At the most basic level, Rumble is a search engine for your network; it sends out probes, listens for replies, normalizes the results, applies fingerprints, and makes this data easy to query. Similar to web crawlers, Rumble will follow links between assets, this includes HTTP redirects, but also things like SunRPC portmappers, UPnP SSDP endpoints, and other services that point the way to additional data.
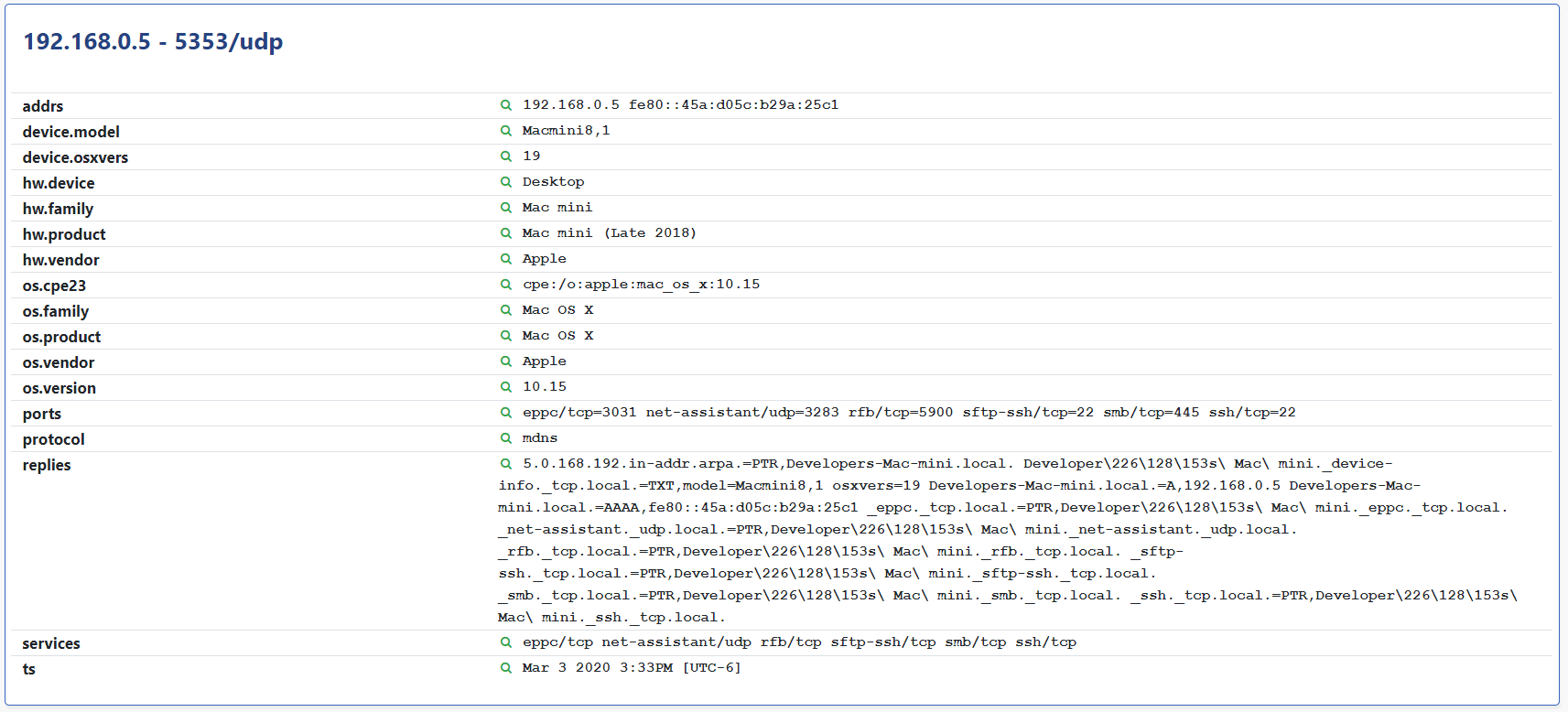
mDNS (also known as ZeroConf or Bonjour) is one of these services. mDNS provides a list of other reachable applications and services along with tons of metadata, especially on macOS systems. This metadata is how Rumble identifies the exact macOS hardware and software versions without credentials, but it can expose quite a bit more.
Last December we ran across an oddity in mDNS that was too useful to pass up. It appeared that an application on macOS was registering something called ptService in the mDNS service table that included the logged-in username of the operator in the response. The reply almost always ended with the string com.cisco.ptService and had the following form:
thismac.local.thisusername.com.cisco.ptService._ptService._tcp.local.
Our immediate response was to extract the username component and report this as a new asset-level attribute within the platform. How awesome would it be to find the laptop and IP address associated with a given user through a Rumble query? We thought it was awesome, but one of our customers pointed out that this might have security implications, and that they would prefer that their macOS systems not leak their active directory usernames on every network they join.
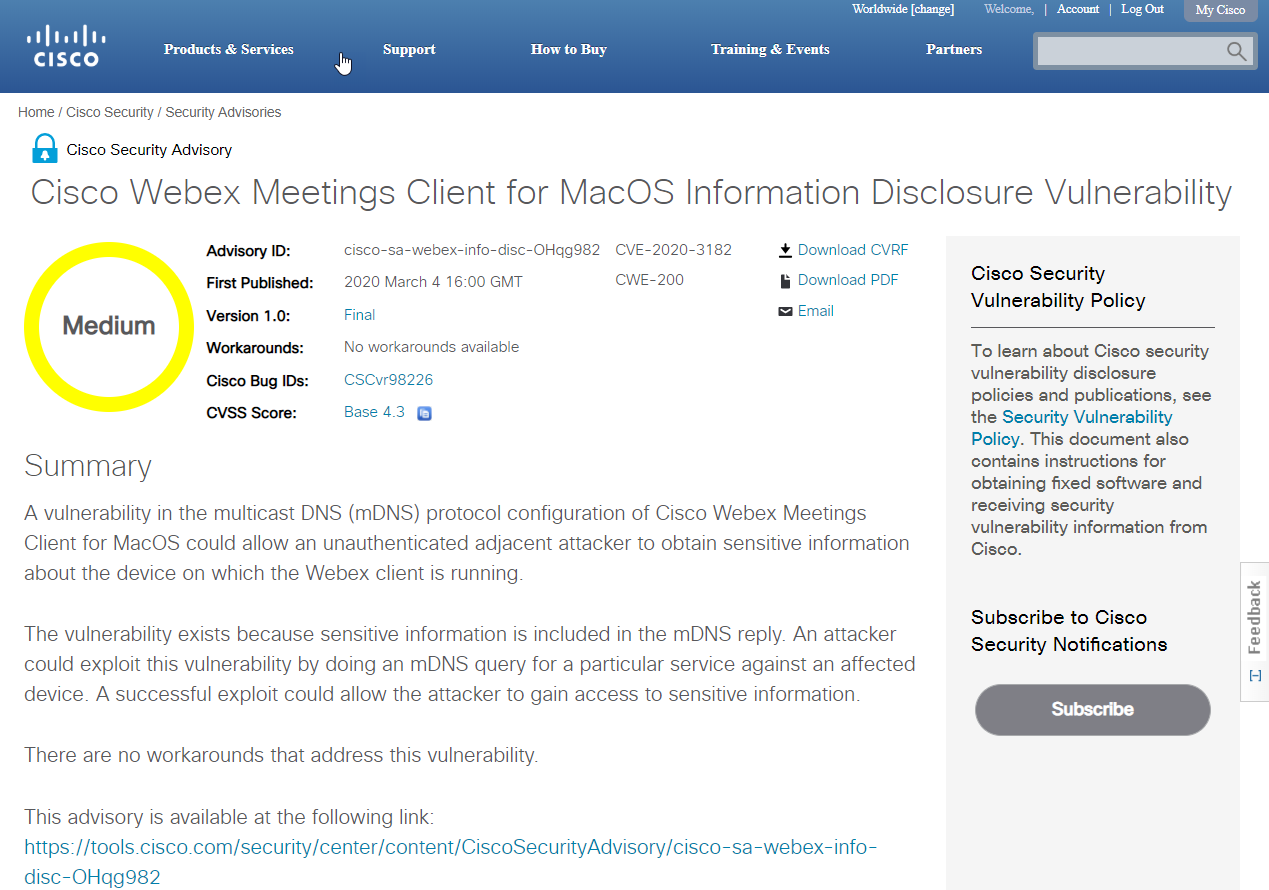
Fair point. We reached out to the folks at Cisco PSIRT to report this issue and coordinate a public response. As of yesterday, this issue now public, and assigned CVE-2020-3182, as well as Cisco Bug ID CSCvr98226. This issue affects the Cisco Webex Meetings Client for macOS and applies to versions up to and including 40.1.8.5.
One caveat is that the mDNS query in question only works on the same broadcast domain as the macOS systems. This applies generally to mDNS on macOS; newer versions of the operating system only respond to local multicast queries. If you have a Rumble Agent on the same broadcast domain as your macOS systems, there is a good chance this will turn up if you use Cisco Webex. To query for this issue, run a Services search for port:5353 AND services:"ptService/tcp".
Big thanks to Bryan and Marcus for helping us identify this issue and being a good sport about us turning a vulnerability into a product feature (at least temporarily).
Happy Scanning!
-HD