What is Fortinet SSL-VPN? #
Fortinet SSL-VPN is a VPN capability offered in some Fortinet products, including FortiGate firewall devices. This service provides secured network communications between a remote client and protected devices on an internal network. Several modes of operation are supported, including "tunnel mode" (which requires use of the FortiClient VPN client) and "web mode" (which does not require client-side VPN software).
Latest Fortinet SSL-VPN vulnerability #
Fortinet warned customers this week of potential limited exploitation in the wild regarding a flaw affecting the SSL-VPN software component. This critical vulnerability (tracked as CVE-2023-27997) can be remotely exploited without authentication and can yield remote code or command execution to an attacker. Discovered by researchers Charles Fol and Dany Bach at LEXFO, disclosure-and-fix of this vulnerability coincided with an internal SSL-VPN audit-and-fix effort at Fortinet which covered this and five additional vulnerabilities.
What is the impact? #
Of the six disclosed vulnerabilities, CVE-2023-27997 is considered the most severe with a "critical" CVSS score of 9.2. This pre-authentication vulnerability is rooted in a heap-based buffer overflow, seemingly similar to CVE-2022-42475 which was disclosed earlier this year as also affecting SSL-VPN (and did have reported exploitation in the wild). Attackers can exploit this vulnerability via a specially crafted request.
The complete list of recently disclosed-and-fixed Fortinet SSL-VPN vulnerabilities is as follows:
- CVE-2023-27997 (9.2, "critical) - pre-auth heap buffer overflow in SSL-VPN, exploitation could yield code/command execution
- CVE-2023-29180 (7.3, "high") - null pointer dereference in SSLVPNd, exploitation could cause a denial-of-service condition by crashing SSLVPNd
- CVE-2023-22640 (7.1, "high") - out-of-bounds write in SSLVPNd, exploitation could yield code/command execution
- CVE-2023-29181 (8.3, "high") - format string bug in Fclicense daemon, exploitation could yield code/command execution
- CVE-2023-29179 (6.4, "medium") - null pointer dereference in the SSLVPNd proxy endpoint, exploitation could cause a denial-of-service condition by crashing SSLVPNd
- CVE-2023-22641 (4.1, "medium") - open redirect in SSLVPNd, exploitation could allow an attacker to redirect a user's browser to a malicious URL
Are updates available? #
Fortinet published new firmware versions a few days ahead of this disclosure. A variety of FortiOS, FortiOS-6K7K, and FortiProxy versions have been patched to fix the recently disclosed CVEs affecting SSL-VPN: CVE-2023-27997, CVE-2023-29180, CVE-2023-22640, CVE-2023-29181, CVE-2023-29179, CVE-2023-22641. Admins or owners of Fortinet appliances/products running affected firmware with SSL-VPN enabled should ensure they are updated to one of the newer firmware versions. If updating is not a near-term option, disabling the SSL-VPN service on affected appliances can mitigate the risk of exploitation.
How do I find potentially vulnerable Fortinet SSL-VPN instances with runZero? #
From the Services inventory, use the following prebuilt query to locate Fortinet SSL-VPN instances in your network:
_asset.protocol:http AND protocol:http AND (http.head.setCookie:="SVPNCOOKIE%SVPNNETWORKCOOKIE%" OR last.http.head.setCookie:="SVPNCOOKIE%SVPNNETWORKCOOKIE%")
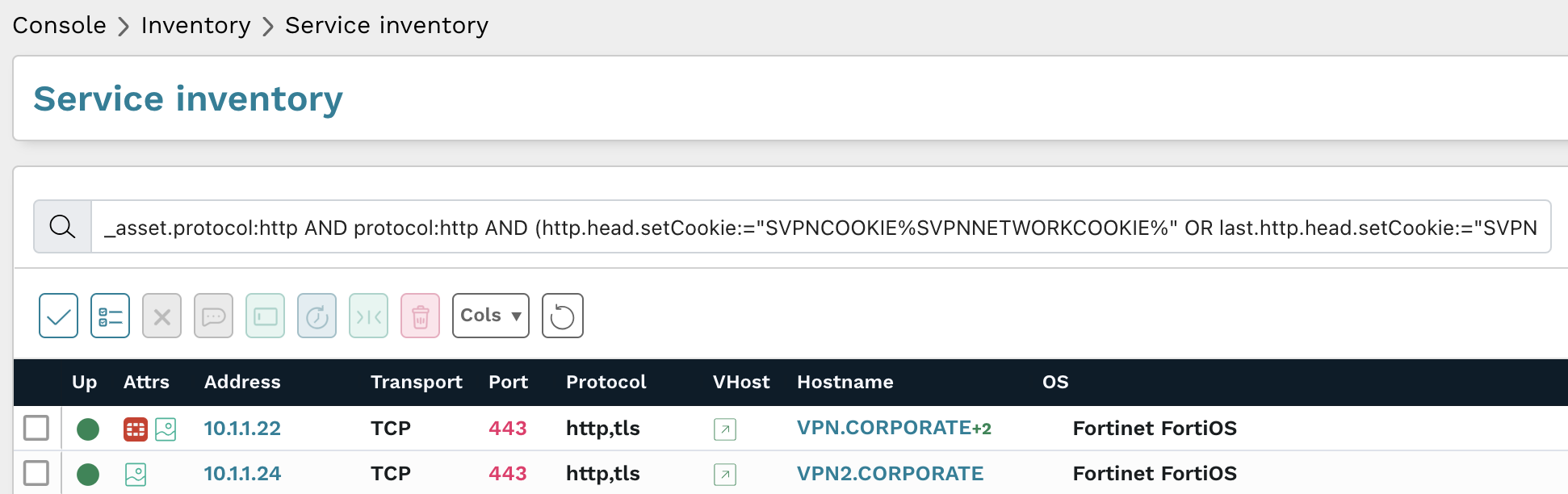
Results from the above query should be triaged to verify those assets are running updated firmware versions.
As always, any prebuilt queries are available from your runZero console. Check out the documentation for other useful inventory queries.