One of the trickiest parts of network discovery is balancing thoroughness with speed. We strive to provide a fast, low-impact scan by default, but also try to include as many services and protocols as possible.
Today we released version 0.7.5 of the Rumble Agent and runZero Scanner. This version increases the default port coverage from 100 TCP ports to more than 400, while also supporting discovery and fingerprinting of
additional TCP services by leveraging UDP discovery protocols.
Automatically scanning and fingerprinting TCP services #
Rumble will now automatically scan and fingerprint TCP services identified through multicast ZeroConf (mDNS) SRV records, advertised via UPnP SSDP locations, returned in Microsoft SQL Server discovery responses, enumerated via SunRPC portmapper responses, included in WSD probe replies, and identified via HTTP redirects. Combined, these discovery methods substantially improve TCP service coverage without a major impact on scan durations.
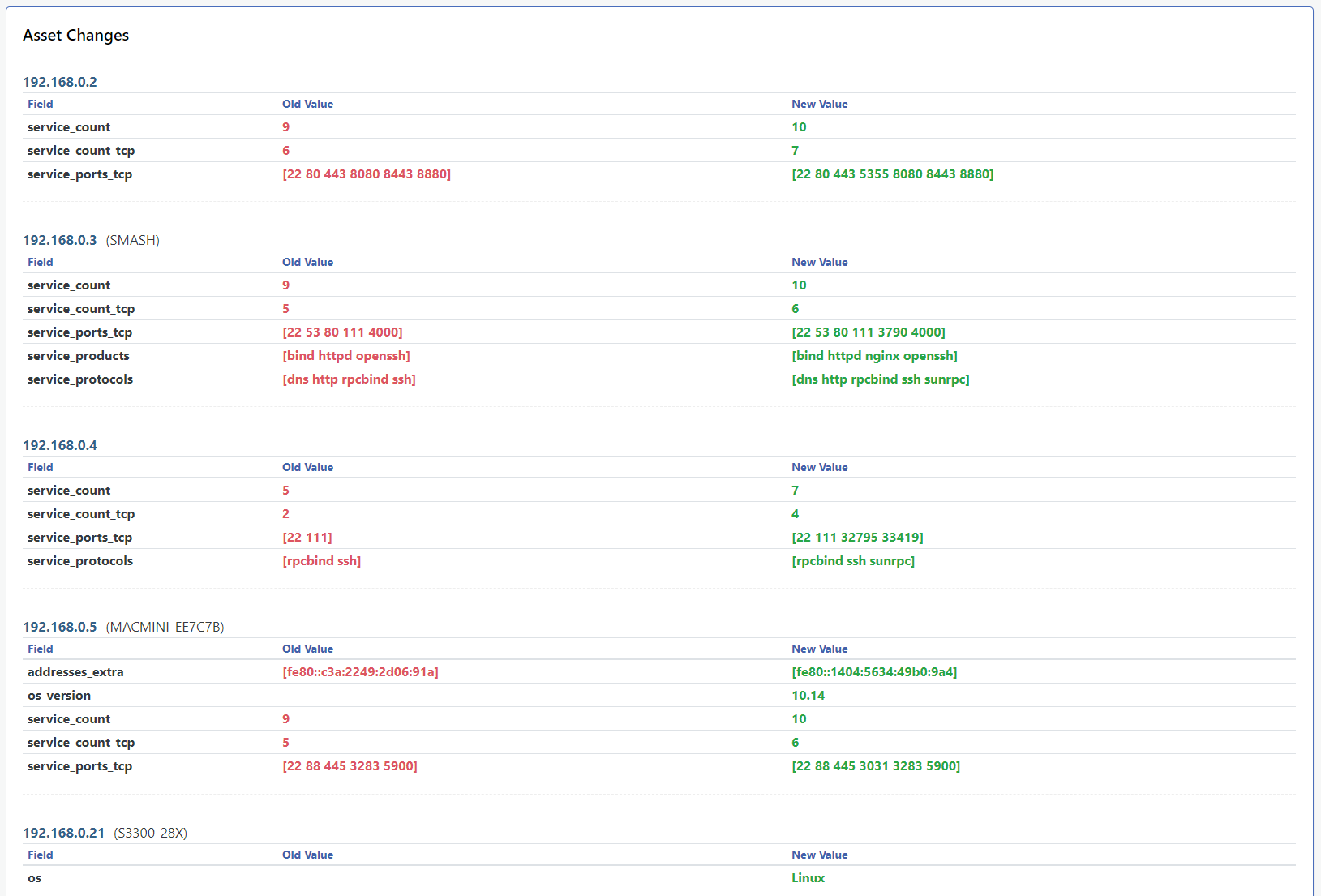
Multicast ZeroConf discovery is now used to identify Apple macOS version and hardware model information, along with a ton of useful information from ZeroConf-enabled network devices.
In addition to increased port coverage and UDP-based TCP discovery, the default scan parameters have been slightly tweaked to improve performance while also increasing scan reliability of low-power devices. The default
Scan Rate has been increased from 500 to 1000 while the Max Host Rate dropped from 50 to 40.
As part of the UPnP SSDP changes, the UPnP device description (XML) is also automatically retrieved and recorded.
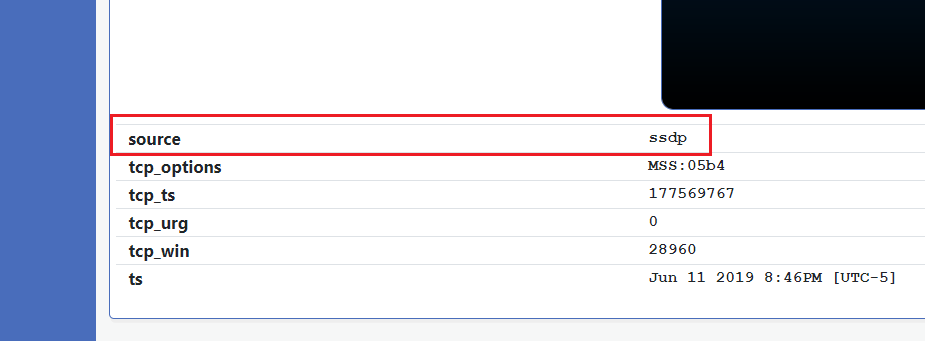
Update: Version 0.7.6 of the Rumble Agent and runZero Scanner will also track how the TCP service was discovered. An example of a TCP service found via SSDP is shown below.
Going forward we plan to leverage cross-service discovery whenever possible while also aiming to keep scan speeds consistent with their current levels. Candidates for future cross-service discovery include the Netstat daemon, SNMP v1/v2c, and the Microsoft RPC Endpoint Mapper. Existing recurring scans will continue to use the old port settings, but as of Beta 4, can be updated via the Modify action on the Tasks screen.
To update an existing scan to match the new defaults, set the Scan Rate to 1000, the Max Host Rate to 40, and the TCP Ports to following list:
1,7,9,13,19,21,22,23,25,37,42,49,53,69,79,80,81,82,83,84,85,88,102,105,109,110,111,113,123,135,137,139,143,161,179,222,264,384,389,402,407,443,445,465,500,502,512,513,515,523,524,540,548,554,587,617,623,631,636,689,705,771,783,873,888,902,910,912,921,993,995,998,1000,1024,1030,1035,1080,1089,1090,1091,1098,1099,1100,1101,1102,1103,1128,1129,1158,1199,1211,1220,1234,1241,1300,1311,1352,1433,1440,1494,1521,1530,1533,1581,1582,1583,1604,1720,1723,1755,1811,1883,1900,2000,2049,2082,2083,2100,2103,2121,2181,2199,2207,2222,2323,2362,2375,2379,2380,2381,2525,2533,2598,2601,2604,2638,2809,2947,2967,3000,3037,3050,3057,3128,3200,3217,3273,3299,3306,3311,3312,3351,3389,3460,3500,3628,3632,3690,3780,3790,3817,4000,4322,4433,4443,4444,4445,4567,4659,4679,4730,4840,4848,5000,5038,5040,5051,5060,5061,5093,5168,5222,5247,5250,5351,5353,5355,5400,5405,5432,5433,5498,5520,5521,5554,5555,5560,5580,5601,5631,5632,5666,5672,5683,5800,5814,5900,5920,5938,5984,5985,6000,6001,6002,6050,6060,6070,6080,6082,6101,6106,6112,6262,6379,6405,6502,6503,6504,6542,6660,6661,6667,6905,6988,7001,7021,7071,7077,7080,7144,7181,7210,7443,7474,7510,7547,7579,7580,7700,7770,7777,7778,7787,7800,7801,7879,7902,8000,8008,8014,8020,8023,8028,8030,8080,8081,8087,8088,8089,8090,8095,8098,8161,8180,8205,8222,8300,8303,8333,8400,8443,8471,8503,8545,8686,8800,8812,8834,8880,8883,8888,8899,8901,8902,8903,9000,9002,9042,9060,9080,9081,9084,9090,9092,9099,9100,9111,9152,9160,9200,9300,9390,9391,9418,9443,9471,9495,9809,9855,9999,10000,10008,10050,10051,10080,10098,10162,10202,10203,10443,10616,10628,11000,11099,11211,11234,11333,12174,12203,12221,12345,12397,12401,13364,13500,13838,14330,15200,15672,16102,17185,17200,18881,19300,19810,19888,20000,20010,20031,20034,20101,20111,20171,20222,22222,23472,23791,23943,25000,25025,26000,26122,27000,27017,27019,27080,27888,28017,28222,28784,30000,30718,31001,31099,32764,32913,34205,34443,34962,34963,34964,37718,37777,38080,38292,40007,41025,41080,41523,41524,44334,44818,45230,46823,46824,47001,47002,48899,49152,50000,50013,50070,50090,52302,55553,57772,61616,62078,62514,65535















