Version >=V8.6.2j-398 and <V8.6.2-472 HES UDIS — Versions affected: All Versions
HES UDIS — Versions affected: All Versions Industrial Edge Management App (IEM-App) — Versions affected: All Versions
Industrial Edge Management App (IEM-App) — Versions affected: All Versions Industrial Edge Management Hub — Versions affected: < 2021-12-13
Industrial Edge Management Hub — Versions affected: < 2021-12-13 Industrial Edge Management OS (IEM-OS) — Versions affected: All Versions
Industrial Edge Management OS (IEM-OS) — Versions affected: All Versions Mendix Applications — Versions affected: All Versions
Mendix Applications — Versions affected: All Versions MindSphere App Management Cockpits (Developer & Operator) — Versions affected: < 2021-12-16
MindSphere App Management Cockpits (Developer & Operator) — Versions affected: < 2021-12-16 MindSphere Asset Manager — Versions affected: < 2021-12-16
MindSphere Asset Manager — Versions affected: < 2021-12-16 MindSphere Cloud Foundry — Versions affected: < 2021-12-14
MindSphere Cloud Foundry — Versions affected: < 2021-12-14 MindSphere Cloud Platform — Versions affected: < 2021-12-11
MindSphere Cloud Platform — Versions affected: < 2021-12-11 MindSphere IAM (User Management/Settings) — Versions affected: All Versions
MindSphere IAM (User Management/Settings) — Versions affected: All Versions MindSphere Integrated Data Lake — Versions affected: < 2021-12-16
MindSphere Integrated Data Lake — Versions affected: < 2021-12-16 MindSphere Notification Service — Versions affected: < 2021-12-16
MindSphere Notification Service — Versions affected: < 2021-12-16 MindSphere Predictive Learning — Versions affected: All Versions
MindSphere Predictive Learning — Versions affected: All Versions MindSphere Usage Transparency Service — Versions affected: < 2021-12-16
MindSphere Usage Transparency Service — Versions affected: < 2021-12-16 MindSphere Visual Explorer — Versions affected: All Versions
MindSphere Visual Explorer — Versions affected: All Versions NX — Versions affected: All Versions
NX — Versions affected: All Versions Opcenter EX CP Process Automation Control — Versions affected: >= V17.2.3 and < V18.1
Opcenter EX CP Process Automation Control — Versions affected: >= V17.2.3 and < V18.1 Opcenter Intelligence — Versions affected: >= V3.2 only OEM version that ships Tableau
Opcenter Intelligence — Versions affected: >= V3.2 only OEM version that ships Tableau Operation Scheduler — Versions affected: >= V1.1.3
Operation Scheduler — Versions affected: >= V1.1.3 SENTRON powermanager V4 — Versions affected: V4.1, V4.2
SENTRON powermanager V4 — Versions affected: V4.1, V4.2 SIGUARD DSA — Versions affected: V4.2, 4.3, 4.4
SIGUARD DSA — Versions affected: V4.2, 4.3, 4.4 Simcenter 3D — Versions affected: <= V022.1
Simcenter 3D — Versions affected: <= V022.1 SiPass integrated V2.80 — Versions affected: All Versions
SiPass integrated V2.80 — Versions affected: All Versions SiPass integrated V2.85 — Versions affected: All Versions
SiPass integrated V2.85 — Versions affected: All Versions Siveillance Command — Versions affected: >= 4.16.2.1
Siveillance Command — Versions affected: >= 4.16.2.1 Siveillance Control Pro — Versions affected: All Versions
Siveillance Control Pro — Versions affected: All Versions Siveillance Identity V1.5 — Versions affected: All Versions
Siveillance Identity V1.5 — Versions affected: All Versions Siveillance Identity V1.6 — Versions affected: All Versions
Siveillance Identity V1.6 — Versions affected: All Versions Solid Edge CAM Pro — Versions affected: All Versions delivered with Solid Edge SE 2020 or later version
Solid Edge CAM Pro — Versions affected: All Versions delivered with Solid Edge SE 2020 or later version Solid Edge Harness Design — Versions affected: >= 2020 SP2002 only if Teamcenter integration feature is used
Solid Edge Harness Design — Versions affected: >= 2020 SP2002 only if Teamcenter integration feature is used Spectrum Power 4 — Versions affected: >= V4.70 SP8
Spectrum Power 4 — Versions affected: >= V4.70 SP8 Spectrum Power 7 — Versions affected: >= V2.30 SP2
Spectrum Power 7 — Versions affected: >= V2.30 SP2 Teamcenter — Versions affected: >= V13.1
Teamcenter — Versions affected: >= V13.1 Teamcenter Active Workspace — Versions affected: >= V4.3
Teamcenter Active Workspace — Versions affected: >= V4.3 Teamcenter Briefcase Browser — Versions affected: >= V13.1
Teamcenter Briefcase Browser — Versions affected: >= V13.1 Teamcenter Data Share Manager — Versions affected: >= V13.1
Teamcenter Data Share Manager — Versions affected: >= V13.1 Teamcenter Deployment Center — Versions affected: >= V13.1
Teamcenter Deployment Center — Versions affected: >= V13.1 Teamcenter Dispatcher Service — Versions affected: >= V13.1
Teamcenter Dispatcher Service — Versions affected: >= V13.1 Teamcenter EDA — Versions affected: >= V2.3
Teamcenter EDA — Versions affected: >= V2.3 Teamcenter FMS — Versions affected: >= V11.3
Teamcenter FMS — Versions affected: >= V11.3 Teamcenter Integration Framework — Versions affected: >= V13.2
Teamcenter Integration Framework — Versions affected: >= V13.2 Teamcenter MBSE Gateway — Versions affected: >= V4.0
Teamcenter MBSE Gateway — Versions affected: >= V4.0 Teamcenter Mendix Connector — Versions affected: V1.0
Teamcenter Mendix Connector — Versions affected: V1.0 Teamcenter Microservices Framework — Versions affected: >= V5.1
Teamcenter Microservices Framework — Versions affected: >= V5.1 Teamcenter Polarion Integration — Versions affected: >= V5.1
Teamcenter Polarion Integration — Versions affected: >= V5.1 Teamcenter Rapid Start — Versions affected: >= V13.1
Teamcenter Rapid Start — Versions affected: >= V13.1 Teamcenter Reporting and Analytics — Versions affected: All Versions based on Java SOA client >= V11.3
Teamcenter Reporting and Analytics — Versions affected: All Versions based on Java SOA client >= V11.3 Teamcenter Requirements Integrator — Versions affected: All Versions based on Java SOA client >= V11.3
Teamcenter Requirements Integrator — Versions affected: All Versions based on Java SOA client >= V11.3 Teamcenter Retail Footwear and Apparel — Versions affected: >= V4.3
Teamcenter Retail Footwear and Apparel — Versions affected: >= V4.3 Teamcenter Security Services — Versions affected: >= V11.3
Teamcenter Security Services — Versions affected: >= V11.3 Teamcenter Supplier Collaboration — Versions affected: >= V5.1
Teamcenter Supplier Collaboration — Versions affected: >= V5.1 Teamcenter System Modeling Workbench — Versions affected: All Versions based on Java SOA client >= V11.3
Teamcenter System Modeling Workbench — Versions affected: All Versions based on Java SOA client >= V11.3 Teamcenter Technical Publishing — Versions affected: >= V2.10
Teamcenter Technical Publishing — Versions affected: >= V2.10 Xpedition Enterprise — Versions affected: >= VX.2.6
Xpedition Enterprise — Versions affected: >= VX.2.6 Xpedition IC Packaging — Versions affected: >= VX.2.6
Xpedition IC Packaging — Versions affected: >= VX.2.6
SolarWinds #
 Database Performance Analyzer (DPA) — Versions affected: 2021.1.X, 2021.3.X, 2022.1.X
Database Performance Analyzer (DPA) — Versions affected: 2021.1.X, 2021.3.X, 2022.1.X Server & Application Monitor (SAM) — Versions affected: SAM 2020.2.6 and later
Server & Application Monitor (SAM) — Versions affected: SAM 2020.2.6 and later
Soliton Systems #
 MailZen Management Portal - On-Premise — Versions affected: 2.36.2, 2.37.3, 2.38.2
MailZen Management Portal - On-Premise — Versions affected: 2.36.2, 2.37.3, 2.38.2
SonicWall #
 Email Security — ES 10.0.11 and earlier versions are affected.
Email Security — ES 10.0.11 and earlier versions are affected. NSM — Affected.
NSM — Affected. WAF — Version 3.x with Cloud Management enabled is affected.
WAF — Version 3.x with Cloud Management enabled is affected.
Splunk #
 Add-On: Java Management Extensions — Versions 3.0.0 & 2.1.0 affected.
Add-On: Java Management Extensions — Versions 3.0.0 & 2.1.0 affected. Add-On: JBoss — Versions 3.0.0 & 2.1.0 affected.
Add-On: JBoss — Versions 3.0.0 & 2.1.0 affected. Data Stream Processor — DSP 1.0.x, DSP 1.1.x, DSP 1.2.x affected.
Data Stream Processor — DSP 1.0.x, DSP 1.1.x, DSP 1.2.x affected. IT Service Intelligence (ITSI) — Versions 4.11.x, 4.10.x, 4.9.x, 4.8.x, 4.7.x, & 4.4.x affected.
IT Service Intelligence (ITSI) — Versions 4.11.x, 4.10.x, 4.9.x, 4.8.x, 4.7.x, & 4.4.x affected. Stream Processor Service — Current version affected.
Stream Processor Service — Current version affected.
Stardog #
 Stardog — Versions affected: <7.8.1
Stardog — Versions affected: <7.8.1
Stratodesk #
 NoTouch — Versions affected: 4.5.231
NoTouch — Versions affected: 4.5.231
SwingSet #
 SwingSet — Versions affected: < 4.0.6
SwingSet — Versions affected: < 4.0.6
TeamViewer #
 TeamViewer Engage — Affected, low.
TeamViewer Engage — Affected, low. TeamViewer Frontline — Affected, low.
TeamViewer Frontline — Affected, low. TeamViewer IoT — Affected, low.
TeamViewer IoT — Affected, low.
Tesorion #
 SOC-appliances and software — Versions affected: all (unverified)
SOC-appliances and software — Versions affected: all (unverified)
Tibco #
 BusinessWorks 5 V.5.15 — Under investagation.
BusinessWorks 5 V.5.15 — Under investagation.
TP-Link #
Controllers
Hardware Controllers
Hardware Controllers
TrendMicro #
 Deep Discovery Director — Versions affected: <= 5.3, upgrade to 5.3 CPB1228 or 5.2 CPB1400
Deep Discovery Director — Versions affected: <= 5.3, upgrade to 5.3 CPB1228 or 5.2 CPB1400
Ubiquiti #
 UniFi Network Application — Versions affected: 6.5.53 & lower versions
UniFi Network Application — Versions affected: 6.5.53 & lower versions UniFi Network Controller — Versions affected: 6.5.54 & lower versions
UniFi Network Controller — Versions affected: 6.5.54 & lower versions
USoft #
 USoft — Versions affected: 9.1 (unverified)
USoft — Versions affected: 9.1 (unverified)
VMware #
The current list can be found in the advisory.
 API Portal for VMware Tanzu
API Portal for VMware Tanzu App Metrics
App Metrics Carbon Black Cloud Workload Appliance
Carbon Black Cloud Workload Appliance Carbon Black EDR Servers
Carbon Black EDR Servers Cloud Foundation
Cloud Foundation HCX
HCX Healthwatch for Tanzu Application Service
Healthwatch for Tanzu Application Service Horizon
Horizon Identity Manager
Identity Manager NSX-T Data Center
NSX-T Data Center Single Sign-On for VMware Tanzu Application Service
Single Sign-On for VMware Tanzu Application Service Site Recovery Manager
Site Recovery Manager Spring Cloud Gateway for Kubernetes
Spring Cloud Gateway for Kubernetes Spring Cloud Gateway for VMware Tanzu
Spring Cloud Gateway for VMware Tanzu Spring Cloud Services for VMware Tanzu
Spring Cloud Services for VMware Tanzu Tanzu Application Service for VMs
Tanzu Application Service for VMs Tanzu GemFire
Tanzu GemFire Tanzu Greenplum
Tanzu Greenplum Tanzu Kubernetes Grid Integrated Edition
Tanzu Kubernetes Grid Integrated Edition Tanzu Observability by Wavefront Nozzle
Tanzu Observability by Wavefront Nozzle Tanzu Operations Manager
Tanzu Operations Manager Tanzu SQL with MySQL for VMs
Tanzu SQL with MySQL for VMs Telco Cloud Automation
Telco Cloud Automation Unified Access Gateway
Unified Access Gateway vCenter Cloud Gateway
vCenter Cloud Gateway vCenter Server
vCenter Server vRealize Automation
vRealize Automation vRealize Lifecycle Manager
vRealize Lifecycle Manager vRealize Log Insight
vRealize Log Insight vRealize Operations
vRealize Operations vRealize Operations Cloud Proxy
vRealize Operations Cloud Proxy vRealize Orchestrator
vRealize Orchestrator WorkspaceOne Access
WorkspaceOne Access
WatchGuard #
 AuthPoint — Versions affected: Cloud
AuthPoint — Versions affected: Cloud
Wibu Systems #
 CodeMeter Cloud Light — Versions affected: <= 2.2
CodeMeter Cloud Light — Versions affected: <= 2.2 CodeMeter Keyring for TIA Portal — Versions affected: <= 1.30
CodeMeter Keyring for TIA Portal — Versions affected: <= 1.30
WitFoo #
 WitFoo Precinct — Versions affected: 6.x
WitFoo Precinct — Versions affected: 6.x
Zeiss #
 Advanced Data Export — Versions affected: 1.X
Advanced Data Export — Versions affected: 1.X Cataract Suite — Versions affected: 1.3.1
Cataract Suite — Versions affected: 1.3.1 EQ Workplace — Versions affected: 1.6 - 1.8
EQ Workplace — Versions affected: 1.6 - 1.8 FORUM — Versions affected: 4.2.X
FORUM — Versions affected: 4.2.X Glaucoma Workplace — Versions affected: 3.5.X
Glaucoma Workplace — Versions affected: 3.5.X Laser Treatment Workplace — Versions affected: 1.X
Laser Treatment Workplace — Versions affected: 1.X Retina Workplace — Versions affected: 2.5.X and 2.6.X
Retina Workplace — Versions affected: 2.5.X and 2.6.X
Zendesk #
 All Products — Versions affected: All Versions
All Products — Versions affected: All Versions
Other #
 3ds — Some instances of log4j in Catia v6 R2020x.
3ds — Some instances of log4j in Catia v6 R2020x. Apereo CAS
Apereo CAS Apple XCode
Apple XCode Aruba Networks — Affects Silver Peak Orchestrator in some configurations.
Aruba Networks — Affects Silver Peak Orchestrator in some configurations. Avantra — Syslink
Avantra — Syslink Avaya — Still investigating.
Avaya — Still investigating. Azure Data Lake Store — Client.
Azure Data Lake Store — Client. Backbox — Affected versions 6.50 up to 6.53.x.
Backbox — Affected versions 6.50 up to 6.53.x. Blackberry — May be affected. No list 12/20
Blackberry — May be affected. No list 12/20 BMC Software — Still investigating.
BMC Software — Still investigating. Citrix Endpoint Management / XenMobile Server — Affected. Update to version 10.14 RP2, 10.13 RP5, or 10.12 RP10.
Citrix Endpoint Management / XenMobile Server — Affected. Update to version 10.14 RP2, 10.13 RP5, or 10.12 RP10. Citrix XenApp / XenDesktop — Linux Virtual Delivery Agent affected, update to version 2112. Not affected: Linux VDA LTSR (all versions) and All other CVAD components.
Citrix XenApp / XenDesktop — Linux Virtual Delivery Agent affected, update to version 2112. Not affected: Linux VDA LTSR (all versions) and All other CVAD components. Code42
Code42 Connect2id — Server.
Connect2id — Server. Contrast Security — Versions affected: All
Contrast Security — Versions affected: All Couchbase — Elasticsearch Connector and Server Enterprise.
Couchbase — Elasticsearch Connector and Server Enterprise. Cpanel — via Solr plugin.
Cpanel — via Solr plugin. Datadog — Agent and seveal components affected.
Datadog — Agent and seveal components affected. Dynatrace Synthetic Chromium — Affected versions: update to 1.229.49.20211210-165018, 1.227.31.20211210-164955, 1.225.29.20211210-164930, 1.223.30.20211210-164926
Dynatrace Synthetic Chromium — Affected versions: update to 1.229.49.20211210-165018, 1.227.31.20211210-164955, 1.225.29.20211210-164930, 1.223.30.20211210-164926 ESRI ArcGIS
ESRI ArcGIS Forcepoint — Security Manager & DLP Manager
Forcepoint — Security Manager & DLP Manager Ghidra — Versions affected: < 10.1
Ghidra — Versions affected: < 10.1 GoAnywhere — GoAnywhere MFT version 5.7.0 or later, GoAnywhere Gateway version 2.7.0 or later, GoAnywhere MFT Agents 1.4.2 or later
GoAnywhere — GoAnywhere MFT version 5.7.0 or later, GoAnywhere Gateway version 2.7.0 or later, GoAnywhere MFT Agents 1.4.2 or later Grails
Grails Graylog — Versions affected: >= 1.2.0 and <= 4.2.2
Graylog — Versions affected: >= 1.2.0 and <= 4.2.2 Guidewire
Guidewire IBM QRadar — May be vulnerable.
IBM QRadar — May be vulnerable. IFS — Still investigating.
IFS — Still investigating. iManage — Work Indexer, Records Manager, Security Policy Manager, Threat Manager
iManage — Work Indexer, Records Manager, Security Policy Manager, Threat Manager Informatica — Still investigating.
Informatica — Still investigating. InterSystems — Still investigating.
InterSystems — Still investigating. JAMF Pro — Versions affected: 10.31.0 - 10.34.1
JAMF Pro — Versions affected: 10.31.0 - 10.34.1 JetBrains — License Server.
JetBrains — License Server. JGAAP
JGAAP Jitsi — Video bridge.
Jitsi — Video bridge. Jitterbit — Jitterbit Harmony Private Agent: Partially affected.
Jitterbit — Jitterbit Harmony Private Agent: Partially affected. Kafka Connect CosmosDB
Kafka Connect CosmosDB Kaseya — Still investigating.
Kaseya — Still investigating. LogRhythm
LogRhythm LucentSky — Self-hosted.
LucentSky — Self-hosted. Mailcow — Affected versions: < 1.8
Mailcow — Affected versions: < 1.8 McAfee — Still investigating.
McAfee — Still investigating. Metabase
Metabase Minecraft
Minecraft MongoDB — Atlas Search vulnerable, patched as of December 12, 6pm ET.
MongoDB — Atlas Search vulnerable, patched as of December 12, 6pm ET. N-Able Risk Intelligence
N-Able Risk Intelligence Nelson
Nelson Neo4J — Versions affected: 4.2+
Neo4J — Versions affected: 4.2+ Netgear — Believed not affected, but still investigating.
Netgear — Believed not affected, but still investigating. Openfire
Openfire OpenHab
OpenHab OpenMRS
OpenMRS OpenNMS
OpenNMS OpenSearch
OpenSearch PagerDuty Rundeck — Affeced, upgrade to v3.4.9/v3.3.17
PagerDuty Rundeck — Affeced, upgrade to v3.4.9/v3.3.17 PaperCut MF and NG — Versions affected: 21.0 and later
PaperCut MF and NG — Versions affected: 21.0 and later Pegasystems — Self-hosted.
Pegasystems — Self-hosted. PowerSchool
PowerSchool Progress — Open Edge & DataDirect Hybrid Data Pipeline.
Progress — Open Edge & DataDirect Hybrid Data Pipeline. Puppet — Continuous Delivery for Puppet Enterprise.
Puppet — Continuous Delivery for Puppet Enterprise. Radware
Radware Red Hat — is reporting affected packages
Red Hat — is reporting affected packages Rosette — RNI Web Services.
Rosette — RNI Web Services. RSA SecureID Authentication Manager
RSA SecureID Authentication Manager SAP
SAP SAS — Profile and possibly other products.
SAS — Profile and possibly other products. SDL — WorldServer.
SDL — WorldServer. SecurityOnion — Versions affected: 2.3.90 20211210
SecurityOnion — Versions affected: 2.3.90 20211210 Sentry — Through optional plugin.
Sentry — Through optional plugin. ServiceNow — MID Servers & self-hosted.
ServiceNow — MID Servers & self-hosted. Signald
Signald Software AG — ARIS, Cumulocity, webMethods
Software AG — ARIS, Cumulocity, webMethods Sophos Mobile EAS Proxy — Versions affected: < 9.7.2
Sophos Mobile EAS Proxy — Versions affected: < 9.7.2 Splunk
Splunk Spring Boot — if log4j was configured.
Spring Boot — if log4j was configured. Sumo Logic — Collector Java agent affected. The current search link here will surface Sumo Logic servers in your organization, which themselves are not vulnerable, but presnece of the server could indicate existance of collectors in your organization.
Sumo Logic — Collector Java agent affected. The current search link here will surface Sumo Logic servers in your organization, which themselves are not vulnerable, but presnece of the server could indicate existance of collectors in your organization. SwingSet
SwingSet SysAid — Remote Discovery Server.
SysAid — Remote Discovery Server. SysAid Remote Discovery Server
SysAid Remote Discovery Server Tableau
Tableau Talend Component Kit
Talend Component Kit Varonis
Varonis Wowza Streaming Engine
Wowza Streaming Engine WSO2
WSO2 ZAP Proxy
ZAP Proxy Zenoss — Zenoss Resource Manager version > 6.5
Zenoss — Zenoss Resource Manager version > 6.5 Zerto — Not affected.
Zerto — Not affected. Zimbra — Not affected.
Zimbra — Not affected. Zoom — Under investigation for their own infrastructure
Zoom — Under investigation for their own infrastructure
Potentially affected products #
- Blackberry may be affected.
- Citrix is still investigating many products.
- Dell is still investigating.
- Huawei is still investigating.
- Kaseya is still investigating.
- Oracle currently requires a support account to see affected products.
- TrendMicro is still investigating.