Latest AMI MegaRAC BMC vulnerabilities #
AMI has disclosed a vulnerability in its MegaRAC SPx Baseboard Management Controller (BMC). BMCs provide capabilities for remotely managing and monitoring servers. This vulnerability is considered highly critical with a CVSS score of 10.0. This exploit could allow a remote attacker to bypass authentication and take complete control of the vulnerable system. This issue was discovered and reported by Eclypsium Research, and is assigned CVE-2024-54085.
Update: On June 25th, 2025 CISA added the vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog. There is evidence that this vulnerability is being actively exploited in the wild.
What is the impact? #
A remote attacker capable of exploiting this vulnerability would be able to take complete control of the vulnerable system, potentially including the hosted operating system.
Are updates or workarounds available? #
AMI has released updates to the vulnerable software; additionally users are strongly advised to implement network access control to limit access to BMC interfaces to trusted networks only.
How to find potentially vulnerable systems with runZero #
From the Asset Inventory, use the following query to locate systems running potentially vulnerable software:
hw:="AMI MegaRAC"
July 2023: CVE-2023-34329, CVE-2023-34330 #
This week, Eclypsium Research published findings on critical vulnerabilities discovered in AMI MegaRAC baseboard management controller (BMC) firmware. Adding to the portfolio of "BMC&C" vulnerabilities that Eclypsium has been discovering and surfacing since late 2022, these two new vulnerabilities (tracked as CVE-2023-34329 and CVE-2023-34330) can be exploited and chained together to yield unauthenticated remote code execution on vulnerable targets. These vulnerabilities could impact many devices, as MegaRAC BMCs are popular across a number of manufacturers and appear in products from AMD, Asus, Dell EMC, Gigabyte, HPE, Lenovo, Nvidia, and more.
What was the impact? #
These two newly disclosed vulnerabilities involve the Redfish service running on the MegaRAC:
- Authentication Bypass via HTTP Header Spoofing (CVE-2023-34329; CVSS score 9.1 - "critical")
- Code injection via Dynamic Redfish Extension (CVE-2023-34330; CVSS score 8.2 - "high")
CVE-2023-34329 can be exploited with specially crafted HTTP headers to trick the Redfish service into believing the request is coming from an interface that does not require authentication, such as USB0. On systems which have the No Auth option enabled, these spoofed headers will allow attackers to access and interact with any Redfish API endpoints.
CVE-2023-34330 can be exploited via an HTTP POST action to execute arbitrary code on the MegaRAC processor. While this code-execution-via-POST was an intentional design choice by AMI, it likely was intended for internal development only. However, it is enabled by default in vulnerable versions of the firmware, making it available to a broader audience.
Chaining exploitation of the two above vulnerabilities together can provide attackers with unauthenticated remote code execution and full control over a vulnerable MegaRAC target. Following successful exploitation, attackers can establish persistence, perform data exfiltration, perform lateral movement in the network, deploy malware, and more. Attackers can also perform a denial of service by forcing the server into a reboot loop or even bricking the system so it will no longer properly function.
Are updates available? #
AMI has made patched firmware available in versions SPx_12.4 and SPx_13.2. Admins should update MegaRAC BMCs to the newer firmware as soon as possible.
Eclypsium Research also shared mitigations to help reduce the chance of a successful attack, including:
- Ensuring all remote server management network interfaces are NOT exposed externally and operate on networks dedicated to management traffic only.
- Ensuring access to remote server management network interfaces is restricted to administrative users via ACLs or firewalls per Zero Trust Architecture principles.
Additionally, U.S. government agencies and contractors legally required to comply with CISA's Binding Operational Directive 23-02 should note required guidance to follow (similar to the aforementioned mitigation steps).
How do I find potentially vulnerable MegaRAC BMCs with runZero? #
From the Asset inventory, use the following prebuilt query to locate MegaRAC BMC instances in your network:
hw:megarac
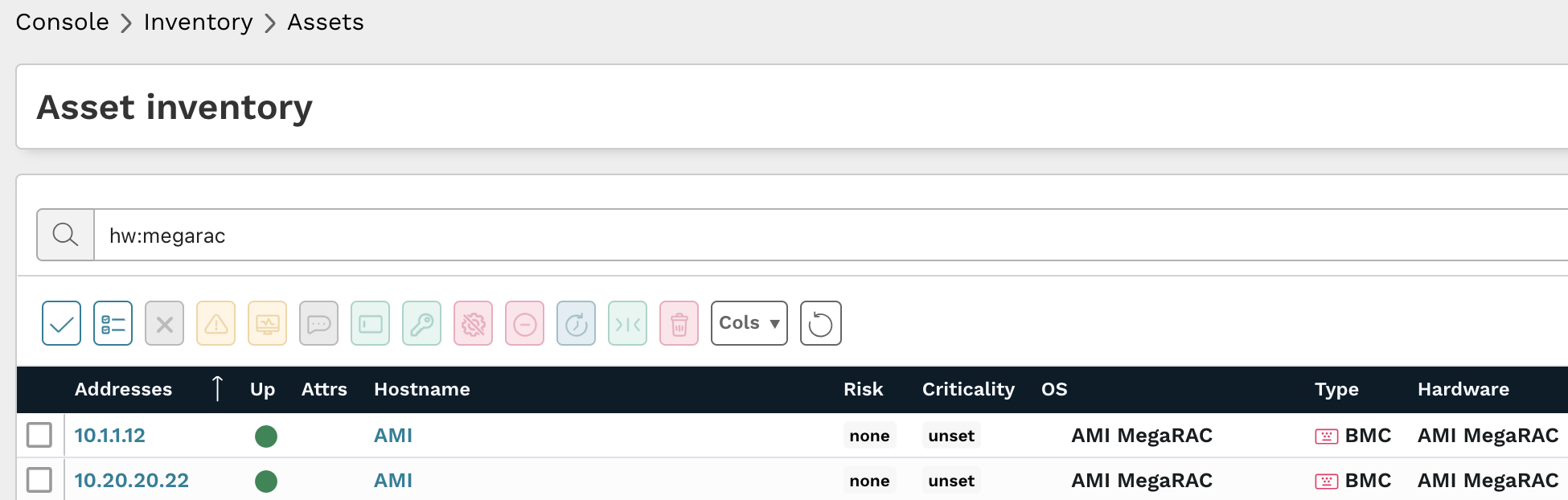
Results from the above query should be triaged to verify if those assets are running updated firmware versions.
As always, any prebuilt queries are available from your runZero console. Check out the documentation for other useful inventory queries.
Severe flaws in MegaRAC baseband management firmware impacted servers from AMD, ARM, HPE, Dell, others #
In December 2022, researchers with Eclypsium shared findings on three vulnerabilities present in American Megatrends (AMI) MegaRAC firmware.
MegaRAC can be found in many server manufacturers’ Baseboard Management Controllers (BMCs), including AMD, Ampere Computing, ASRock, Asus, ARM, Dell EMC, Gigabyte, HPE, Huawei, Inspur, Lenovo, Nvidia, Qualcomm, Quanta, and Tyan. Successful exploitation of these vulnerabilities can provide an attacker with remote code execution, an administrative shell, and user enumeration. Given American Megatrend’s broad reach across server manufacturers and models the number of systems with vulnerable MegaRAC BMC firmware could be quite large.
What was the impact? #
These vulnerabilities were scored as CVSS “critical” and “high” severities, and the reported vulnerability details include:
- CVE-2022-40259 (CVSS “critical” score of 9.9) - Remote code execution via Redfish API; requires initial access to an account with callback privileges or higher
- CVE-2022-40242 (CVSS “high” score of 8.3) - Administrative shell via default credentials
- CVE-2022-2827 (CVSS “high” score of 7.5) - User enumeration via API request manipulation
The Eclypsium report mentioned that public exposure of vulnerable BMCs appears to be “relatively low compared to recent high-profile vulnerabilities in other infrastructure products.” That said, data centers where many similar servers exist -– including data centers providing cloud-based resources -– could yield many opportunities for an attacker who has attained access, and detection of BMC exploitation can be “complex” and is likely to be missed with traditional EDR/AV.
Are updates available? #
Mitigations are offered in the Eclypsium report (see the “Mitigations” section), including (but not limited to) the following suggestions:
- Ensure that all remote server management interfaces (e.g. Redfish, IPMI) and BMC subsystems in their environments are on their dedicated management networks and are not exposed externally, and ensure internal BMC interface access is restricted to administrative users with ACLs or firewalls.
- Review vendor default configurations of device firmware to identify and disable built-in administrative accounts and/or use remote authentication where available.
How do I find MegaRAC BMC assets running MegaRAC firmware? #
From the Asset Inventory, use the following pre-built query to locate BMC assets running MegaRAC firmware which may need remediation:
type:"BMC" and (hw:"MegaRAC" or os:"MegaRAC")
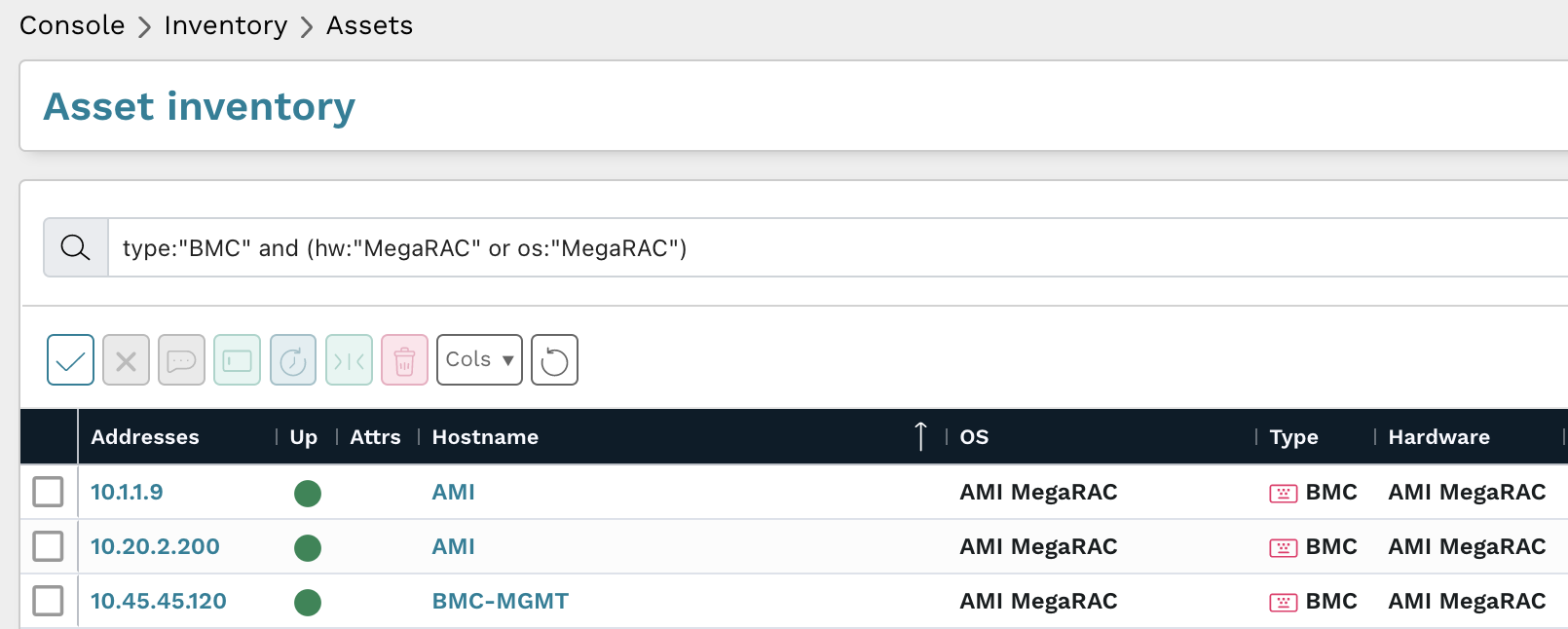
You can also locate all BMC assets in your environment by searching your Asset inventory for type:"BMC", which can then be triaged further.
As always, any prebuilt queries are available from our Queries Library. Check out the library for other useful inventory queries.
















