Latest Zabbix vulnerability #
Popular monitoring tool Zabbix surfaced in security news this week due to two newly disclosed vulnerabilities. Discovered by researchers at SonarSource, successful exploitation of vulnerable Zabbix Frontend targets could allow authentication bypass, configuration changes, privilege escalation, and code execution by attackers:
- CVE-2022-23131 (CVSS "critical" score of 9.8) - session data can be modified to bypass authentication, gain privilege escalation, and perform code execution
- CVE-2022-23134 (CVSS "medium" score of 5.3) - unauthenticated access to some steps of setup.php
While CVE-2022-23131 has a "critical" score, it should be noted that this vulnerability relies on SAML SSO authentication being enabled, which is a non-default setting, and that the attacker know the name of a user.
Meanwhile, CVE-2022-23134 exposes some steps of the setup.php file to unauthenticated users, allowing an attacker to change configuration of the Zabbix Frontend, which could have many different impacts based on attacker motivation.
Zabbix developers have released patches, and the researchers at SonarSource recommend that admins upgrade to Frontend versions 6.0.0beta2, 5.4.9, 5.0.19, or 4.0.37. If upgrading instances isn't possible in the near-term, Zabbix recommends disabling SSO (for CVE-2022-23131) and removing the setup.php file (for CVE-2022-23134) as mitigations.
How to find potentially vulnerable Zabbix instances with runZero #
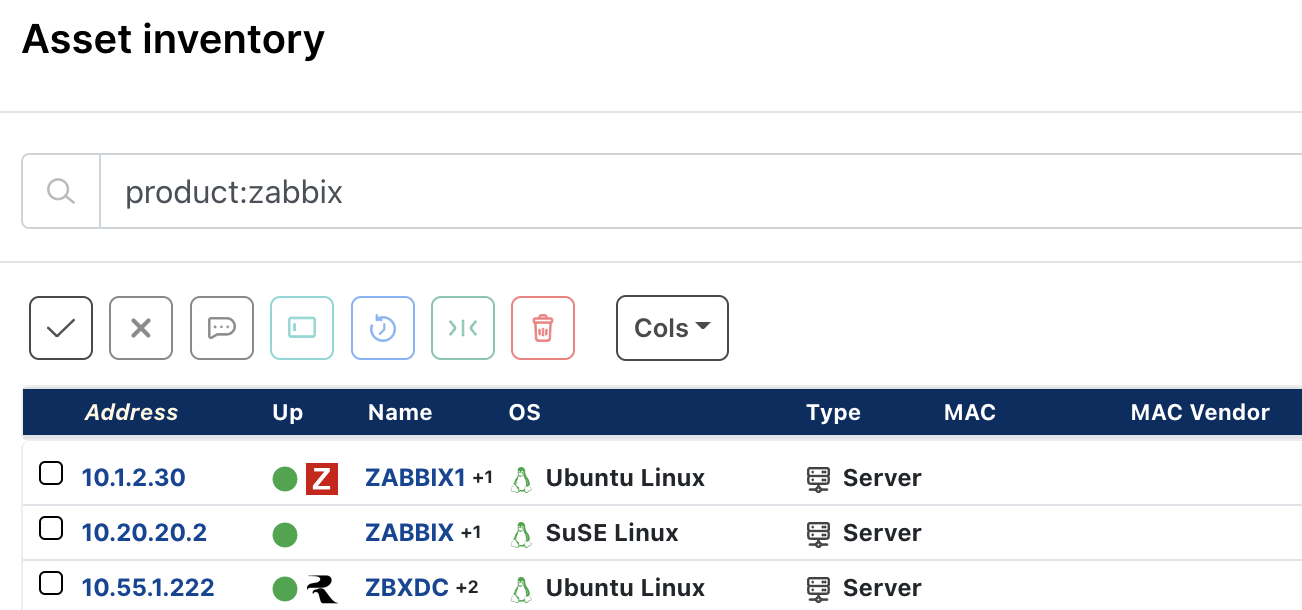
From the Asset Inventory, use the following pre-built query to locate Zabbix assets within your network that are potentially vulnerable:
product:zabbix
As always, any prebuilt queries we create are available from our Queries Library. Check out the library for other useful inventory queries.