Each year, August arrives with promises of hot weather and cool security research talks. The DEF CON, Black Hat, and BSidesLV security conferences bring people in from all over the world to share knowledge through conversations, villages, training, and talks. There are always a number of interesting talks, and one that caught our eye was from this year's Black Hat "briefings." It covered vulnerabilities in the HPE iLO 5 firmware discovered by researchers Alexandre Gazet (Senior Security Engineer, Airbus), Fabien Périgaud (Reverse Engineering Team Tech Lead, Synacktiv), and Joffrey Czarny (Red Team Lead, Medallia).
Bypassing encryption to improve iLO security #
HPE's Integrated Lights-Out (iLO) logic is available in many of HPE's server lines, including ProLiant and Gen10 series. Similar to other "lights out" management solutions such as Dell's iDRAC and Supermicro's IPMI boards, iLO supports out-of-band remote management of the servers where it is embedded.
Last year, these security researchers noticed that HPE had begun encrypting the iLO firmware blobs and decided to analyze the new encryption mechanism, with an eye toward surfacing security implications around this new encrypted packaging. Their talk at Black Hat, titled "HPE iLO5 Firmware Security - Go Home Cryptoprocessor, You're Drunk!", digs into their research methods and the vulnerabilities they discovered with iLO. It included a buffer overflow (CVE-2021-29202) that can be locally exploited to allow a privileged user of the system OS to execute code as a privileged user on the iLO itself.
In addition to these researchers' findings, a number of other iLO 5 vulnerabilities had been reported to HPE, including XSS and CRLF injection, affecting multiple versions of iLO 5 firmware on HPE servers that include iLO logic. Ultimately, leading HPE to publish a security bulletin and a new iLO firmware version: 2.44.
How to find vulnerable iLO BMCs with Rumble #
While remaining true to our "unauthenticated scanning" mantra, runZero Explorers and scanners take additional steps when querying iLO assets to provide a rich set of details. Rumble provides a holistic view of each iLO asset–all without authentication–by making pre-auth queries of iLO REST endpoints that return XML-formatted details, and then combining that data with information gleaned from initiating a web login session.
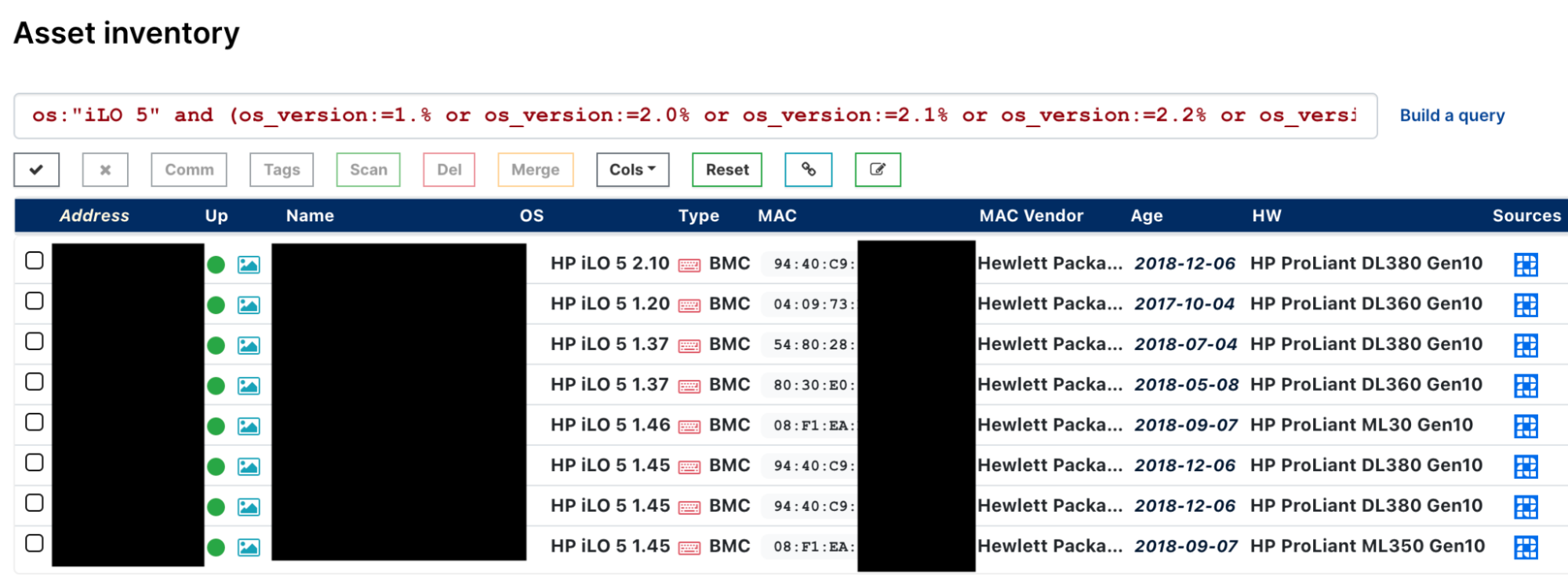
You can locate iLO 5 assets in your inventory currently running vulnerable versions of iLO firmware with this pre-built query:
os:"iLO 5" and (os_version:=1.% or os_version:=2.0% or os_version:=2.1% or os_version:=2.2% or os_version:=2.3% or os_version:=2.40 or os_version:=2.41 or os_version:=2.42 or os_version:=2.43)
As always, any prebuilt queries we create are available from our Queries Library.
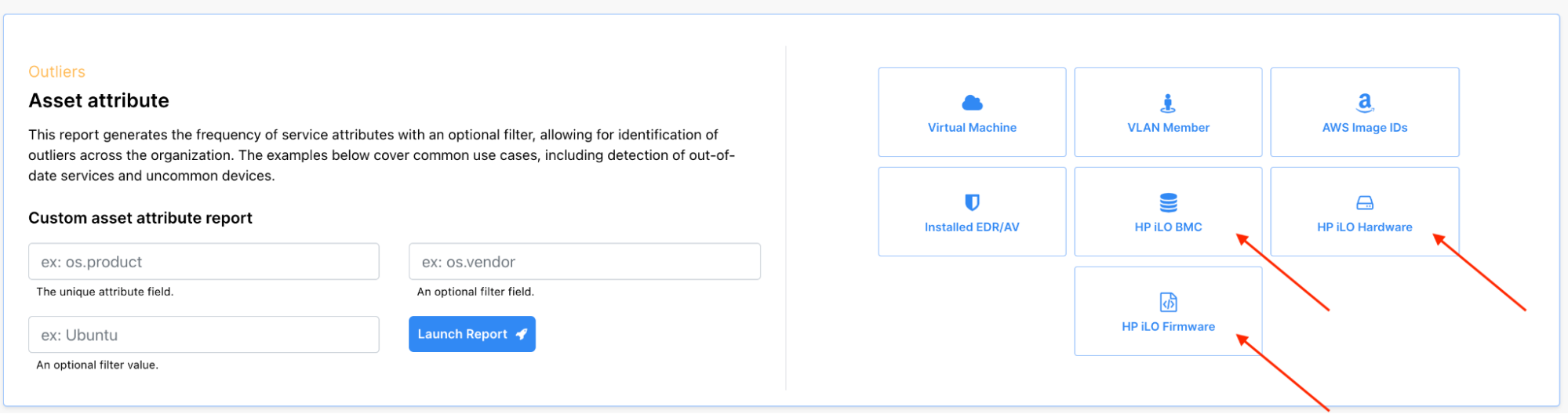
Additional iLO details can be found on a per-asset view via "ilo" attributes and also using your Reports page, including what kind of iLO assets are present in your environment, the server assets they are a part of, and all the versions of firmware running on those iLO assets:
There is also a specially-crafted CSV export available for iLO devices from your Inventory page, containing many details which are suitable for warranty tracking:
Additional details you'll find in this CSV export of your iLO assets include:
- The configured Insight Remote Support server
- The health status of the module
- All active MAC addresses
- Authentication methods
You can also broaden your search to find ALL of your lights-out assets in your inventory via this query:
type:bmc
Shine a light on your lights-out assets #
Use the Rumble resources we covered in this post to get faster visibility of your iLO assets and their current state. At Rumble, our goal is to build the best products for IT and security professionals through applied research. We hope that you found this post interesting and that you will try it out.