Latest Fortinet WAF vulnerability #
Recently published security research from Rapid7 provides details on an OS command injection vulnerability in Fortinet's web application firewall (WAF) product line known as FortiWeb. This vulnerability exists in the FortiWeb management interface (versions 6.3.11 and prior) and has a CVSSv3 base score of 8.7 (currently awaiting CVE assignment). While authentication is required for successful exploitation of this vulnerability, Rapid7 researchers point out that chaining this with exploitation of an existing authentication bypass vulnerability could be a successful attack vector against vulnerable FortiWeb targets.
Fortinet is tracking this issue as FG-IR-21-116 (with a fix in the upcoming FortiWeb 6.4.1 release) and advising current FortiWeb owners with a workaround until the patch is available.
How to find Fortinet web application firewall devices with Rumble #
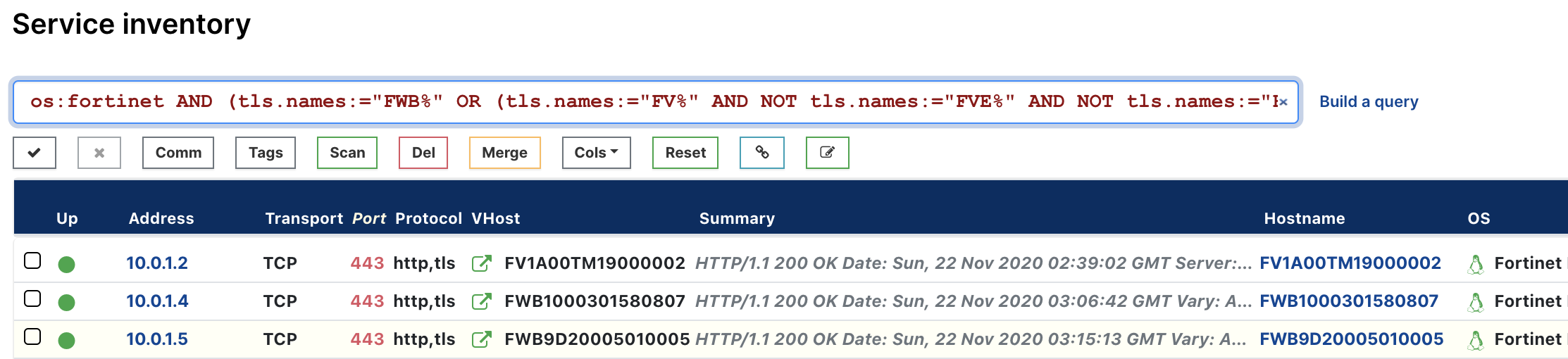
From the Services inventory, use the following pre-built query to locate FortiWeb assets in your network:
os:fortinet AND (tls.names:="FWB%" OR (tls.names:="FV%" AND NOT tls.names:="FVE%" AND NOT tls.names:="FVC%"))
As always, any prebuilt queries we create are available from our Queries Library. Check out the library for other useful inventory queries.